Every year, more and more Americans are taking care of their holiday shopping on Cyber Monday.
Last year, consumers spent a record $6.59 billion during the annual online shopping day, an all-time record, according to Adobe Insights. Still, that doesn’t mean no one is rushing out the night of Thanksgiving to do their shopping. Shoppers still went out in droves on Black Friday last year — Adobe estimated that Americans spent $2.43 billion on Nov. 25, 2017.
These two frenzied days open the door for bad actors to take advantage, hoping to trick uneducated consumers into clicking on malicious ads (a.k.a. malvertising) and emails disguised as shopping deals to phish credit card and personal information. Last year, 71 percent of emails that mentioned either “Black Friday” or “Cyber Monday” by name were classified as spam by Cisco Talos. Of that spam, 96 percent of the emails came from uncommon top-level domains (TLDs) such as .top, .stream, .trade and .bid.
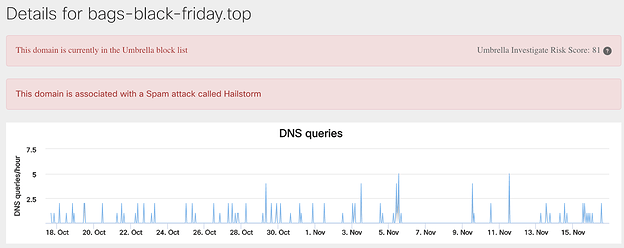
One of the most prevalent domains associated with these emails is hxxp://bags-black-friday[.]top, which utilized the “hailstorm” method. This means that the attacker registered many domains and use them to send hundreds of spam emails in a matter of minutes, only to never use those domains again. Since those domains have no history in detection software, they can easily blow by security systems and land in users’ inboxes. The Cisco Umbrella data for bags-black-friday is below.
Based on last year’s metrics, Talos believes that there will be a similar spike in these kinds of emails after the holiday shopping season kicks off.
Talos has also seen several malicious sites hoping to capitalize on Black Friday and Cyber Monday. We have blacklisted several sites that contain either “Black Friday” or “Cyber Monday” directly in the URL name, indicating that attackers are hoping to draw customers in who are looking for deals specific to those shopping days. A complete list of these domains is in the “IOCs” section below.
Some of these URLs reference popular stores that often run sales, such as J.C. Penney and Pandora jewelry. There are several other malicious URLs that mention these holidays but have been inactive for an extended period of time as of Nov. 14. As we get closer to Thanksgiving, we anticipate that the number of URLs targeted at shoppers will rise, as well. It is typical of attackers to set up these malicious sites just as the shopping days are arriving, hoping to show up in internet searches and bypass the usual detection, as with the email campaigns mentioned above.
There are also specific malware attacks that have tried to capitalize on these “holidays.” For example, Microsoft discovered a malware campaign in 2016 that disguised itself as a special deal from online retailer Amazon that downloaded the Locky ransomware onto victim’s machines. Locky is a ransomware that’s been spread for years, mainly through email campaigns. Once launched, the malware will encrypt users’ files and ask for a payment in order to return the files. However, the threat of Locky has largely been wiped out by antivirus detection engines over the past year. (If you happen to be infected with Locky, we have an open-source decryptor here called “LockyDump” that can help you recover your files.)
With these numbers in mind, Talos recommends that shoppers take the following advice when planning to shop on Black Friday and Cyber Monday to protect themselves from common scams:
Our customers can detect and block these kinds of threats, as well, through a variety of our products.
IOCs
americanas-seguranca-blackfriday[.]oni[.]cc
blackfriday-deal-uk[.]com
blackfriday-shoping[.]com
blackfriday-uk-deal[.]com
blackfridaydiscountmuch[.]com
blackfridayonlineshoping[.]com
blackfridaysofasale[.]com
centralatendimento-2016-blackfriday[.]com[.]br[.]fewori20.mobi
discount-blackfriday[.]shop
discountblackfriday[.]shop
downloadfileshere[.]com/get/odelldaigneault.nm.ru_black-friday_Downloader_8911010.exe
jcpenney[.]black[.]friday[.]sales[.]cybersmondaydeals.com
mariiusblog[.]blogspot[.]com/search/label/reduceri%20black%20friday%202014
pandora-blackfriday-deal[.]com
ricardoeletro-blackfriday[.]com[.]br[.]dosd23-0[.]mobi
sale-blackfriday[.]shop
saleblackfriday[.]shop
shopblackfriday[.]shop
ssl-dados-blackfriday-ricardoeletro[.]com[.]br[.]dsdkowie0930[.]net/produtos/32882479/PlayStation-3-250GB-HD-Controle-Dual-Shock-3-Preto-Sem-Fio-Produto-Oficial-Sony-Compacto-03-Super-Jogos
Uk-blackfriday[.]com
jcpenney[.]black[.]friday[.]sales[.]cybersmondaydeals[.]com
Last year, consumers spent a record $6.59 billion during the annual online shopping day, an all-time record, according to Adobe Insights. Still, that doesn’t mean no one is rushing out the night of Thanksgiving to do their shopping. Shoppers still went out in droves on Black Friday last year — Adobe estimated that Americans spent $2.43 billion on Nov. 25, 2017.
These two frenzied days open the door for bad actors to take advantage, hoping to trick uneducated consumers into clicking on malicious ads (a.k.a. malvertising) and emails disguised as shopping deals to phish credit card and personal information. Last year, 71 percent of emails that mentioned either “Black Friday” or “Cyber Monday” by name were classified as spam by Cisco Talos. Of that spam, 96 percent of the emails came from uncommon top-level domains (TLDs) such as .top, .stream, .trade and .bid.
One of the most prevalent domains associated with these emails is hxxp://bags-black-friday[.]top, which utilized the “hailstorm” method. This means that the attacker registered many domains and use them to send hundreds of spam emails in a matter of minutes, only to never use those domains again. Since those domains have no history in detection software, they can easily blow by security systems and land in users’ inboxes. The Cisco Umbrella data for bags-black-friday is below.
Based on last year’s metrics, Talos believes that there will be a similar spike in these kinds of emails after the holiday shopping season kicks off.
Talos has also seen several malicious sites hoping to capitalize on Black Friday and Cyber Monday. We have blacklisted several sites that contain either “Black Friday” or “Cyber Monday” directly in the URL name, indicating that attackers are hoping to draw customers in who are looking for deals specific to those shopping days. A complete list of these domains is in the “IOCs” section below.
Some of these URLs reference popular stores that often run sales, such as J.C. Penney and Pandora jewelry. There are several other malicious URLs that mention these holidays but have been inactive for an extended period of time as of Nov. 14. As we get closer to Thanksgiving, we anticipate that the number of URLs targeted at shoppers will rise, as well. It is typical of attackers to set up these malicious sites just as the shopping days are arriving, hoping to show up in internet searches and bypass the usual detection, as with the email campaigns mentioned above.
There are also specific malware attacks that have tried to capitalize on these “holidays.” For example, Microsoft discovered a malware campaign in 2016 that disguised itself as a special deal from online retailer Amazon that downloaded the Locky ransomware onto victim’s machines. Locky is a ransomware that’s been spread for years, mainly through email campaigns. Once launched, the malware will encrypt users’ files and ask for a payment in order to return the files. However, the threat of Locky has largely been wiped out by antivirus detection engines over the past year. (If you happen to be infected with Locky, we have an open-source decryptor here called “LockyDump” that can help you recover your files.)
With these numbers in mind, Talos recommends that shoppers take the following advice when planning to shop on Black Friday and Cyber Monday to protect themselves from common scams:
- Ensure that you are only downloading apps from trusted and official app stores like the Google Play store and iOS App Store.
- Look out for apps that ask for suspicious permissions, such as access to your text messages, contacts, stored passwords and administrative features.
- Some malicious apps will try to masquerade as a legitimate version of the one you could be searching for. Signs of these apps include poor spelling and grammar in app descriptions and interfaces, lack of high-quality performance and a developer contact that uses a free email service (such as @gmail.com).
- Avoid clicking on unsolicited emails. Make sure that you purposely subscribed to any marketing emails you are receiving from retailers.
- Do not click on any files from untrusted sources. These often contain files that will execute unwanted programs on your machine.
- Use an ad blocker locally on your browser. These will often block any malvertising campaigns that aim to capitalize on shoppers looking for deals.
- Try to use payment services such as Google Pay, Samsung Pay and Apple Pay. These services use tokenization instead of the “Primary Account Number” (your credit card number), making your transaction more secure.
- Use complex passwords that are unique, per site. Attackers commonly reuse passwords as a way to compromise multiple accounts with the same username.
- If a deal sounds too good to be true, it probably is.
Our customers can detect and block these kinds of threats, as well, through a variety of our products.
IOCs
americanas-seguranca-blackfriday[.]oni[.]cc
blackfriday-deal-uk[.]com
blackfriday-shoping[.]com
blackfriday-uk-deal[.]com
blackfridaydiscountmuch[.]com
blackfridayonlineshoping[.]com
blackfridaysofasale[.]com
centralatendimento-2016-blackfriday[.]com[.]br[.]fewori20.mobi
discount-blackfriday[.]shop
discountblackfriday[.]shop
downloadfileshere[.]com/get/odelldaigneault.nm.ru_black-friday_Downloader_8911010.exe
jcpenney[.]black[.]friday[.]sales[.]cybersmondaydeals.com
mariiusblog[.]blogspot[.]com/search/label/reduceri%20black%20friday%202014
pandora-blackfriday-deal[.]com
ricardoeletro-blackfriday[.]com[.]br[.]dosd23-0[.]mobi
sale-blackfriday[.]shop
saleblackfriday[.]shop
shopblackfriday[.]shop
ssl-dados-blackfriday-ricardoeletro[.]com[.]br[.]dsdkowie0930[.]net/produtos/32882479/PlayStation-3-250GB-HD-Controle-Dual-Shock-3-Preto-Sem-Fio-Produto-Oficial-Sony-Compacto-03-Super-Jogos
Uk-blackfriday[.]com
jcpenney[.]black[.]friday[.]sales[.]cybersmondaydeals[.]com
Article Link: http://feedproxy.google.com/~r/feedburner/Talos/~3/I_PPrec4k5Q/what-scams-shoppers-should-look-out-for.html