In the midst of the ongoing Israel-Palestine conflict, a notable upsurge of hacktivists collectives has emerged, announcing an unceasing barrage of digital assaults directed at a wide range of targets from both sides of the conflict.
This situation unfolds as a response to the ongoing Israel-Palestine conflict, which involves Palestinian militant groups led by Hamas initiating a large-scale offensive originating from the Gaza Strip and targeting Israel.
Although the cyber world sometimes seems like a stand-alone entity, it must be a reflection of the physical world, so just like the hacktivism resurgence that came with the Ukraine-Russia war, this sad conflict situation for humanity will also show an increasing business of war in the cyber world.
The Hacker Groups Involved in the Israel-Palestine Conflict
In the ongoing conflict, where the global landscape is split into two factions, NATO and Western-aligned nations often lean towards supporting Israel. Conversely, many countries in Asia tend to align themselves with the Palestinian cause. However, it is worth noting that some nations, like India, may adopt positions that diverge from their geographic affiliations. Both political alliances and geopolitical priorities influence this dynamic.
When we analyze these events through this lens, it becomes increasingly challenging to categorize countries definitively into one camp or the other. This complexity is even more pronounced in the realm of cyberspace. While hacktivist groups typically align with the political objectives of their home country, there are instances where they may adopt alternative stances.
| Pro-Israel Groups | Pro-Palestine Groups | Neutral Groups |
|---|---|---|
| VulzSec | KillNet | ThreatSec |
| Indian Cyber Force | Anonymous Sudan | Cyber Army Of Russia |
| UCC Team | UserSec | |
| Garuna Ops | Anonymous Russia | |
| SilentOne | Ghosts of Palestine | |
| IT ARMY of Ukraine | Team Azrael Angel of Death | |
| Dark Strom Team | ||
| Pakistani Leet Hackers | ||
| Sylhet Gang-SG | ||
| Team_insane_Pakistan | ||
| Hacktivism Indonesia | ||
| Garnesia Team | ||
| Blackshieldcrew MY | ||
| Gb Anon 17 | ||
| Anonymous Morocco | ||
| Ghost Clan Malaysia | ||
| Mysterious Team Bangladesh | ||
| Ganosec team | ||
| Moroccan Black Cyber Army | ||
| Muslim Cyber Army | ||
| GhostClan | ||
| Eagle Cyber Crew | ||
| Kerala Cyber Xtractors | ||
| YourAnon T13x | ||
| Team Herox | ||
| SynixCyberCrimeMY | ||
| Panoc team | ||
| 4 Exploitation | ||
| Team R70 | ||
| Stucx Team | ||
| The White Crew | ||
| Cscrew | ||
| TYG Team | ||
| Hizbullah Cyb3r Team | ||
| Electronic Tigers Unit | ||
| StarsX Team |
Hacktivist Dynamics
The abundance of pro-Palestinian hacktivists can be attributed to one primary factor: Hacktivism enjoys greater popularity in the Eastern hemisphere. When examining the landscape, it becomes apparent that even pro-Israel groups have their origins in Asia.
Notably, significant hacktivist collectives like KillNet and Anonymous Sudan have not only drawn numerous followers but have also significantly inflated this number, leading to considerable disruptions. KillNet, a pro-Russian hacking collective, justified its actions against Israel by referencing Israel’s support for Ukraine in 2022, which Russia perceived as a betrayal and this also applies to many pro-Russian groups.
Anonymous Sudan, highly suspected of having Russian support, targeted Israeli alert systems, claiming responsibility for disrupting Israel’s Tzeva Adom early warning radar system and launching a DDoS attack on the Jerusalem Post news service.
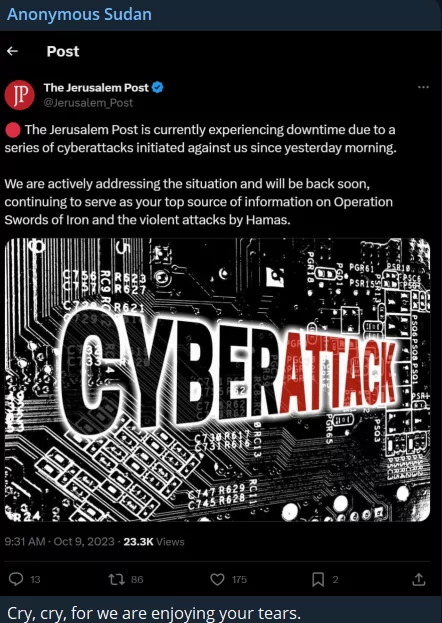 Anonymous Sudan’s Post on Telegram
Anonymous Sudan’s Post on Telegram
Groups with Islamic tendencies gather on the Palestinian side. Furthermore, one of Stucx Team’s claims is that they hacked an Israeli SCADA system’s website.
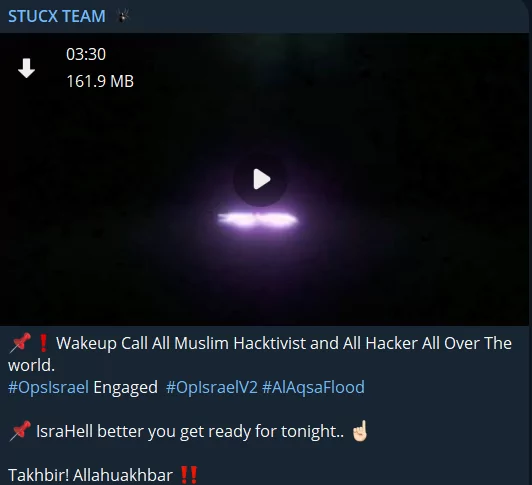 Stucx Team’s Post on Telegram
Stucx Team’s Post on Telegram
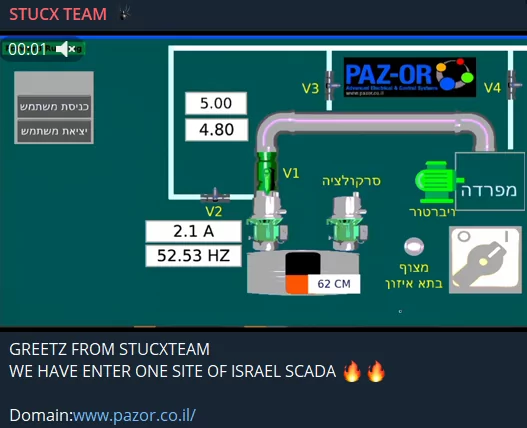 Stucx’s claim about Israeli Scada
Stucx’s claim about Israeli Scada
On the Israeli side, Indian hacktivist groups stand out, and it should be stressed that they call on non-Muslim hackers in the UCC’s and Garuna Ops’ post to take action for an anti-Palestinian stance.
 UCC’s Post on Telegram
UCC’s Post on Telegram
Not every group with Russian origin has taken a completely anti-Israeli stance yet. The Cyber Army of Russia consults its users on what stance it should take, as seen in the figure below.
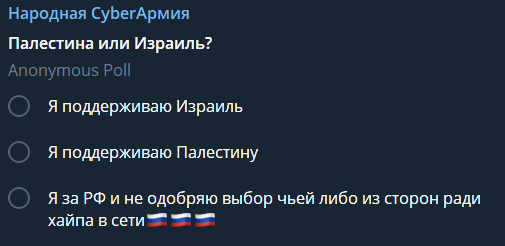 Cyber Army of Russia’s Post on Telegram
Cyber Army of Russia’s Post on Telegram
Some groups are just looking for chaos, with Five Families member ThreatSec stating that they are not on any side, but adding that they will still target Israel.
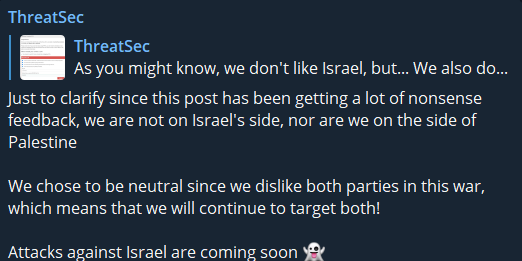 ThreatSec’s Post On Telegram
ThreatSec’s Post On Telegram
The IT Army of Ukraine posted a message stating it is on Israel’s side, but it does not look like they will take action.
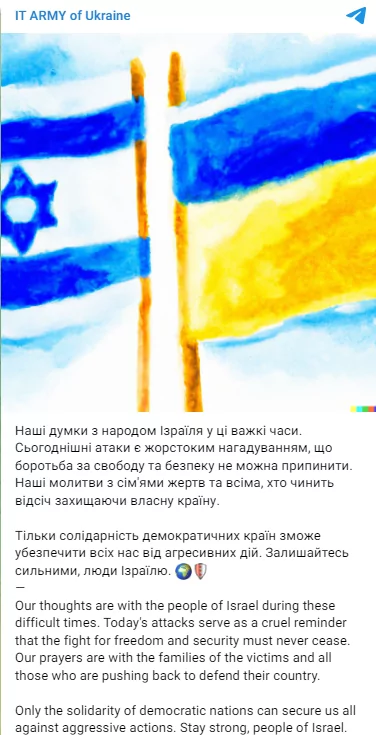 IT Army of Ukraine’s post on Telegram
IT Army of Ukraine’s post on Telegram
Track Telegram with SOCRadar
With SOCRadar’s Cyber Threat Intelligence and Digital Risk Protection modules, you can effortlessly keep a constant watch on threat actor activities in Telegram channels.
SOCRadar’s Digital Risk Protection module makes it simple to monitor the actions of threat actors. The Dark Web Monitoring tab automatically provides pertinent information about products and technologies discovered within your digital assets. Conversely, Dark Web News shares significant updates from deep and dark web forums, social media platforms, and communication channels like Telegram, complete with screenshots and textual content.
 SOCRadar Labs, DoS Resilience
SOCRadar Labs, DoS Resilience
You can also use SOCRadar Labs to measure your resistance to DoS attacks, which are the popular attack methods of hacktivist groups.
Discover whether your data is at risk from threat actors and take steps to mitigate these risks in your digital assets. SOCRadar conducts routine internet scans to identify new Telegram groups where your company’s leaked data may be found. Moreover, it promptly alerts you to any information related to your organization.
The post Reflections of the Israel-Palestine Conflict on the Cyber World appeared first on SOCRadar® Cyber Intelligence Inc..
Article Link: Reflections of the Israel-Palestine Conflict on the Cyber World
