Picture this: A group of IBM employees once tailgated their way into a client’s office building carrying a box of doughnuts, their laptops and testing gear. The group found an unoccupied conference room and placed the doughnuts on a table outside, along with a sign that said the group was conducting network testing there.
They managed to work in the office all week — unchallenged and unquestioned — and penetrated the company’s network from the inside, fulfilling their mission. So began another engagement for the IBM X-Force Red team, a unique group of more than 100 security analysts who probe customers’ networks for vulnerabilities.
Cris Thomas, who also goes by the pseudonym Space Rogue, is the global strategy lead at IBM X-Force Red. I recently spoke with him to discuss his work as a penetration testing specialist, his role as a cybersecurity activist in the late 1990s — and the recent reunion of his influential hacking group on Capitol Hill.
Inside Offensive Security
The X-Force Red team doesn’t “just do vulnerability assessment, which is what most folks think of when it comes to offensive security,” according to Thomas. It also uses both automated and manual tools and conducts code reviews and physical security testing.
In other words? The team does exactly what cybercriminals do.
Physical security is perhaps the most popular assessment. This tactic is where a team member tries — with full authorization, of course — to enter a company’s premises and hack its network from the inside, as in the now notorious doughnut example above. When they begin an engagement, members of the team usually find a vulnerability within a day or so.
“We have never been to a client that we haven’t gotten into their network and found something serious,” Thomas said. “While it’s depressing to think that holes are everywhere, it’s a positive thing because we help our customers find and patch these holes and better secure their environments.”
During his time at IBM, Thomas has worked on improving the IBM X-Force Red portal, which customers use to retrieve reports and schedule work for teams. He also worked on a project to expand an internship program.
“There are not a lot of opportunities for offensive security positions at the college level, so we are ramping that up,” Thomas said. “That helps feed our employee pipeline too.”
White Hats Go to Washington
In 1998, Thomas and other members of attacker think tank L0pht Heavy Industries testified to Congress. L0pht is infamous for developing a series of hacking tools, such as Windows NT password crackers and a website called Hacker News Network. The white-hat hacking group also took on numerous consulting projects over the years. (Security firm @Stake acquired the think tank in 2000, and Symantec subsequently acquired @Stake in 2004.)
During their testimony two decades ago, the group warned that computer networks were embarrassingly insecure — and bragged that any one of them could take the entire internet down in only a few minutes thanks to weaknesses in the core Border Gateway Protocol (BGP) routing. (The members even used their hacker names on their nameplates because many of them feared prosecution.)

L0pht Heavy Industries testifying before Congress in 1998. (Photo courtesy of Cris Thomas.)
The Return of the White Hats
Thomas and several L0pht colleagues made headlines again in May 2018 when they reunited on Capitol Hill. The reason for their reunion? The group wanted to talk to Congress about the progress of cybersecurity regulations.
While the group didn’t meet with representatives this time around — and their given names were openly discussed — there was still a serious reason for their reunion. Four of the original members returned to Capitol Hill to say that while security technology has improved, some things haven’t changed.
“Nearly all of what we said 20 years ago still holds true,” said Joe “Kingpin” Grand, another member of the L0pht group. “Yes, there have been improvements, but the general class of problems are the same.” For example, the same 1998 BGP flaws were used in the MEWKit phishing attack in May 2018.
“We have better visibility into our network endpoints, if we choose to gather it, and can make educated decisions about where to apply our limited resources,” Thomas testified. “Strong encryption is more prevalent, but we aren’t evenly applying the knowledge of how to make something secure.”
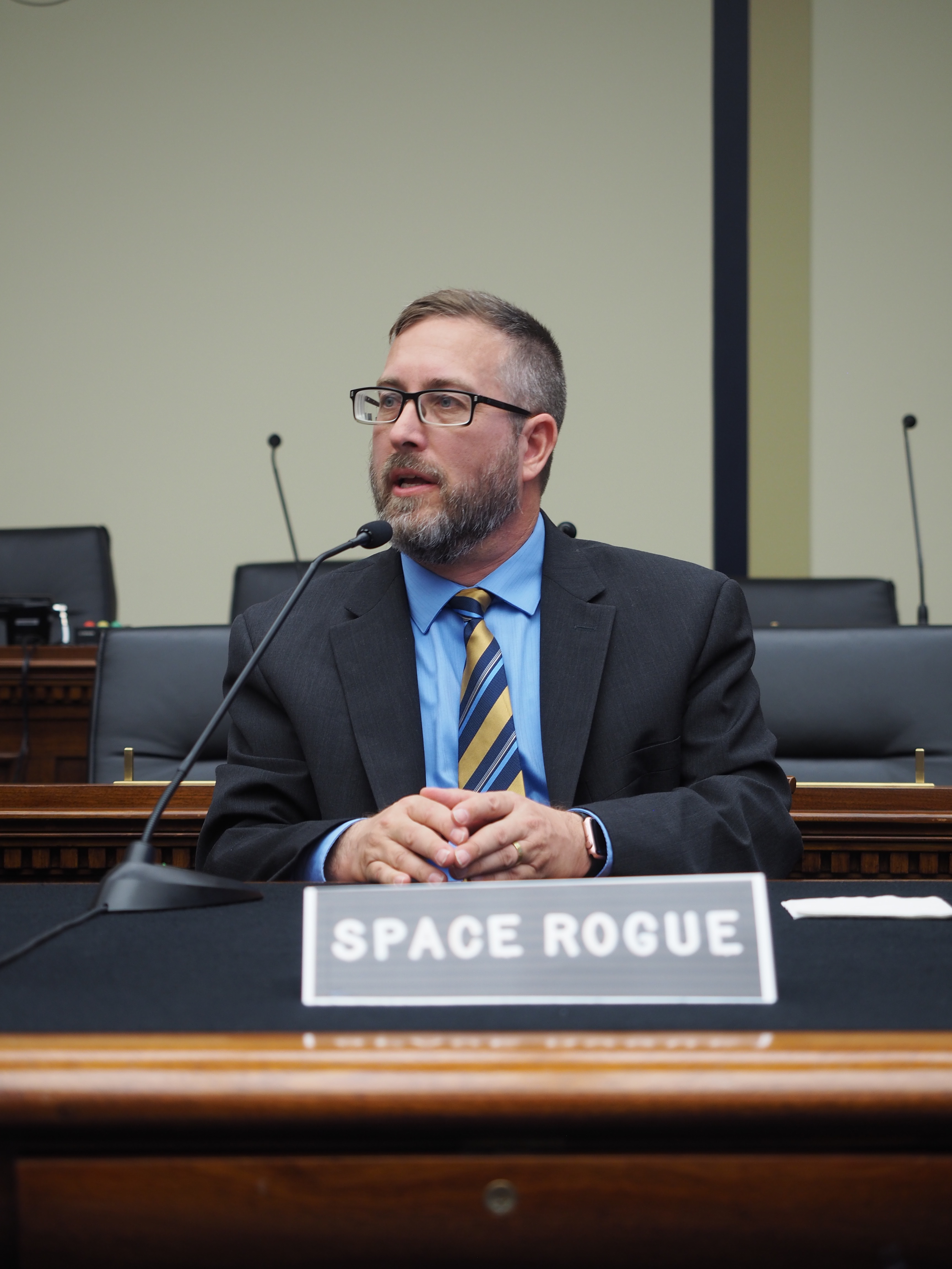
Cris Thomas, who also goes by the pseudonym Space Rogue, testifying before Congress in 2018. (Photo courtesy of Debra Kavaler Wysopal.)
Space Rogue Spreads Security Awareness
In the past 20 years, Thomas has made other visits to Capitol Hill, primarily to brief congressional staffers about technology and security issues.
“Staffers influence the elected representative, so they help to make sure that the basic tech knowledge is available to them,” Thomas said. “I want the representatives to have this knowledge because then they will make the right decisions. That’s regardless of whether they agree with my point of view or not.”
In 2017, Thomas escorted two members of Congress around the show floor of DEF CON, a large hacker convention held annually in Las Vegas. It was an interesting experience for all of them.
“Clearly, there is an obvious knowledge gap with our elected officials, but they have to be experts in almost everything. So, it isn’t fair to expect them to be knowledgeable in technology,” Thomas said.
But did Thomas ever imagine he’d be working at IBM one day?
“Even two years ago, I never thought I would,” he said. “But Steve Ocepek [regional lead of North America at IBM X-Force Red] was the best manager that I have ever worked with, and when he asked me to come work for him at IBM, I took it seriously.”
Listen to the podcast: Talking Offensive Security with Space Rogue of X-Force Red
The post Space Rogue: A Security Rebel Turned Pen Tester appeared first on Security Intelligence.
Article Link: https://securityintelligence.com/space-rogue-a-security-rebel-turned-pen-tester/
