Introduction
- A Chinese Ministry of Public Security (MPS) contractor called iSOON (also known as Anxun Information) that specializes in network penetration research and related services has had its data leaked to GitHub.
- Preliminary findings from less than one week since the leak revealed that it contains unprecedented insights into how the Chinese MPS operates by using Chinese commercial surveillance vendors and what their technical capabilities are.
- The Chinese MPS is China’s internal security service that primarily focuses on internal and border security, counter-terrorism, surveillance. The MPS is comparable to the Russian FSB, the US DHS or the UK’s MI5.
- The most interesting findings have come from iSOON’s product whitepapers and confidential slide deck presentations given to their MPS clients.
About the iSOON Leak
The iSOON leak has revolutionized the open source intelligence (OSINT) community's general understanding of the Chinese MPS' cyber operations. Its significance is comparable to the NTC Vulkan leak that impacted the Russian military intelligence (GRC) and Russian federal security service (FSB) as well as the Snowden Leak or the Shadow Brokers Leak, both of which impacted the US National Security Agency (NSA).
The leak is around 170MB and contains images of documents in Mandarin. They were machine translated to English for this blog. Therefore, not all of the facts will be available for a some time as the community digs in and there may be some misunderstandings in this blog due to not being a Chinese-speaking analyst myself.
The company, iSOON has had a long development history. Established in 2010, iSOON has been involved in various activities related to "network penetration research" and "overseas special case network work" and has conducted national training programs on network security. They have received commendations from CCP ministerial and central leaders for their contributions. In 2019, iSOON was selected as one of the first units installed by the Cyber Security Bureau of the MPS.
On 16 February 2024, a GitHub repository ("github[.]com/I-S00N/I-S00N") containing the data dumped from iSOON was uploaded to the site by an unknown source:
iSOON's Services
According to an iSOON presentation in the leak, the structure of firm includes three penetration teams, one security research team, and one basic support team, comprising a total of around 70 people.
Their primary targets are countries and regions such as Central Asia, Southeast Asia, Hong Kong, Macao, and Taiwan. iSOON offers services such as "APT Service System," "Target Penetration Services," and "Battle Support Services" to their MPS clients.
They have also reportedly targeted various regions in China, including Xinjiang and Tibet, which includes dissidents, illegal gambling rings, illegal pornography rings, as well as illegal pyramid schemes (which all come under MPS jurisdiction).
Notably, iSOON featured in a slide deck their attacks on the Indian and Nepalese governments, targeting government departments such as the Ministry of Foreign Affairs, Defense, Home Affairs, Finance, and the Nepalese Presidential Palace.
iSOON's Victims
Fellow security researcher @azakasekai_ also was first to find that the leak contains conversations and spreadsheets about iSOON’s victims, including how many terabytes of data has been exfiltrated from certain government entities, telecommunications firms, medical organizations, and academic sectors of countries such as: Pakistan, Kazakhstan, Kyrgyzstan, Malaysia, Mongolia, Nepal, Turkey, India, Egypt, France, Cambodia, Rwanda, Nigeria, Hong Kong, Indonesia, Vietnam, Myanmar, Philippines, and Afghanistan.
Examples of some of the victim organizations include:
- Ministry of Foreign Affairs, Myanmar
- National Taiwan University Hospital
- Tamkang University, Taiwan
- National Intelligence Agency, Thailand
- Ministry of Foreign Affairs, Thailand
- Ministry of Health, Rwanda
- Apollo Hospital, India
- Punjab Anti-Terrorism Center, Pakistan
- Beeline Communications, Kazakhstan
- Tele2 Communications, Kazakhstan
- Skytel Communications, Mongolia
- Ministry of Public Security, Mongolia
- Nepal Telecom
- Chinese University of Hong Kong
- Hong Kong Shue Yan University
- Tung Wah College, Hong Kong
- Paris Institute of Political Studies, France
The Twitter Tool whitepaper also showed in detail how the Chinese intelligence services access Western social media services and bypassing the Great Firewall of China. The platform enabled the Chinese MPS to view tweets and Twitter account profiles of target dissidents. The Chinese MPS operators using the iSOON platform could obtain "evidence" using the collection system in the platform, which involves indexing content from Twitter users criticizing the Chinese government.
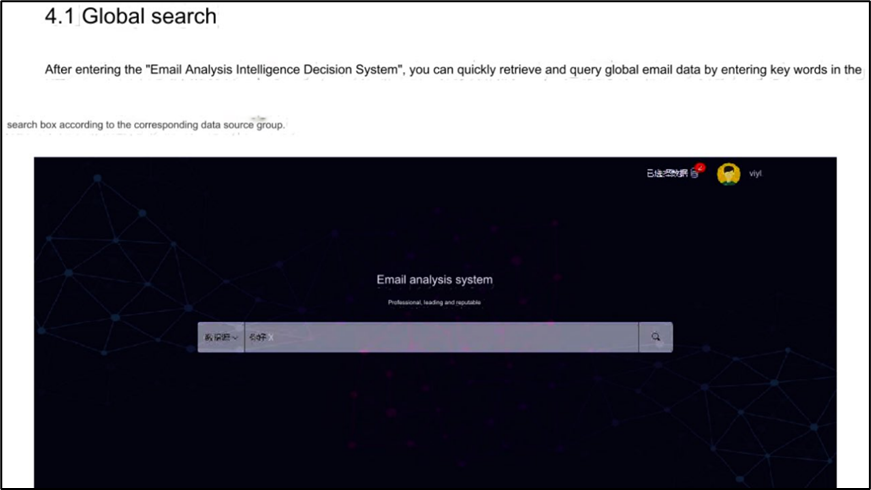
The Email Tool whitepaper included the architecture of the system that enables mass email data analysis using machine learning (ML) algorithms, optical character recognition (OCR), and other methodologies.
One of the notable screenshots from the Email Tool whitepaper showed that the platform can also enable MPS operators to recreate their target’s inbox and read through their stolen emails
- An iSOON Revengeful Ex-Employee
- A rival Chinese Contractor
- A rival Chinese Agency to the MPS
- A Foreign Intelligence Agency
- An Anti-CCP Hacktivists
- Chinese Cybercriminals
- The original thread by Azaka: https://twitter.com/AzakaSekai_/status/1759326049262019025
- The Associated Press' investigation: https://apnews.com/article/china-cybersecurity-leak-document-dump-spying-aac38c75f268b72910a94881ccbb77cb
- The AP journalist's thread: https://twitter.com/dakekang/status/1760497207013241189
- MemeticWarfare Summary: https://memeticwarfareweekly.substack.com/p/memetic-warfare-weekly-my-data-leaks
- Kris McConkey's Thread on Red Scylla: https://twitter.com/smoothimpact/status/1760636928716689784
- Mark Kelly's Thread on Red Hotel: https://twitter.com/markkelly0x/status/1760408290255663170
- Dakota Cary's analysis: https://twitter.com/DakotaInDC/status/1760347298494599197
Article Link: Lessons from the iSOON Leaks