by Matan Ben David
Inroduction
On December 16 2019, Check Point’s Incident Response Team (CPIRT) was engaged by three firms in the finance sector to investigate fraudulent wire transfers sent from their joint bank account. Four separate bank transactions attempted to transfer 1.1M GBP to unrecognized bank accounts. Emergency intervention with the banks allowed for the recovery of only £570K, leaving the rest as permanently lost funds.
If this scary scenario sounds familiar to you, it is because not so long ago, we released a report about a similar case investigated by CPIRT – An incident where attackers were able to divert $1M of funds, which were supposed to be transferred from a Chinese venture capital to an Israeli startup company.
In the following investigation we unravel the story behind the threat group we dubbed “The Florentine Banker” and shed light on how these types of sophisticated Business Email Compromise (BEC) attacks take place; from how the attackers monitor their victims for months, to how they gradually divert hundreds of thousands of dollars from unsuspecting organizations, into their own pockets.
The Target
Before diving in to all the evidence gathered, let us have a quick glance at our target profile. The targeted organizations are three large, UK and Israeli based finance sector firms – often handling and transferring large sums of money to new partners and third-party providers on a weekly basis.
The firms use Office 365 as their main email provider throughout the organization.
First Contact
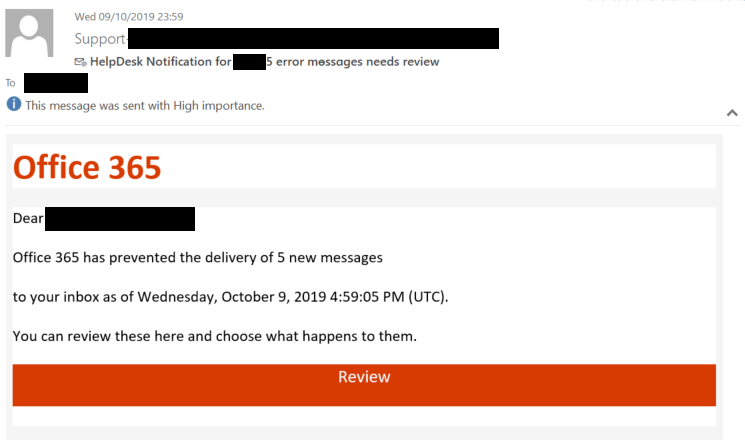
Having chosen a target, the Florentine Banker group starts their attack by setting up a targeted Phishing campaign against individuals inside the victim’s company. These individuals can be the CEO, CFO or any other key individuals within the organization who would be in charge of executing money transactions.
In our case, the first Phishing emails targeted only two personnel, of which one provided their credentials. Phishing attacks would continue, persisting for weeks in alternating methods, occasionally adding new individuals to the list of targets until the attackers gain a panoramic view of the entire financial aspect of the company.
Phishing email sent by the Florentine Banker group
Step 1: Observe
Once the attackers gain control over the victim’s email account, they start reading their emails in order to understand the following:
- The different channels used by the victim to conduct money transfers.
- The victim’s relationships with other third parties such as clients, lawyers, accountants and banks.
- Key roles inside the victim’s company.
The Florentine Banker can spend days, weeks or even months doing reconnaissance before actively intervening in the communication, patiently mapping the business scheme and procedures.
Step 2: Control & Isolate
After carefully studying the victim’s organization, the attackers start to isolate the victim from third parties and internal colleagues by creating malicious mailbox rules. These email rules would divert any emails with interesting content or subjects into a folder monitored by the threat group, essentially creating a type of “Man in the Middle” attack.
For example, any email containing pre-defined words such as “invoice”, “returned” or “fail” would be moved to another folder not commonly used by the victim, such as the “RSS Feeds” folder.
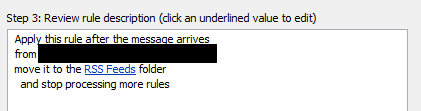
Outlook email rule – demo
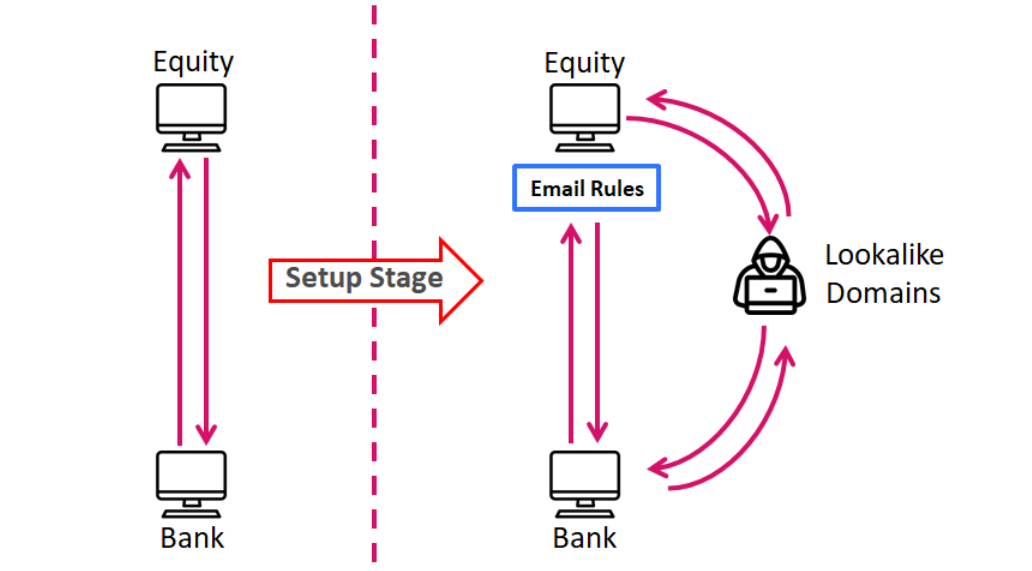
Step 3: Lookalike Setup
In order to proceed to the next stage of their operation, the attackers registered lookalike domains – domains that look visually similar to the legitimate domains of the entities involved in the email correspondences they want to intercept. For example, if there was a correspondence between “finance-firm.com” and “banking-service.com”, the attackers could register similar domains like “finance-firms.com” and “banking-services.com”.
Once the setup is complete, the attacker starts sending emails from the lookalike domains. They either create a new conversation or continue an existing one – thus deceiving the target who presumes the source of the email is legitimate, and does not notice the slight change to the domain name sending it.
Email flow example: before and after the setup
Step 4: Ask for Money
In this stage the attackers possess a high level of control over the firm’s inbound email traffic and can create legitimate looking emails, their correspondences would trust. This is without sending any actual email from the real firm’s account.
Now the attackers begin injecting fraudulent bank account information, with the following two techniques:
-
Intercepting legitimate wire transfers – by reading the firm’s emails, the attackers learned of planned money transfers. Using this knowledge and the infrastructure prepared in the Setup stage, the attacker provides “new” bank account details, thus funneling the funds to their own bank accounts.
In our case, the attackers noticed a planned transaction with a third party, in which the firm suggested using a UK bank account to speed up the process; but the receiving party reported they do not possess a bank account in the UK. The threat group leveraged the opportunity and provided an alternative UK bank account. - Generating new wire transfer requests – During the reconnaissance phase, the attackers learn how money transfers are executed – procedures, approval cycle and most importantly, the key people within the compromised organization and the banks who actually issue the transactions. Back to our case, the hackers scoured email correspondence between the firm and the bank through which it makes the money transfers. Using this information the Florentine Banker group contacted the firm’s bank contact, instructing new money transfer orders.
Final Step: Money Transfer
The Florentine Banker manipulates the conversation until the third party approves the new banking details and confirms the transaction. If the bank rejects the transaction due to a mismatch in the account currency, beneficiary name or any other reason, the attackers are there to fix the rejects until the money is in their own hands.
This was just the case with the heist here; the attackers monitored the correspondences with the bank contact, and made the required fixes and succeeded in maneuvering everyone to issue the transaction to their fraudulent account. Throughout this operation, the group was able to fraudulently transfer an approximate of £600K, accumulated by three different successful transactions that could not be reverted.
Additional Targets
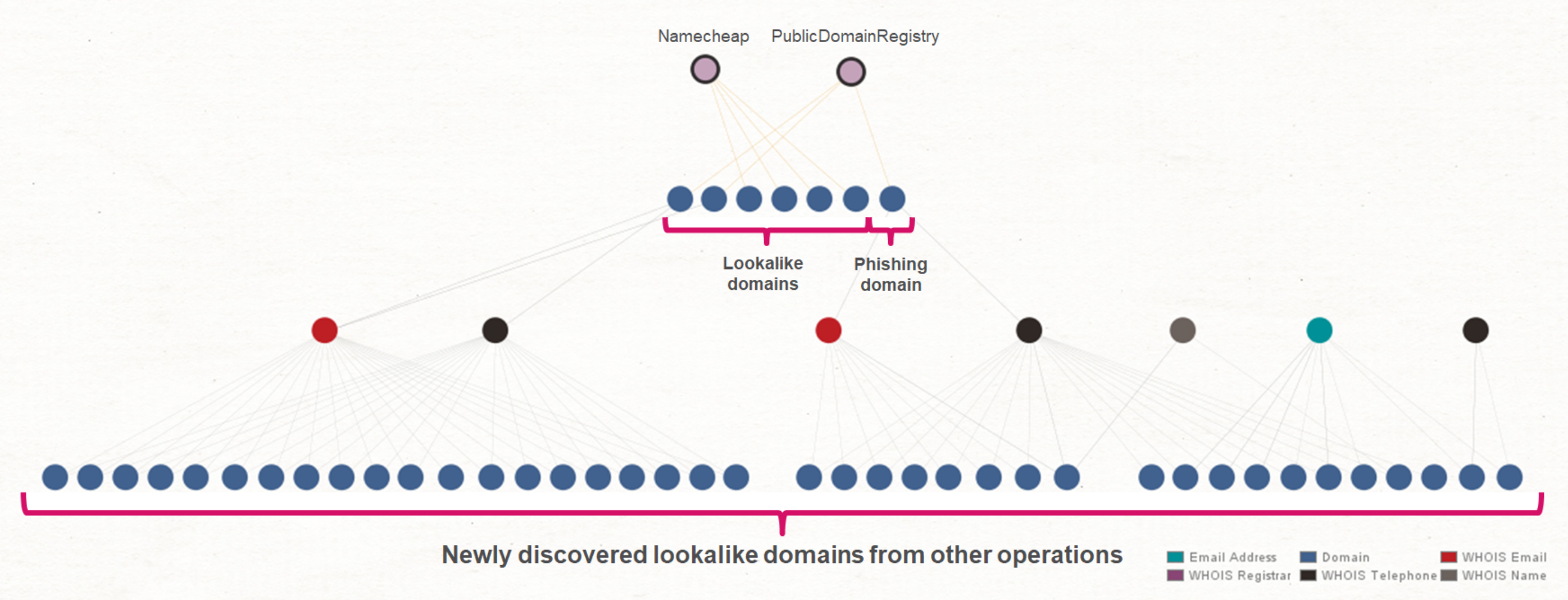
While investigating the above operation conducted by the Florentine Banker group, we gathered forensics information and observed various domains that were involved in this operation.
A total of seven different domains were used by the attackers; either lookalike domains, or a website to serve the Phishing pages.
We were able to use the data collected from the domains’ WHOIS information (registration name, email, telephone number), to extend our visibility into additional operations conducted by our threat actor.
Pivoting on the unique WHOIS information enabled us to find 39 additional lookalike domains registered throughout 2018-2020, evidently trying to masquerade as a variety of legitimate businesses who may have been targeted by the Florentine Banker as well.
Maltego view of domains investigation
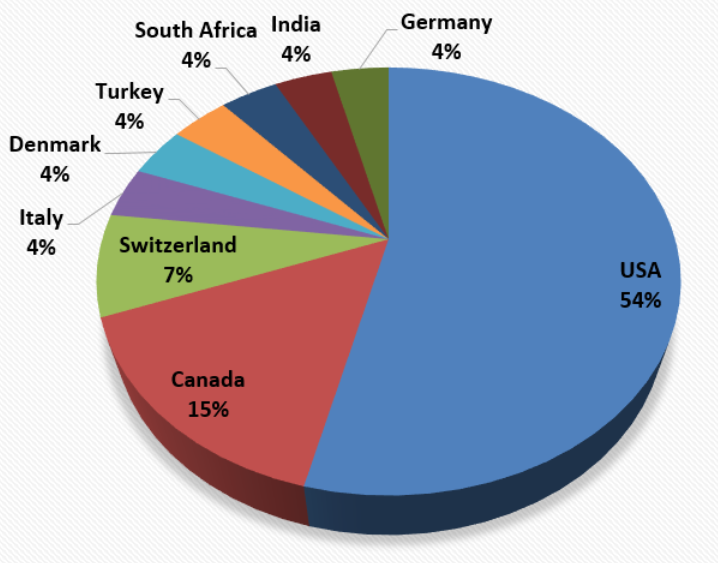
Below is a breakdown by country and industry of possible Florentine Banker targets, deduced from the lookalike domains we uncovered.
Victims by country
Victims by industry
Florentine Banker Origins
During our investigation we did not find definitive evidence to the origins of Florentine Banker, but we did observe a number of clues that might indicate their origin:
- Only conversations or transactions conducted in English were intercepted and modified.
- During the two months that the Florentine Banker group spent inside the victim’s environment, they operated Monday through Friday.
- Fraudulent bank accounts were located in Hong Kong and the United Kingdom.
- Several email threads in Hebrew included valuable leads that were not used by the attacker – which leads us to assume they do not speak Hebrew.
- A Hong Kong based company name was used for the fraudulent money transfers in which the Florentine Banker group requested a wire transfer directly from the victim’s bank contact. It appears that this company was either fake or previously registered and has since gone out of business.
To protect the privacy of the potential victims, we will not share the lookalike domains or the targeted brands. Check Point Research works to contact these organizations in order to prevent the next BEC heist.
Conclusion
Private equities and venture capitals have become a lucrative target for BEC operations. The fact that VC’s are often involved in transfers of large amounts of money, often to new partners and recipients, make them the perfect target to introduce new and fraudulent transactions.
The Florentine Banker group seems to have honed their techniques over multiple attacks, from at least several years of activity and has proven to be a resourceful adversary, quickly adapting new situations.
The techniques they use, especially the lookalike domains technique, present a severe threat – not only to the originally attacked organization, but also to the third-parties with whom they communicated using the lookalike domains. The attackers can continue and try initiate fraudulent activity with the third-parties with whom trust has been established, long after the main target has detected and removed the intruder from their network.
How to protect yourself
- Email is by far the number one vector for attackers to infiltrate business networks. Phishing emails baiting users to expose their organization credentials or to click on a malicious link/file are the number one threat in the email space. Organizations must always incorporate an email security solution, designed to prevent such attacks automatically utilizing continuously updated security engines.
- Educate your employees – proper and ongoing education of employees to the evolving threat landscape.
- When dealing with wire transfers, always make sure to add a second verification by either calling the person who asked to make the transfer or calling the receiving party.
- If a similar breach has been detected in your organization, make sure to notify all your business partners as well – any delay in notification only works for the benefit of the attacker.
For the email security vector, Check Point’s Artificial Intelligence based security engines include an advanced anti-phishing engine, which relies on behavioral analysis, designed to prevent precisely attacks similar to the one in our story.
The post IR Case: The Florentine Banker Group appeared first on Check Point Research.
Article Link: https://research.checkpoint.com/2020/ir-case-the-florentine-banker-group/