Natural disasters aren’t wholly dedicated to any single season. Tornadoes can occur at any time, but generally occur from March through to June. Fire season generally runs from October to January. Earthquakes can occur at any time. The Atlantic hurricane season usually lasts half the year (between June and November), where we presently are once again. Depending where you live, these natural disasters may not directly affect you (or may be less likely than other locales), but it’s certainly a good time to consider how your business would react in the case of a natural disaster. Do you have a plan in place? Has that plan been communicated to all employees at your company? Hopefully the answer to both those questions is “yes.” Either way though, we’re here to talk about a few less obvious aspects of cybersecurity preparedness. Besides a Disaster Recovery/Business Continuity Plan (DR/BCP) and associated physical security concerns (which is of the utmost importance), we’ve highlighted some things to consider.
Your evacuation plan
If you have a BCP, hopefully you’ve an evacuation plan. It’s important to know exactly if and how business will carry on in the event of an evacuation (or emergency in general). Do all your employees have VPN access? If so, is the expectation that all employees will go home and continue working? Do you have sufficient hardware and licenses? What if the roads are closed – where do your employees go?
Another important consideration is communication. How will employees be updated throughout the disaster? Is there a central point of contact within the company that all internal and external communications should be directed?
In addition to communication, there needs to be an overall understanding among all employees about the impact of a natural disaster on business. Your employees should know what to do and what to expect before disaster strikes.
Acronyms that matter in the event of an emergency
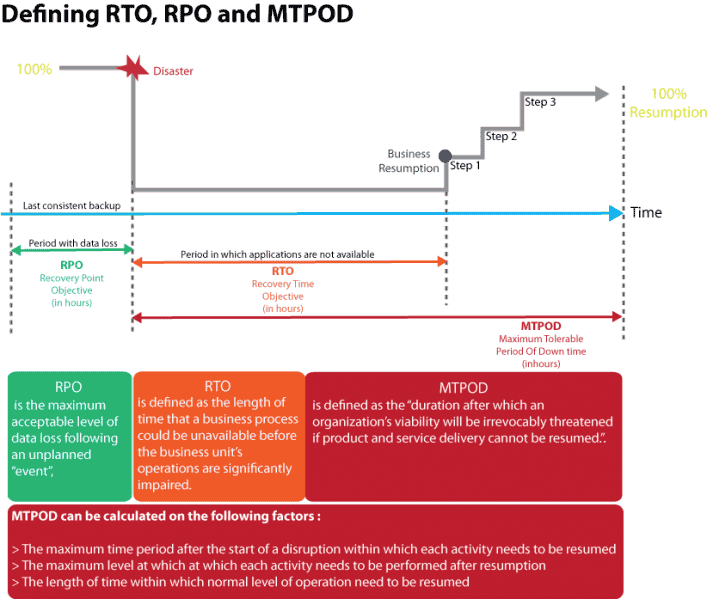
In case DR/BCP weren’t enough, there are a few more acronyms you should be familiar with. Each of these refers to an amount of time in which the firm can determine sufficient “downtime” for different systems within the firm.
Recovery Point Objective (RPO) - the point in time in the past to which you will recover. For example, if the RPO is one hour, backups must be made at least once per hour. In this situation, the most data you would worry about losing is anything from the last hour.
Recovery Time Objective (RTO) - the point in time in the future at which you will be up and running again.
Interruption Window - the maximum time allowed for restoration of critical systems so that its business goals are not negatively affected.
Maximum Tolerable Period of Disruption (MTPOD) - the maximum amount of time that a company’s key products or services can be unavailable or undeliverable after a disruption before its impact is deemed unacceptable.
Image taken from: http://www.bcmpedia.org/wiki/Maximum_Tolerable_Period_of_Disruption_(MTPOD)
For each critical system, the CTO should have a well-defined (and accepted) value of RPO, RTO, and MTPOD.
Cyberattackers
Emergency situations are naturally very chaotic. This can mean an increase in the likelihood of sensitive data being accidentally leaked. Amid confusion, employees are unlikely to place high priority on information security, yet these are precisely the moments cybercriminals may choose to test your cybersecurity defenses in creative and relevant ways. Here’s three things to watch out for online during a natural disaster:
1) Phishing scams disguised as charitable donations
Cybercriminals have been known to take advantage of compassionate people who want to help in a time of need. If a website is asking you to provide credit card information, make sure that it’s a valid site and organization.
2) Photos or videos that claim to be “just released” or “exclusive”
A photo or video that claims to be “never before seen” may actually lead you to click on a malicious link. This goes the same for websites offering exclusive information about the disaster. Always look for signs that the link you’re about to click on is legitimate, and remember that if something is truly worth seeing, you’ll probably be able to find it on a site you know is reputable. Cybercriminals will also take advantage of trending topics to spread malware, so remember that just because a post has “#hurricane,” it doesn’t mean that it’s safe to click.
3) Posts or messages from “friends” on social networks
Cybercriminals can hack into accounts and send fraudulent messages to everyone in the victim’s list of contacts. Remember, just because the messages seem somewhat tailored to the recipient, it doesn’t mean they won’t contain malicious links or files. If you’re ever unsure, contact your friend directly to confirm they sent the message through a different means of communication.
Lean on your security provider
There’s a lot to worry about during a natural disaster, and trying to think of everything may feel impossible. Fortunately, your security provider can help you. For example, during Hurricane Sandy in 2012, eSentire saw an increase in a certain amount of inbound attacks against clients across the Northeast USA. After investigating, we identified these attacks as fraudulent and alerted our clients to the possible danger.
With eSentire, each client has a sensor, and our Security Operations Center (SOC) is alerted when a client’s sensor becomes unreachable. If this happens, we immediately escalate the situation to confirm what is causing the sensor outage and reach out to the client to alert them. From there we can help the client with their escalation and emergencies procedures to ensure no data is lost in the event of a natural disaster.
Learn more
These situations are difficult and responding to them can be stressful. With Managed Detection and Response service, our SOC can be a great resource to monitor operations when you can’t. We’ve got your back. Let us know what we can do to help.
Article Link: https://www.esentire.com/blog/natural-disasters-threaten-more-than-just-physical-security/