Since late 2023, Microsoft has observed an increase in reports of attacks focusing on internet-exposed, poorly secured operational technology (OT) devices. Internet-exposed OT equipment in water and wastewater systems (WWS) in the US were targeted in multiple attacks over the past months by different nation-backed actors, including attacks by IRGC-affiliated “CyberAv3ngers” in November 2023, as well as pro-Russian hacktivists in early 2024. These repeated attacks against OT devices emphasize the crucial need to improve the security posture of OT devices and prevent critical systems from becoming easy targets.
OT systems, which control real-world critical processes, present a significant target for cyberattacks. These systems are prevalent across various industries, from building heating, ventilation, and air conditioning (HVAC) systems, to water supply and power plants, providing control over vital parameters such as speed and temperature in industrial processes. A cyberattack on an OT system could transfer control over these critical parameters to attackers and enable malicious alteration that could result in malfunctions or even complete system outages, either programmatically via the programmable logic controller (PLC) or using the graphical controls of the human machine interface (HMI).
Adding to the potential damage of attacks on OT systems are their often-lacking security measures, which make OT attacks not only attractive for attackers but also relatively easy to execute. Many OT devices, notwithstanding common security guidelines, are directly connected to the internet, making them discoverable by attackers through internet scanning tools. Once discovered by attackers, poor security configurations, such as weak sign-in passwords or outdated software with known vulnerabilities, could be further exploited to obtain access to the devices.
The attractiveness of OT systems and attackers’ capabilities against systems with weak configurations were demonstrated in the Israel-Hamas war, which was accompanied by a spike in cyberattacks, including from OT-focused actors. Shortly after October 7, the Telegram channels of several such actors broadcasted their attacks against OT systems associated with Israeli companies. These publications were often accompanied by images of purportedly compromised systems, which the threat actors presented as alleged evidence for the attacks.
Microsoft’s analysis of multiple attacks by these actors revealed a common attack methodology: focusing on internet-exposed, poorly secured OT devices. This report will illustrate this attack methodology using the high-profile case of the November 2023 attack against Aliquippa water plant, for which CISA released an advisory in December 2023. CISA attributed the attack to the Islamic Revolutionary Guard Corps (IRGC)-affiliated actor “CyberAv3ngers”, tracked by Microsoft as Storm-0784. Microsoft assesses that the same methodology has been utilized by other OT-focused threat actors in multiple other attacks as well.
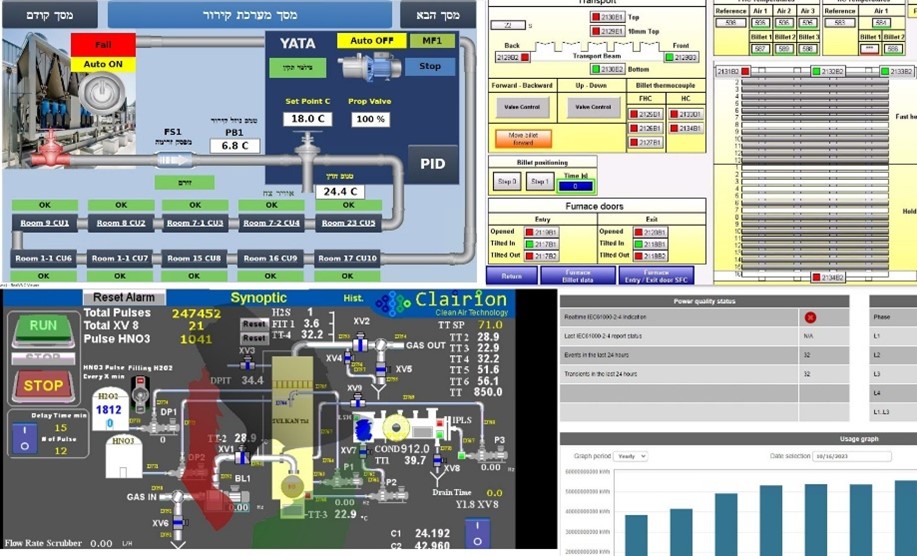 Figure 1. Sample images of victim systems as posted by actors on their Telegram channels
Figure 1. Sample images of victim systems as posted by actors on their Telegram channels
The attacks conducted by OT-focused actors were not limited to public sector facilities but also affected private companies in various countries. While the public sector has been implored to implement proper risk management and protection of OT systems, the diversity of target profiles illustrates that ensuring OT security in the private sector is equally crucial. Recommendations for organizations to protect against similar attacks and improve the security posture of their OT systems can be found at the end of this report.
Spike in activity of OT threat actors
Shortly after the outbreak of the Israel-Hamas war, Microsoft has seen a rise in reports of attacker activity against OT systems with Israeli affiliation. This included activity by existing groups such as the IRGC-affiliated “CyberAv3ngers”, and the emergence of new groups such as the “CyberAv3ngers”-associated “Soldiers of Solomon”, and “Abnaa Al-Saada”, a cyber persona presenting itself as Yemeni. Microsoft tracks both “CyberAv3ngers” and its associated group “Soldiers of Solomon” as Storm-0784.
The systems targeted by these groups included both OT equipment deployed across different sectors in Israel, including PLCs and HMIs manufactured by large international vendors, as well as Israeli-sourced OT equipment deployed in other countries. The attacks were made public by the actors using their Telegram channels, on which they also posted images of the target systems to enhance purported credibility and present evidence for the attack.
Researching the threat actors in question, Microsoft has identified a typical target profile that attackers appeared to focus on: internet-exposed OT systems with poor security posture, potentially accompanied by weak passwords and known vulnerabilities.
The Aliquippa case: A high-profile OT attack
In late November 2023, the Aliquippa water plant was affected by a cyberattack that resulted in the outage of a pressure regulation pump on the municipal water supply line in Aliquippa, Pennsylvania. In addition to impairing functionality, the attack, which targeted a PLC-HMI system by Israeli manufacturer Unitronics, also defaced the device to display a red screen with the name and logo of the “CyberAv3ngers” actor. The US Department of Treasury sanctioned officials in the Iranian Islamic Revolutionary Guard Corps Cyber-Electronic Command (IRGC-CEC) in relation to the attack.
Around the same time, multiple other attack cases on Unitronics systems were reported across the industry in other parts of the world, with targeted equipment displaying the same message: “Every equipment ‘made in Israel’ is a Cyber Av3ngers legal target“.
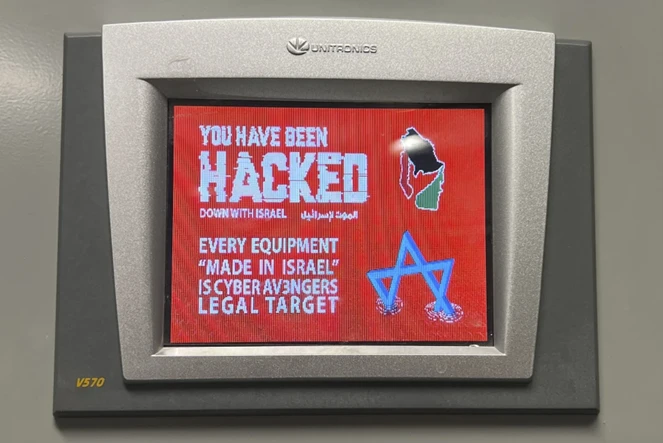 Figure 2. A photo of the Aliquippa Unitronics PLC released to media by the Municipal Water Authority of Aliquippa. The top right corner displays the Cyber Av3ngers’ group logo. The bottom left corner discloses model number V570 (source: THE TIMES OF ISRAEL)
Figure 2. A photo of the Aliquippa Unitronics PLC released to media by the Municipal Water Authority of Aliquippa. The top right corner displays the Cyber Av3ngers’ group logo. The bottom left corner discloses model number V570 (source: THE TIMES OF ISRAEL)
Microsoft analyzed the publicly available data on the Aliquippa incident to find the victim system and assess how it was compromised. Leveraging researchers’ intimate OT knowledge to interpret the limited details known to the public has enabled the identification of a specific machine that Microsoft believes to be the victim.
According to publicly accessible sources, the targeted system was exposed to the internet, and it suffered both defacement and the shutdown of the pump it controlled. Designated engines that map internet-connected devices and their associated services allowed Microsoft researchers to compile a list of internet-exposed Unitronics devices of the relevant model, which also had a dedicated control port open. This configuration could potentially allow to reprogram the device reprogramming, leading to the observed defacement and shutdown.
The analysis of contextual data narrowed the device profile list, identifying a specific system that could be the victim. This system was geographically situated near the Aliquippa station, with its PLC Name field set to “Raccoon Primary PLC”, consistent with the Aliquippa water station serving Potter and Raccoon townships, and also aligning with a photograph disseminated by the media, depicting a sign that reads “PRIMARY PLC” on the targeted system.
The data gathered throughout the research of the Aliquippa attack case highlights a trend: a common target profile of internet-exposed OT systems with a weak security posture that mirrors other attack cases.
Attacks representing a broader concerning trend
The CISA advisory that was released following the attacks in November 2023 described the profile of the targeted OT systems as being internet-exposed and having weak sign-in configurations. In May 2024, CISA released another advisory following the more recent attacks against the water sector, which showed that the victims had a similar profile. Again, OT systems that were left internet-exposed and had weak passwords were targeted by nation-state attackers, this time by pro-Russia activists.
While attacks on high-profile targets, especially in the public sector, often receive significant media attention, it’s important to recognize that the private sector and individual users may also be impacted. Notably, the Aliquippa water plant was just one victim in a series of attacks on Unitronics by “CyberAv3ngers”, which also expanded to the private sector. Screenshots of affected systems with the same red screen and message have been posted by users on the Unitronics forum claiming their equipment was attacked, with similar reports also showing on social media platform X. Following the incidents, a vulnerability was assigned for the Unitronics default password configuration (CVE-2023-6448), and a patch was issued by Unitronics to require users to fix the issue.
The common target profile for the attack cases analyzed reflects what attackers do to pick an easily accessible and appealing target in the first place. Attackers can, and do, obtain visibility on OT devices that are open to the internet using search engines, identify vulnerable models and open communication ports, and then use the contextual metadata to identify devices that are of special interest, such as ICS systems in water plants or other critical facilities. At that point, a weak password or an outdated system with an exploitable vulnerability is all that stands between them and remote access to the system.
The growing attention from attackers towards OT systems, observed across various sectors, is particularly concerning due to inadequate security practices on these systems. The Microsoft Digital Defense Report 2023 highlights that 78% of industrial network devices on customer networks monitored by Microsoft Defender for IoT have known vulnerabilities. Among these, 46% utilize deprecated firmware, for which patches are no longer available, while the remaining 32% operate outdated systems with unpatched vulnerabilities. For devices that are patched, many still use default passwords or have no passwords at all. Microsoft collects statistics on the prevalence of username and password pairs seen used in Microsoft’s sensor network, as was shared in the Microsoft Digital Defense Report 2022. Such outdated and vulnerable systems present attractive targets for future attacks, particularly when coupled with internet connectivity and default passwords. In the next sections, we share recommendations for improving the security posture of OT systems to help prevent attacks.
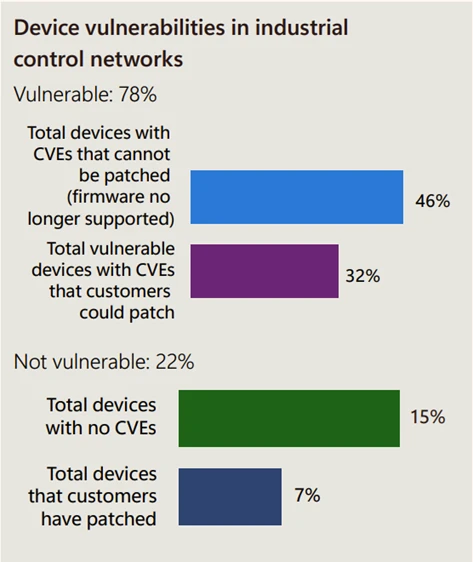 Figure 3. Statistics of vulnerable devices in customer industrial network. Source: Microsoft Digital Defense Report October 2023
Figure 3. Statistics of vulnerable devices in customer industrial network. Source: Microsoft Digital Defense Report October 2023
Mitigation and protection guidance
The analysis of the attack claims in question reveals diverse target profiles. It is therefore vital for organizations of all different sectors to ensure security hygiene for their OT systems to prevent similar threats.
- Adopt a comprehensive IoT and OT security solution such as Microsoft Defender for IoT to allow visibility and monitoring of all IoT and OT devices, threat detection and response, and integration with SIEM/SOAR and XDR platforms such as Microsoft Sentinel and Microsoft Defender XDR.
- Enable vulnerability assessments to identify unpatched devices in the organizational network and set workflows for initiating appropriate patch processes through Microsoft Defender Vulnerability Management and Microsoft Defender for Endpoint with the Microsoft Defender for IoT add-on.
- Reduce the attack surface by eliminating unnecessary internet connections to IoT devices and OT control systems. Verify that no OT system is directly connected to the internet, for example, through IoT routers or Cellular bridged (LTE or 3G). Close unnecessary open ports and services on their equipment, eliminating remote access entirely when possible, and restricting access behind a firewall or VPN when full elimination cannot be achieved.
- Implement Zero Trust practices by applying network segmentation to prevent an attacker from moving laterally and compromising assets after intrusion. OT devices and networks should be isolated from IT with firewalls. Extend vulnerability and exposure control beyond the firewall with Microsoft Defender External Attack Surface Management. Turn on attack surface reduction rules in Microsoft Defender for Endpoint to prevent common attack techniques such as those used by ransomware groups.
Microsoft Defender for IoT detections
Microsoft Defender for IoT provides detections for suspicious behaviors of OT and IoT devices. Alerts related to internet access and modification of PLC behavior will detect activity of this type, such as:
- External address within the network communicated with Internet
- Internet Access Detected
- Unauthorized Internet Connectivity Detected
- Unauthorized PLC Program Upload
- Unauthorized PLC Programming
References
- IRGC-Affiliated Cyber Actors Exploit PLCs in Multiple Sectors, Including U.S. Water and Wastewater Systems Facilities | CISA
- Municipal Water Authority of Aliquippa hacked by Iranian-backed cyber group – CBS Pittsburgh (cbsnews.com)
- Aliquippa Water Authority – Municipal Water Authority of Aliquippa
- Cyber group backed by Iran is taking credit for Pennsylvania water system cyberattack
- PLC Hacking – More Commonplace Than You Might Think – Best Programming Practices – Unitronics Support Forum: Programmable Controllers (PLC + HMI All-in-One)
- Full Pint Beer on X: “Ugh – the brewery control system received a CYBER ATTACK over the weekend!!! We are working to restore things to working order, kudos to the crew at @Brewmation for working with us over the Thanksgiving weekend! Thank goodness for backups! #cyberattack #automation #ransomware https://t.co/SNdXY9ne4h” / X
- NVD – CVE-2023-6448 (nist.gov)
- Unitronics-Cybersecurity-Advisory-2023-001-CVE-2023-6448.pdf (unitronicsplc.com)
- Iranian cyber attack targets Israeli tech used by several US bodies | The Times of Israel
Learn more
For the latest security research from the Microsoft Threat Intelligence community, check out the Microsoft Threat Intelligence Blog: https://aka.ms/threatintelblog.
To get notified about new publications and to join discussions on social media, follow us on LinkedIn at https://www.linkedin.com/showcase/microsoft-threat-intelligence, and on X (formerly Twitter) at https://twitter.com/MsftSecIntel.
To hear stories and insights from the Microsoft Threat Intelligence community about the ever-evolving threat landscape, listen to the Microsoft Threat Intelligence podcast: https://thecyberwire.com/podcasts/microsoft-threat-intelligence.
The post Exposed and vulnerable: Recent attacks highlight critical need to protect internet-exposed OT devices appeared first on Microsoft Security Blog.