
The digital ocean on which many of us including the world’s largest corporations rely on, is filled with hidden dangers, particularly in the open-source ecosystem. One such peril that often does not get the attention it deserves is the threat posed by abandoned digital assets. These forgotten or ignored elements of our digital infrastructure, far from being harmless relics of the past, are attractive targets for cybercriminals. They transform these assets into Trojan horses, infiltrating and compromising the integrity of open-source ecosystems. This blog delves into several recent case studies that highlight the severity and prevalence of these threats
Key Points
- Abandoned digital assets are not relics of the past; they are ticking time bombs and attackers have been increasingly taking advantage of them, transforming them into trojan horses within the open-source ecosystems.
- MavenGate and CocoaPods case studies highlight how abandoned domains and subdomains could be hijacked to mislead users and spread malicious intent.
- Hijacking abandoned Rubygems package name case study emphasizes how abandoned package names could be hijacked and potentially used for malicious activities.
- Hijacking abandoned S3 buckets case study: The NPM package “bignum” is compromised through an abandoned S3 bucket, illustrating how attackers can stealthily replace necessary binaries with malicious ones.
- Email domain hijacking case study: Details the popular ‘ctx’ and ‘PHPass’ packages’ compromise due to reclaimed expired email domains.
- RepoJacking attack: Highlights a GitHub vulnerability where attackers hijack repositories by exploiting renamed usernames.
Mavengate: Hacker’s Ability to Leverage Abandoned Libraries to Hijack Java and Android Applications
An attack vector called MavenGate, revealed in January 2024, revealed a critical flaw in the way Maven-based technologies, including Gradle, manage dependencies.
This method enables attackers to hijack abandoned Java and Android libraries by acquiring expired domain names linked to these libraries.
Through those hijacked abandoned libraries, attackers could inject malicious code and potentially compromise the entire build process of projects that use those abandoned libraries as dependencies. This threat extended to all Maven-based technologies, including Gradle, affects a broad range of applications and services. And since the default build configurations of many projects do not account for this possibility. It leaves them open to undetected attacks.
Many Android and Java projects were found to be affected by the described problem including Companies like Google, Facebook, Amazon, Microsoft, Adobe, LinkedIn, Netflix, and over two hundred other companies.
Upon being notified of the issue, Sonatype, the owner of the mavenCentral repository, took action to address the problem. They blocked vulnerable dependencies and improved security in the Java ecosystem by implementing public key verification for uploaded artifacts. These actions will contribute to making the Java ecosystem a safer place.
Subdomain Hijacking: The CocoaPods Incident
In a notable cybersecurity incident, CocoaPods, a widely used dependency manager for iOS and Mac projects, faced a subdomain hijacking attack in 2023. In the CocoaPods incident, the attackers took control of the abandoned subdomain ‘cdn2[.]cocoapods[.]org,’ which still had DNS records pointing to GitHub Pages, and used it to host malicious content. This type of hijacking exploits forgotten settings on hosting platforms, with attackers using the reputation of legitimate domains to mislead users.
The following short demo video demonstrates this incident in action:
Hijacking Abandoned S3 Buckets
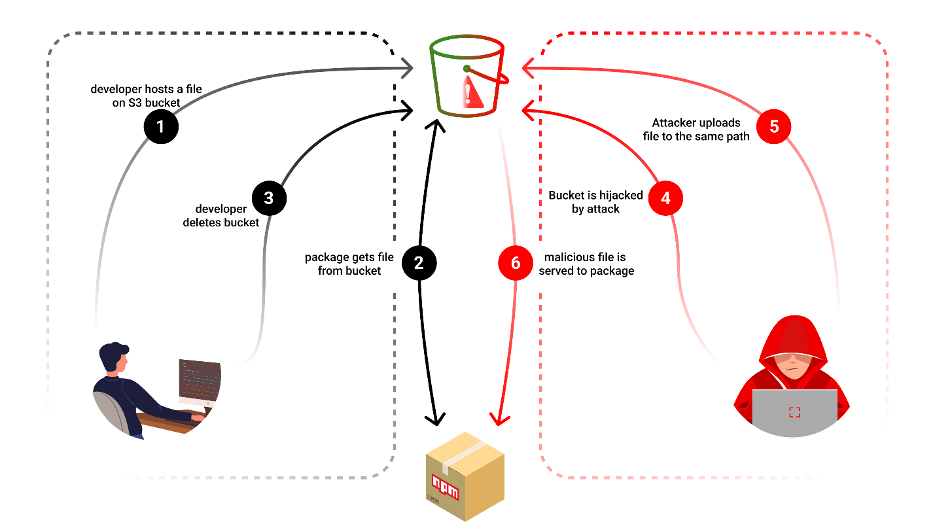
In a recent case of the NPM package “bignum,” in mid-2023, a significant security breach occurred through the hijacking of an S3 bucket. The attackers took control of an abandoned AWS S3 bucket previously used by the npm package, “bignum,” for storing binaries. They then replaced these binaries with malicious ones, effectively poisoning the package.
When users installed or re-installed “bignum,” they unknowingly downloaded these malicious binaries, which would ultimately steal the user IDs, passwords, local machine environment variables, and local hostname and then exfiltrate the stolen data to the hijacked S3 bucket.
Hijacking Abandoned Email Domains: The Case of ‘cox’ and ‘PHPass’
In May of 2022, the Python package ‘ctx’ and the PHP package ‘PHPass’ were compromised in a sophisticated cyber attack, leveraging a vulnerability in repository maintenance. Attackers identified popular open-source repositories managed through email addresses linked to expired domains. By re-registering these domains, they gained control over the email accounts, enabling them to reset passwords and assume ownership of the repositories. They then injected malicious code designed to steal environment variables, particularly targeting AWS credentials. This strategy led to a significant breach, with roughly 2,000 daily downloads of these packages for days before their removal.
RepoJacking: Hijacking Retired GitHub Namespaces
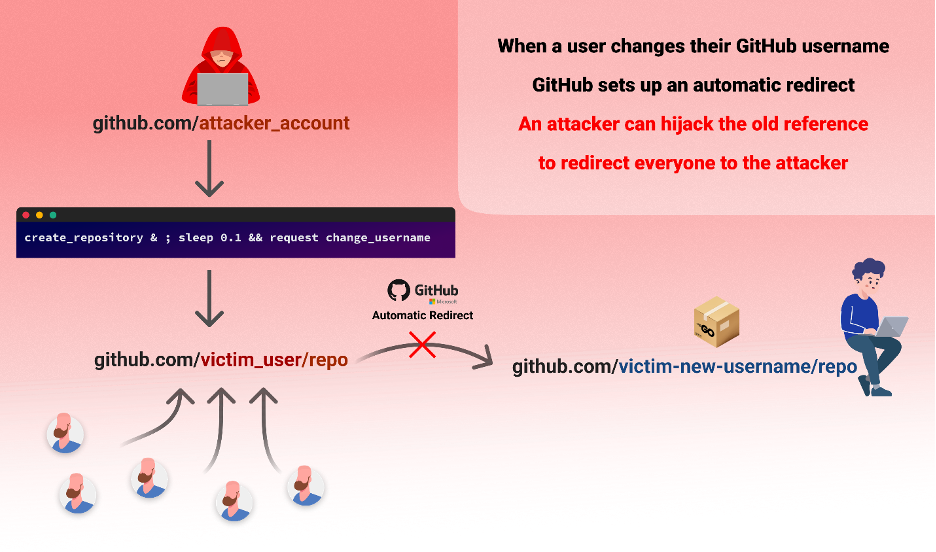
RepoJacking is a cybersecurity threat exploiting GitHub’s repository management system. This attack targets repositories whose usernames have been changed, a common occurrence when maintainers update their GitHub profiles. Attackers seize this opportunity by claiming the old, popular usernames and creating repositories with the same names. Users unknowingly download from these hijacked repositories, thinking they’re accessing trusted sources. This vulnerability allows attackers to distribute malicious code through seemingly reputable repositories.
The following short video demonstrates this case in more detail:
Hijacking Abandoned Open-Source Package Names: A RubyGems Package Takeover
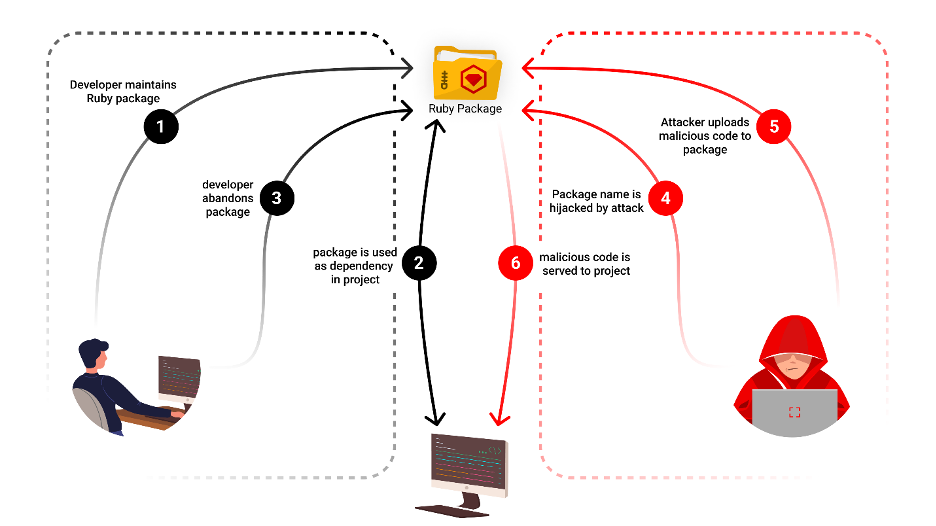
A recent case in the RubyGems ecosystem highlights the risk of attackers exploiting abandoned open-source package names to inject malicious content into software projects that depend on them.
The ‘gemnasium-gitlab-service’ gem package, which was initially created and maintained by Gemnasium and later by GitLab, was eventually abandoned. An unknown entity noticed this abandonment and claimed the name of the gem. This act posed a serious threat because projects that were using the gem, without updating their dependencies, might unknowingly incorporate this new version, mistaking it for a legitimate update from the original gem.
So, What Can Be Done About All This?
To address the risks associated with abandoned digital assets, it is essential for all stakeholders in the open-source community to take proactive steps to protect the integrity of software supply chains.
Developers and organizations are encouraged to remain vigilant and regularly monitor their projects for abandoned dependencies, both direct and transitive, especially within open-source ecosystems.
For maintainers, practicing diligent domain and email management in software maintenance is crucial to prevent similar attacks within the open-source community.
Conclusion
These case studies highlight the risks associated with abandoned digital assets and illustrate not only the creativity of attackers but also the fragility of our software supply chains.
For developers and organizations, these incidents underscore the critical need for vigilant monitoring and stringent security practices in dependency management.
As the open-source ecosystem continues to grow, so does the responsibility to safeguard it from such insidious threats.
Abandoned digital assets are not just dormant pieces of our digital past but ticking time bombs that could detonate with far-reaching consequences. The collective effort in the cybersecurity community towards awareness, proactive measures, and robust defensive strategies is the key to mitigating these hidden dangers and maintaining the integrity of the open-source ecosystem.
The post The Hidden Dangers of Abandoned Digital Assets in Open-Source Ecosystems appeared first on Checkmarx.com.
Article Link: Dangers of Abandoned Digital Assets in Open-Source Ecosystems