Automation services are steadily becoming significant drivers of modern IT, helping improve efficiency and cost effectiveness for organizations. A recent McKinsey survey discovered that “the majority of all respondents (57 percent) say their organizations are at least piloting the automation of processes in one or more business units or functions. Another 38 percent say their organizations have not begun to automate business processes, but nearly half of them say their organizations plan to do so within the next year.”
Automation is no longer a theme of the future, but a necessity of the present, playing a key role in a growing number of IT and user scenarios. As security professionals, you’ll need to recommend an automation service that enables your organization to reap its benefits without sacrificing on strict security and compliance standards.
In our two-part series, we share how Microsoft delivers on the promise of empowering a secure, compliant, and automated organization. In part 1, we provide a quick intro into Microsoft Flow and provide an overview into its best-in-class, secure infrastructure. In part 2, we go deeper into how Flow secures your users and data, as well as enhances the IT experience. We also cover Flow’s privacy and certifications to give you a glimpse into the rigorous compliance protocols the service supports. Let’s get started by introducing you to Flow.
To support the need for secure and compliant automation, Microsoft launched Flow. With Flow, organizations will experience:
- Seamlessly integrated automation at scale.
- Accelerated productivity.
- Secure and compliant automation.
Secure and compliant automation is perhaps the most interesting value of Flow for this audience, but let’s discuss the first two benefits before diving into the third.
Integrated automation at scale
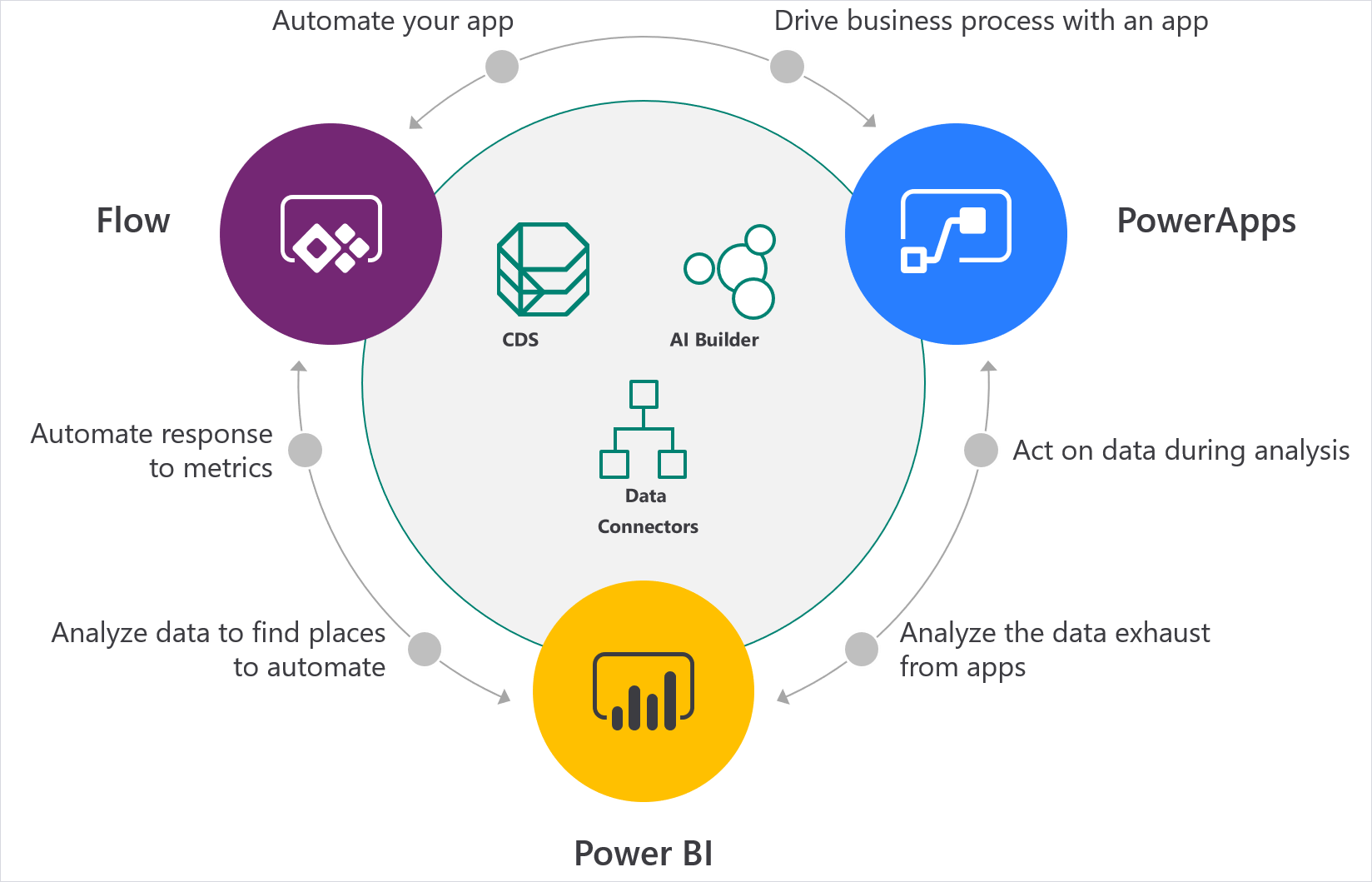
Flow is a Software as a Service (SaaS) automation service used by customers ranging from large enterprises, such as Virgin Atlantic, to smaller organizations, such as G&J Pepsi. Importantly, Flow serves as a foundational pillar for the Microsoft Power Platform, a seamlessly integrated, low-code development platform enabling easier and quicker application development. With Power Platform, organizations analyze data with Power BI, act on data through Microsoft PowerApps, and automate processes using Flow (Figure 1).
Figure 1. Power Platform offers a seamless loop to deliver your business goals.
Low-code platforms can help scale IT capabilities to create a broader range of application developers—from the citizen to pro developer (Figure 2). With growing burdens on IT, scaling IT through citizen developers who design their own business applications, is a tremendous advantage. Flow is also differentiated from all other automated services because of its native integration with Microsoft 365, Dynamics 365, and Azure.
Figure 2. Low-code development platforms empower everyone to become a developer, from the citizen developer to the pro developer.
Accelerated productivity
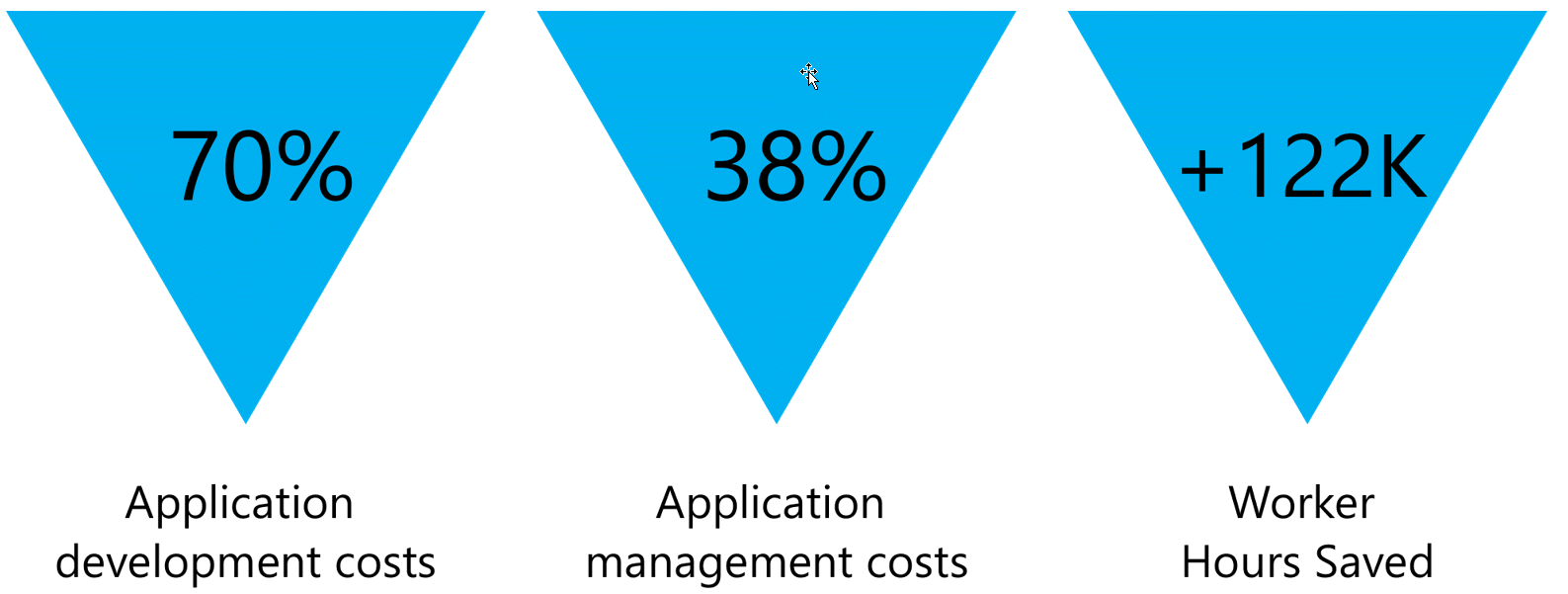
Flow accelerates your organization’s productivity. The productivity benefits from Flow were recently quantified in a Total Economic Impact (TEI) study conducted by Forrester Research and commissioned by Microsoft (The Total Economic Impact Of PowerApps And Microsoft Flow, June 2018). Forrester determined that over a three-year period Flow helped organizations reduce application development and application management costs while saving thousands of employee hours (Figure 3).
Figure 3. Forrester TEI study results on the reduced application development and management costs and total worker hours saved.
Built with security and compliance
Automation will be the backbone for efficiency across much of your IT environment, so choosing the right service can have enormous impact on delivering the best business outcomes. As a security professional, you must ultimately select the service which best balances the benefits from automation with the rigorous security and compliance requirements of your organization. Let’s now dive into how Flow is built on a foundation of security and compliance, so that selecting Flow as your automation service is an easy decision.
A secure infrastructure
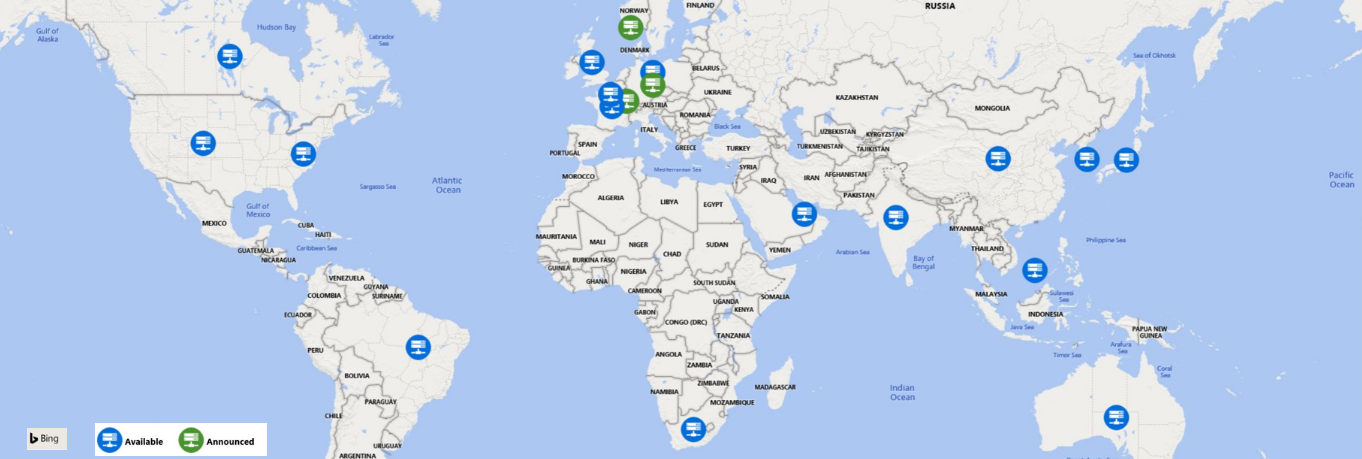
Comprehensive security accounts for a wide variety of attack vectors, and since Flow is a SaaS offering, infrastructure security is an important component and where we’ll start. Flow is a global service deployed in datacenters across the world (Figure 4). Security begins with the physical datacenter, which includes perimeter fencing, video cameras, security personnel, secure entrances, and real-time communications networks—continuing from every area of the facility to each server unit. To learn more about how our datacenters are secured, take a virtual tour.
The physical security is complemented with threat management of our cloud ecosystem. Microsoft security teams leverage sophisticated data analytics and machine learning and continuously pen-test against distributed-denial-of-service (DDoS) attacks and other intrusions.
Flow also has the luxury of being the only automation service natively built on Azure which has an architecture designed to secure and protect data. Each datacenter deployment of Flow consists of two clusters:
- Web Front End (WFE) cluster—A user connects to the WFE before accessing any information in Flow. Servers in the WFE cluster authenticate users with Azure Active Directory (Azure AD), which stores user identities and authorizes access to data. Azure Traffic Manager finds the nearest Flow deployment, and that WFE cluster manages sign-in and authentication.
- Backend cluster—All subsequent activity and access to data is handled through the back-end cluster. It manages dashboards, visualizations, datasets, reports, data storage, data connections, and data refresh activities. The backend cluster hosts many roles, including Azure API Management, Gateway, Presentation, Data, Background Job Processing, and Data Movement.
Users directly interact only with the Gateway role and Azure API Management, which are accessible through the internet. These roles perform authentication, authorization, distributed denial-of-service (DDoS) protection, bandwidth throttling, load balancing, routing, and other security, performance, and availability functions. There is a distinction between roles users can access and roles only accessible by the system.
Stay tuned for part 2 of our series where we’ll go deeper into how Flow further secures authentication of your users and data, and enhances the IT experience, all while aligning to several regulatory frameworks.
Figure 4. Microsoft’s global datacenter locations.
Let Flow enhance your digital transformation
Let your organization start benefiting from one of the most powerful and secure automation services available on the market. Watch the video and follow the instructions to get started with Flow. Be sure to join the growing Flow community and participate in discussions, provide insights, and even influence product roadmap. Also, follow the Flow blog to get news on the latest Flow updates and read our white paper on best practices for deploying Flow in your organization. Be sure to check out part 2 where we dive deeper into how Flow offers the best and broadest security and compliance foundation for any automation service available in the market.
Additional resources
- Sign up for Microsoft Flow—just click or tap Sign up free in the upper-right corner.
- Visit the Flow community to connect with peers, share ideas, and learn from experts.
- Read the Flow blog to get the latest news.
- Read Administering a PowerApps enterprise deployment technical white paper.
- Watch the Microsoft Flow: Getting Started video.
The post Foundations of Microsoft Flow—secure and compliant automation, part 1 appeared first on Microsoft Security.
Article Link: https://www.microsoft.com/security/blog/2019/09/05/foundations-of-microsoft-flow-secure-compliant-automation-part-1/