Word Documents with malicious Macro code are common attack vector used by different malware now to download and infect user’s machine upon opening the office file that maybe attached to e-mail or downloaded in untrusted website. Emotet malware are one of those malware in wild that are actively use this vector and in past few days it use Microsoft Office XML format to execute malicious document with macro.
So let start…
The said malicious document contain 2 pkg that are base64 encoded. First is the actual document that contain macro and the other is binary pkg for the image message that lure the user to enable macro feature.
| figure 1 - the encoded component of the MS XML office |
| fig. 2 - the Shape ID to parse the obfuscated bat command |
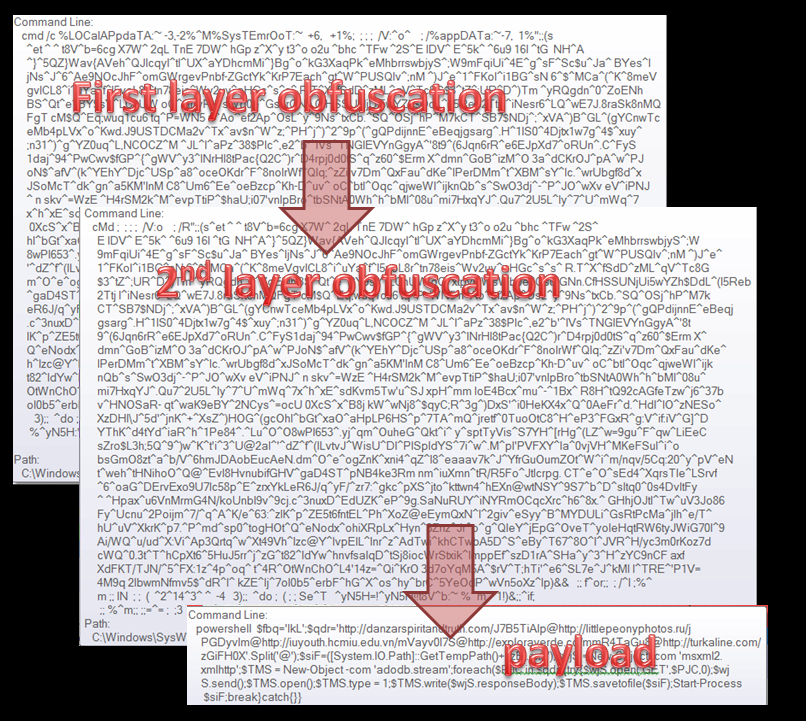 |
| fig. 3 - payload |
Conclusion:
It is really interesting how they keep on finding some way to hide their malicious code and bypassed security product. maybe this detection will bypassed the normal file base signature within a doc file but with other aspect of detection like behavior monitoring or ML classifier for malicious document with this type of features, this technique can still be detected and protect the user from infection.Sha1: 18150ca6134d4da1f5cceb41d891ac2279641704
md5: e45bb46dc465be0c6024c44b66e1db9a
Sha256: 7ccfb6433cc7b3173250028d08719efd1cbe5e556cc284f73a4f88c7aae4b008
FileName: INV299.doc
Article Link: https://tccontre.blogspot.com/2019/01/emotet-malware-used-microsoft-office.html