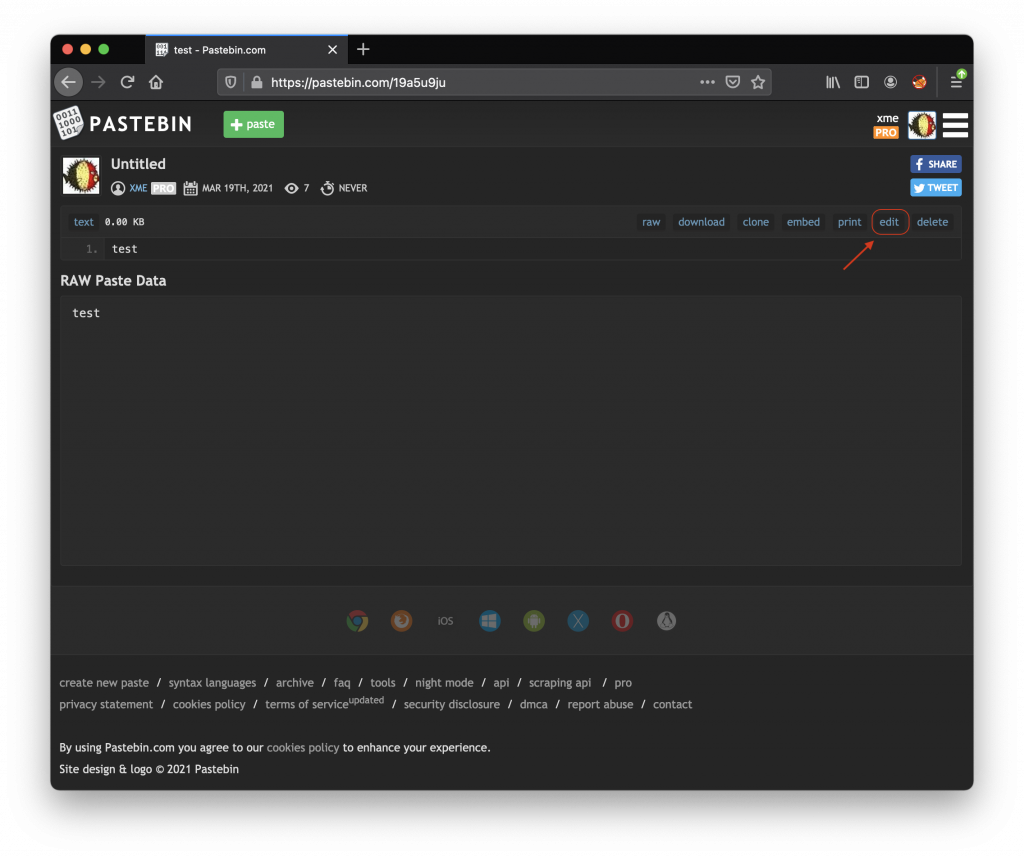
I published the following diary on isc.sans.edu: “Pastebin.com Used As a Simple C2 Channel“:
With the growing threat of ransomware attacks, they are other malicious activities that have less attention today but they remain active. Think about crypto-miners. Yes, attackers continue to mine Monero on compromised systems. I spotted an interesting shell script that installs and runs a crypto-miner (SHA256:00e2ddca696426d9cad992662284d1f28b9ecd44ed7c1be39789417c1ea9a5f2). The script looks to be a classic one but there are some interesting behaviors that I’d like to share… [Read more]
The post [SANS ISC] Pastebin.com Used As a Simple C2 Channel appeared first on /dev/random.
Article Link: https://blog.rootshell.be/2021/03/19/sans-isc-pastebin-com-used-as-a-simple-c2-channel/