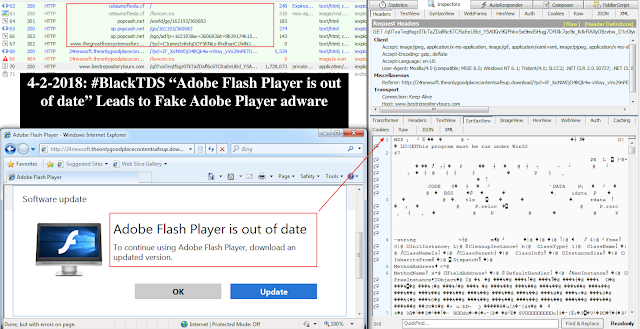
Goal: Review and document latest BlackTDS traffic distribution leading to fake Adobe Flash Player and its social engineering theme.
Background
Traffic chain4-2-2018: Drive-by: #BlackTDS social engineering theme— Vitali Kremez (@VK_Intel) April 2, 2018
“Adobe Flash Player is out of date”
(24newsoft.theonlygoodplacecontentsafeup[.download)
-> Leads to fake Adobe Flash Player #adware
Watch out for unofficial Adobe Flash installs #Malware: https://t.co/4P7XD8PE27 pic.twitter.com/pZWkaBFsSG
I. BlackTDS domain redirect hxxp://celsiumoftesla[.]cf:
<style> html, body { margin: 0; padding: 0; height : 100%; } </style>
<script type=“text/javascript”> </script>
<iframe src=“” style=“display:block; width:100%; height:100%; border:none; margin:0; padding:0;”></iframe><span style=“visibility: hidden”><a href=“/insert”><VALUE</a><a href=“/register”><VALUE></a></span>
<script type=“text/javascript”> </script>
<iframe src=“” style=“display:block; width:100%; height:100%; border:none; margin:0; padding:0;”></iframe><span style=“visibility: hidden”><a href=“/insert”><VALUE</a><a href=“/register”><VALUE></a></span>
II. Popunder domain redirect using hidden /register with hidden visibility.
hxxp://popcash[.]net/world/go/162193/360683
hxxp://popcash[.]net/world/go/162193/360683
III. Popunder redirect
hxxp://www[.]thegreatfreesystemosforcontenting[.]date/?pcl=<VAL>&subid=<VAL>
IV. Fake “Adobe Flash Player” adware redirect:
IV. Fake “Adobe Flash Player” adware redirect:
Domain: hxxp://24newsoft[.]theonlygoodplacecontentsafeup[.]download/?pcl=&subid=&v_id=
V. Fake “Adobe Flash Player” adware download:
Domain: hxxp://www.bestrepositorytours[.]com/<REDACTED>
Domain: hxxp://www.bestrepositorytours[.]com/<REDACTED>
Addendum: Indicators of Compromise (IOCs):
Domain:
- Domain: hxxp://celsiumoftesla[.]cf/
Popunder:
- Domain: hxxp://popcash[.]net/world/go/162193/360683
Popunder redirect:
- Domain: hxxp://www[.]thegreatfreesystemosforcontenting[.]date/?pcl=<VAL>&subid=<VAL>
Fake Adobe Flash Player Adware Redirect:
- Domain: hxxp://24newsoft[.]theonlygoodplacecontentsafeup[.]download/?pcl=&subid=&v_id=
Fake Adobe Flash Player Adware Download:
- Domain: hxxp://www.bestrepositorytours[.]com/<REDACTED>
Fake Adobe Flash Player Adware:
- MD5: 69708785506cf581ea5f81725bdb849b
Article Link: http://www.vkremez.com/2018/04/malware-traffic-internals-blacktds.html