Obinwanne Okeke: The Entrepreneur
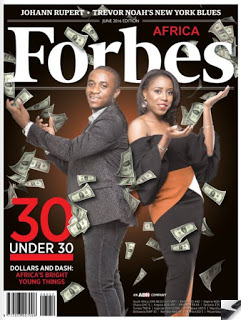
Obinwanne Okeke, 31 year old CEO and Founder of Invictus Group, is frequently lauded as a success story. At age 28, Forbes Africa featured him in their June 2016 issue under the title "Africa's Most Promising Entrepreneurs: Forbes Africa's 30 Under 30 for 2016".Although the 30 are “in no particular order”, Obinwanne was one of the two selected to appear on the cover of that month’s Forbes Africa:
The Forbes profile described Okeke like this:
Okeke could not fail his mother. A promise meant hard work and dreaming big. He was raised in Ukpor village, 790 kilometers from Nigeria’s capital, Abuja, as the 17th child of a polygamous father. He went to boarding school aged 10, lost his father at 16 and moved from one relative to another. He named his company Invictus after one of Nelson Mandela’s favorite a poems, by William Ernest Henley, about the undefeated and unconquerable soul of a hard worker, from an impoverished background, who will not give up.
Invictus is in construction, agriculture, oil and gas, telecoms and real estate. He has 28 permanent and 100 part-time employees across nine companies.
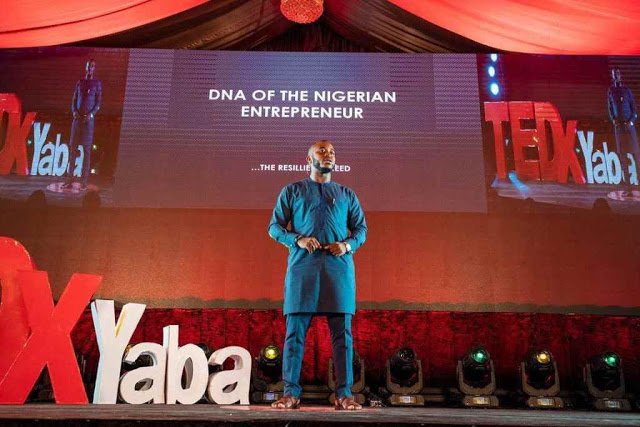
He was also selected to speak at the Lagos TEDx Yaba conference, where his topic was “DNA of the Nigerian Entrepreneur … The Resilience Needed” (photo from his company website - invictus.com.ng):
|
|
| Invictus.com.ng |
|
|
| Full interview at BBC Africa’s Facebook page |
Obinwanne Okeke: The BEC Criminal / Yahoo Boy
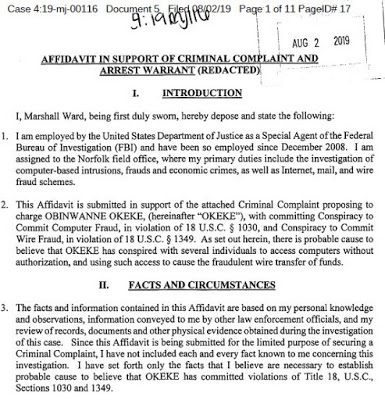
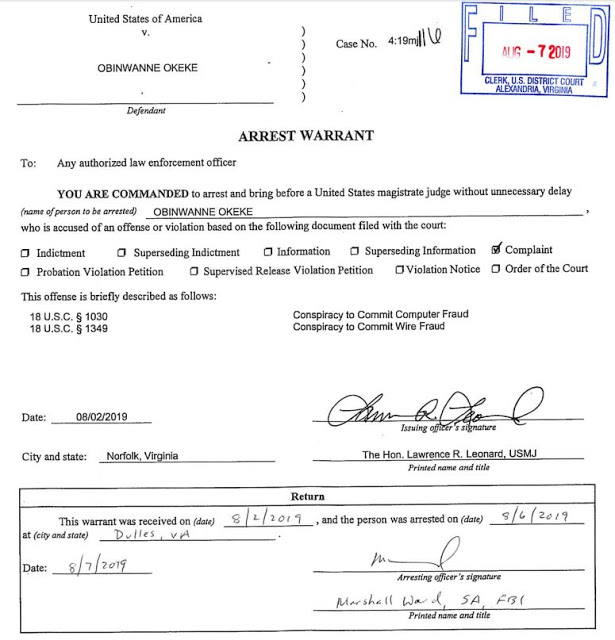
According to court records available on PACER, Okeke was arrested in Dulles, Virginia on August 6, 2019. Let’s just walk through the Criminal Complaint that was used to justify the arrest warrant:
Okeke was charged with Conspiracy to Commit Computer Fraud and Wire Fraud. (18 USC section 1030 and 1349.)
In June 2018, Unatrac Holding Limited, the export sales office for Caterpillar heavy industrial and farm equipment, headquartered in the UK, contacted the FBI, reporting that Unatrac ad been scammed out of $11 Million USD. Unatrac’s Chief Financial Officer fell for a phishing email that contained a login link to a fake Microsoft Office365 website. When the CFO entered his userid and password, it was sent to the criminals. Between April 6 and April 20, 2018, the CFO’s account was logged into from IP addresses mostly in Nigeria on 464 different occasions.
One key behavior of recent BEC scams was also present in this one. On seven different occasions, someone modified Outlook Office365 rules to intercept legitimate emails to and from employees on the financial teams, mark them as “read” and move them to another folder outside the in box. The complaint says “These rules appeared to have been created in an attempt to hide from the CFO any responses from the individuals to whom the intruder was sending fabricated emails.“
With full access to the CFO’s accounts, the intruders stole invoices, invoice templates, and logos, and used them to create fraudulent invoices, sent from external addresses to the CFO, and then forwarded “by the CFO” to the financial team for payment. One such example email was received on April 19, 2018 from [email protected]. The email was forwarded two minutes later to the finance team with instructions to pay.
From April 11 through April 19th, they paid 15 fraudulent payments, included three invoices for “Pak Fei Trade Limited” in the amounts of $278,270.66, $898,461.17, and $1,957,100.00. Altogether, $11 million USD was sent out of the company.
Documents related to the CFO’s travel schedule and the companies tax filings were also stolen, forwarded to the email address "[email protected].” WHOIS queries run by the FBI indicated that the email address was used to create fraudulent “clones” of real companies websites. One example they give is of “emmarlndustries.com” – where the “I” in Industries is actually a lowercase “L”. The real company is a domain owned by ASM International Trading in Dubai. Other domains, not mentioned in the affidavit, but also registered by this address, include “hmlsho-group.com” and “western-chem.net” and “.com”.
Search warrants for the email addresses of iconoclast1960 revealed additional frauds, including a $108,470.55 payment received by the Red Wing Shoe Company in Minnesota. They were victimized in a very similar way. More than 600 additional phished userids and passwords were recovered in the gmail, along with photos of passports and driver’s licenses.
Chats between iconoclast1960 and others dating from December 2017 to November 2018 reveal the scammer interacting with people who are making his phishing sites for him, including a Docusign phishing site. The iconoclast1960 email account also sent and received emails containing phishing kits, such as one called “microsoft.zip” where the file “verify.php” contained code to email stolen credentials to a redacted email address.
The iconoclast1960 gmail account used a recovery email address of "[email protected]”. This address shared a login session cookie with several additional accounts, including "[email protected]". This means that the person who logged in to Gmail as “alibabaobi” had also logged in to Gmail, from the same computer, using the Gmail account “obinwannem”.
The Obinwannem gmail account also belongs to the Nairaland.com user “InvictusObi” and to the Twitter user “@invictusobi.” The Twitter page provides repeated links to an Instagram account for InvictusObi as well. Both the Twitter and Instagram page provide many proofs that these accounts belong to Obinwanne Okeke, the CEO of Invictus Group.
Gmail, Twitter, and Instagram all log the IP addresses from which users access their accounts. When Okeke posted on Instagram that he was visiting Seychelles, Google’s logs showed that iconoclast1960@gmail was logging in from 197.157.125.89, in Seychelles. When Okeke was posting on Instagram that he was visiting London on April 20, 2018, the iconoclast1960@gmail account was logging in from 167.98.28.227. When Okeke said he was visiting the United States, specifically Washington, DC, the iconoclast1960@gmail account was logging in from 68.33.78.173, a ComCast IP address in Washington, DC.
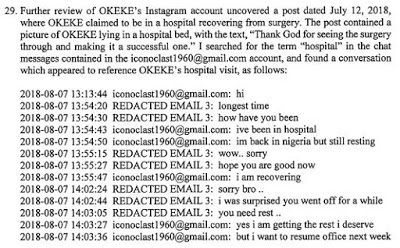
For further evidence, Okeke posted information that he had been hospitalized following a recovery from surgery. The FBI agents searched the Google chat logs for Iconoclast1960 and found that he was mentioning in the chats "ive been in hospital. im back in nigeria but still resting.
The FBI agent also found multiple instances where the iconoclast1960 gmail account forwarded emails with attachments to the [email protected] account. Search warrants were also conducted for that account, as well as obinwannem@gmail and alibabaobi@gmail.
Searches through older FBI case files show additional previous frauds conducted in the same manner using the same email addresses, dating all the way back to 2015.
The FBI agent ended his affidavit by showing that Obinwanne Okeke has a Nigerian Passport A50254005 and uses a Visa for entry to the United States “once or twice a year.” He was currently in the country, scheduled to depart on August 6, 2019.
Presumably that is how they knew where to find him at Dulles Airport in Virginia to arrest him as he attempted to leave the country. That must have been a nice collar for the FBI agent who had spent all that time investigating to be able to pick him up in person!
Article Link: http://garwarner.blogspot.com/2019/08/lauded-nigerian-entrepreneur-may-be-bec.html