In mid-December 2023, researchers at Volexity identified suspicious activity within a client’s network. Their investigation uncovered the deployment of webshells on various internal and external web servers, traced back to the organization’s Ivanti Connect Secure (ICS) VPN appliance.
Upon inspecting the Ivanti Connect Secure VPN appliance, researchers discovered wiped logs and disabled logging, and that the suspicious activity dated back to December 3, 2023.
Subsequent findings confirmed the use of an exploit chain, leveraging zero-day vulnerabilities identified as CVE-2023-46805 and CVE-2024-21887. Exploiting these vulnerabilities enabled the attacker to bypass authentication and achieve Remote Code Execution (RCE).
Details of Ivanti Connect Secure Zero-Day Vulnerabilities (CVE-2023-46805, CVE-2024-21887)
CVE-2023-46805 (CVSS Score: 8.2, High): It is an authentication bypass vulnerability in the web component of Ivanti Connect Secure 9.x, 22.x, and Ivanti Policy Secure. It enables remote attackers to access restricted resources by bypassing control checks.
 SOCRadar Vulnerability Intelligence: CVE-2023-46805
SOCRadar Vulnerability Intelligence: CVE-2023-46805
CVE-2024-21887 (CVSS Score: 9.1, Critical): Web components of Ivanti Connect Secure (9.x, 22.x) and Ivanti Policy Secure contain this command injection vulnerability, which allows an authenticated administrator to execute arbitrary commands via crafted requests.
 SOCRadar Vulnerability Intelligence: CVE-2024-21887
SOCRadar Vulnerability Intelligence: CVE-2024-21887
When used in an exploit chain, these vulnerabilities enable attackers to craft malicious requests and execute arbitrary commands without authentication.
In the case observed by the researchers, the attacker utilized the zero-day vulnerabilities to steal configuration data, modify files, download remote files, and reverse tunnel from the Ivanti Connect Secure VPN appliance.
Ivanti says mitigation is available for CVE-2023-46805 and CVE-2024-21887, while a patch is in development, scheduled for staggered release (first version by the week of January 22, final version by the week of February 19). The company advises urgent action to mitigate these vulnerabilities. To access the mitigation guide, you can visit the official Ivanti advisory here.
The Cybersecurity and Infrastructure Security Agency (CISA) has also issued an alert, stating that it has added these vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog. The agency warns that these types of vulnerabilities pose significant risks to the federal enterprise; organizations are expected to patch these vulnerabilities by the due date of January 31, 2024.
You can monitor digital assets and identify vulnerabilities that are affecting your organization through SOCRadar’s Attack Surface Management (ASM) module. The Company Vulnerabilities page on ASM includes a CISA KEV Check feature for easy identification of KEV Catalog-listed vulnerabilities affecting your systems.
 SOCRadar ASM/Company Vulnerabilities
SOCRadar ASM/Company Vulnerabilities
The Attack Scheme Exploiting Ivanti Connect Secure Zero-Days
Researchers detected the attacker manipulating legitimate Ivanti Connect Secure components to bypass the Integrity Checker Tool. While predominantly relying on Living Off the Land (LOTL) techniques for stealth, the attacker deployed webshells, proxy utilities, made file modifications, and harvested credentials.
Malicious files found on the compromised Ivanti Connect Secure VPN appliance included a modified Perl module (DSLogConfig.pm), a Perl script (sessionserver.pl, sessionserver.sh) for remounting the filesystem with read/write access, a backdoored component enabling command execution (compcheckresult.cgi), and a modified JavaScript file (lastauthserverused.js) acting as a keylogger.
DSLogConfig.pm executed sessionserver.pl, which, in turn, ran sessionserver.sh, restoring mount settings. Sessionserver.sh modified compcheckresult.cgi, inserting a webshell and evading the Integrity Checker Tool during scans.
Compcheckresult.cgi allowed RCE with proper parameters. Lastauthserverused.js acted as a keylogger, sending harvested credentials to a remote URL. The attacker, armed with information and credentials, pivoted within the network, eventually gaining unrestricted access.
After breaching via the Ivanti Connect Secure VPN appliance, the attacker adopted a systematic approach – moving between systems using compromised credentials, further breaching them, and expanding access via Remote Desktop Protocol (RDP). While exploring the network, Volexity noted reconnaissance activities by the attacker.
During network traffic analysis, researchers also identified the deployment of webshell variants on both internet-accessible and internally accessible servers, which they dubbed as GLASSTOKEN.
Understanding the GLASSTOKEN Webshell
The attacker utilized two variations of the webshell: The first version exhibits two distinct code paths, its execution dependent on the parameters present in the request; evidence suggests that Version 1 was primarily employed for executing arbitrary PowerShell commands. Nearly identical to the first version, Version 2 retains only the second code path, facilitating code execution.
Beyond executing commands on the VPN appliance, these webshells served as the primary means for the attacker to maintain persistence.
For comprehensive details on observed attacker activity and insights into these webshells, refer to the detailed research.
Exposure of Ivanti Connect Secure Appliances
A ZoomEye search shows that approximately 13,272 Ivanti Connect Secure appliances and 83 Ivanti Policy Secure appliances are exposed on the internet. This substantial number emphasizes the urgency for organizations to fortify their security posture.
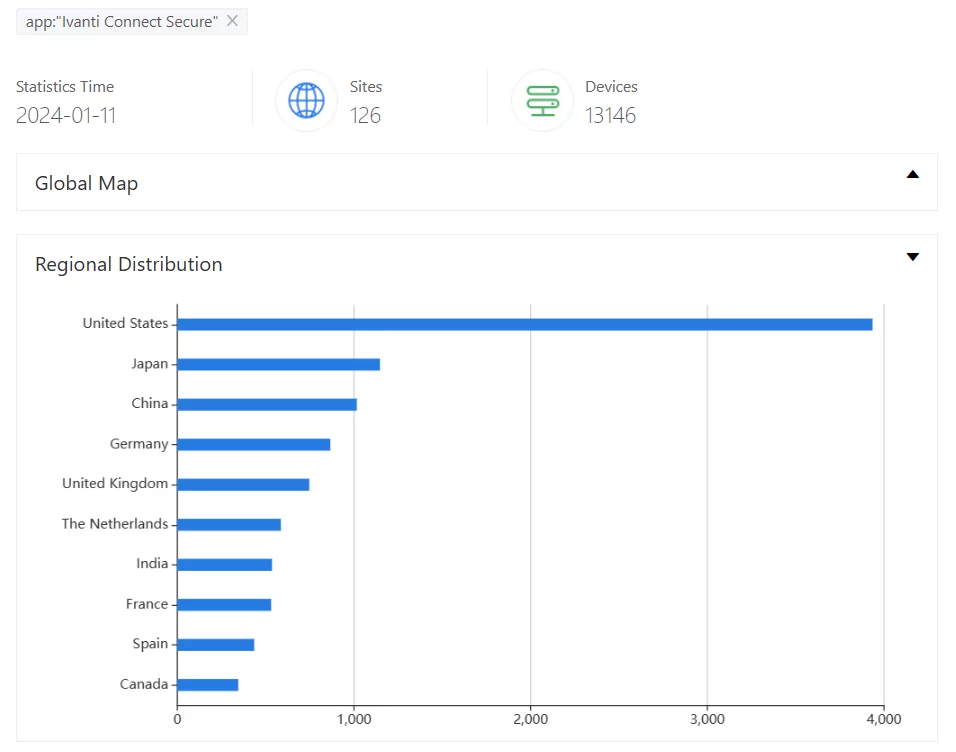 ZoomEye search results for Ivanti Connect Secure
ZoomEye search results for Ivanti Connect Secure
Security Recommendations for Compromised Ivanti Connect Secure VPN Appliance
The researchers recommend several security measures to effectively mitigate the impact of an Ivanti Connect Secure VPN appliance compromise:
- Immediate response is critical upon detecting compromise. Avoid a simplistic wipe-and-rebuild approach.
- Gather essential evidence by collecting logs, system snapshots, and forensics artifacts (memory and disk) from the compromised Ivanti Connect Secure VPN appliance.
- Urgently analyze internal systems to track potential lateral movement by the attacker.
- Assume compromise of any credentials, secrets, or sensitive data stored on the compromised appliance, and take appropriate action to change them.
How Can SOCRadar Help?
Beyond Attack Surface Management (ASM), SOCRadar XTI offers comprehensive Vulnerability Intelligence to provide the latest updates about known vulnerabilities, including available exploits, repositories, hacker trends, and exploitability risks.
 SOCRadar Vulnerability Intelligence
SOCRadar Vulnerability Intelligence
Experience the power of SOCRadar by signing up for the free edition, unlocking its XTI capabilities to elevate your vulnerability management strategy.
Indicators of Compromise (IOCs)
Here are the Indicators of Compromise (IOCs) found related to the exploitation activity:
IP Addresses:
- 206.189.208.156
- 75.145.243.85
- 47.207.9.89
- 98.160.48.170
- 173.220.106.166
- 73.128.178.221
- 50.243.177.161
- 50.213.208.89
- 64.24.179.210
- 75.145.224.109
- 50.215.39.49
- 71.127.149.194
- 173.53.43.7
Hostnames:
- symantke[.]com (Attacker domain used to collect credentials from compromised devices)
- gpoaccess[.]com (Suspected attacker domain)
- webb-institute[.]com (Suspected attacker domain)
The post Attackers Exploit Ivanti Connect Secure Zero-Day Vulnerabilities to Deploy Webshells (CVE-2023-46805, CVE-2024-21887) appeared first on SOCRadar® Cyber Intelligence Inc..
Article Link: Attackers Exploit Ivanti Connect Secure Zero-Day Vulnerabilities to Deploy Webshells (CVE-2023-46805, CVE-2024-21887)
