The CVE-2018-8174 is a bug that allows remote code execution in the VBScript Engine. Found exploited in the wild as a 0day via Word documents, announced by the Qihoo360 on April 20, 2018, patched by Microsoft on May 8, 2018 and explained in details by Kaspersky the day after.
A Proof of Concept for Internet Explorer 11 on Windows 7 has been shared publicly 3 days ago, it’s now beeing integrated in Browser Exploit Kits.
This will replace CVE-2016-0189 from july 2016 and might shake the Drive-By landscape for the coming months.
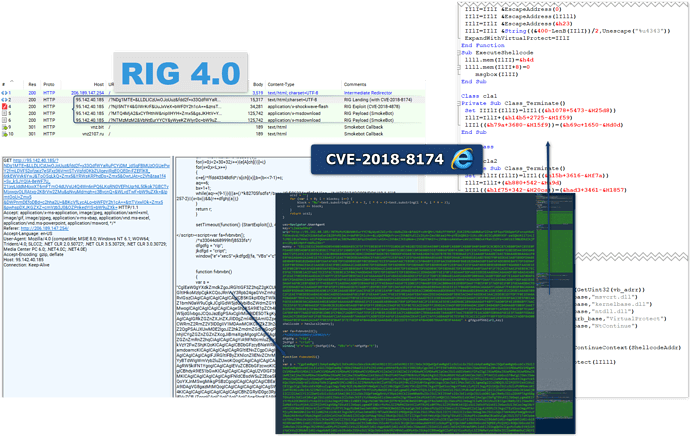
RIG:
Spotted on the 2018-05-25
“TakeThat” wrote yesterday (2018-05-24) that he has integrated it and that infection rate has increased:
Добавлен CVE-2018-8174
Add CVE-2018-8174
Пробив/rate + ![]()
[redacted]@exploit.im
[redacted]@xmpp.jp
And indeed today:
Figure 6: RIG launching code exploiting CVE-2018-8174 against IE11 on Windows 7 - 2018-05-25
| IOC | Type | Comment | Date |
|---|---|---|---|
| 206.189.147.254 | IP | Redirector | 2018-05-23 |
| 95.142.40.187 | IP | RIG | 2018-05-24 |
| 95.142.40.185 | IP | RIG | 2018-05-24 |
| 95.142.40.184 | IP | RIG | 2018-05-24 |
| 46.30.42.164 | IP | RIG | 2018-05-24 |
| vnz[.]bit|104.239.213[.]7 | domain|IP | Smoke Bot C2 | 2018-05-25 |
| vnz2107[.]ru|104.239.213[.]7 | domain|IP | Smoke Bot C2 | 2018-05-25 |
| 92e7cfc803ff73ed14c6bf7384834a09 | md5 | Smoke Bot | 2018-05-25 |
| 58648ed843655d63570f8809ec2d6b26 | md5 | Extracted VBS | 2018-05-25 |
*Files: PCAP on VT
Acknowledgement:
- Thanks to William Metcalf and Frank Ruiz (FoxIT InTELL) for their help.
Read More:
The King is dead. Long live the King! - 2018-05-09 - SecureList
Analysis of CVE-2018-8174 VBScript 0day - 2018-05-09 - Qihoo360
Article Link: http://malware.dontneedcoffee.com/2018/05/CVE-2018-8174.html