The eSentire’s threat intelligence team produced a 2017 threat landscape report. The report focuses on threat specific trends and developments that have been empirically assessed based on eSentire data. We have also provided several forecasting scenarios that are game-changers from a threat landscape perspective.
Some interesting observations that we did not expect to see:
- User passwords are considered high-value targets. We saw nearly 400% growth in brute force and dictionary attacks.
- “Home-based” network infrastructure is an attractive target. We saw a phenomenal increase in attacks against consumer-grade Netgear and Linksys routers.
- Despite limited media coverage, banking or information stealing malware is 3 times more prominent than ransomware.
- Organizations need to revise their phishing awareness programs as phishing methods remain highly successful, with a 130% success rate in comparison to last year.
- Attackers are smart and will monitor IT trends. That’s why DocuSign, Google and Outlook are the most prominent and successful lures used in phishing attacks.
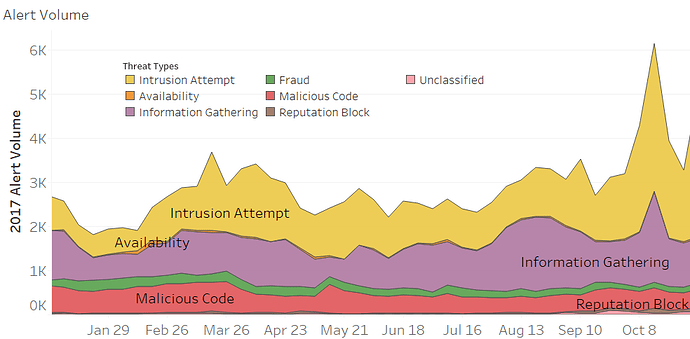
2017 Attack Types
Analysis of the eSentire threat detection landscape showed significant increases in alerts across the majority of threat types (see figure 1). Information gathering alerts saw the largest increase at 130% compared to 2016. This is largely due to prominent remote code execution vulnerabilities (RCEs) and the ever increasing number of interconnected devices. The marked increase in scanning for vulnerable systems is a clear reminder to keep all internet facing systems up to date.
The year over year growth rate of ransomware alerts rose by only 37%. Although this is still an increase, it is surprisingly low compared to other financially motivated attacks, such as banking malware, which rose 113% (see Figure 2). The reason for this growth disparity can be stated with medium confidence to be due to the inherently loud nature of ransomware. Ransomware is meant to be discovered by the end user and as a result, it is fully remediated more often. Banking malware is generally treated with less drastic methods than ransomware, meaning that there is a higher chance for banking malware to reach out to its C2 hosts after initial remediation efforts.
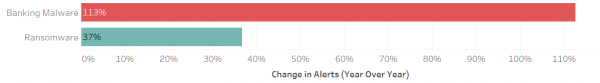
Figure 2: Change in Alerts (Year Over Year)
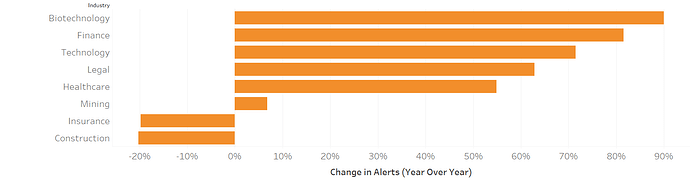
Industry Specific Analysis
The number and type of threats faced by companies varies widely depending on industry; having a view into what specific threats an industry faces allows for a more targeted defence. The biotech industry had the largest increase in year over year alerts (90%), possibly due the attractive nature of the industry for information theft. For industry specific threats, ransomware was found to most frequently target companies in the technology industry. This is likely due to a combination of poor cybersecurity posture and the criminal perception that these companies are more likely to pay a ransom, as they rely heavily on the timely delivery of technology services. Predictably, finance is the most targeted industry by banking malware. Finance saw a 375% increase in banking malware alerts, proving that despite increased regulations and a focus on cybersecurity, attackers are still drawn to these high-profile targets. The most staggering industry specific numbers are found in the fraud (phishing) category. Alerts for real estate rose 880%, retail alerts rose 529% and alerts for nonprofits rose 400%. These massive rises are attributed, with medium confidence, to a lower security awareness, meaning that individuals in these industries are more likely to fall for phishing scams, making them a more valuable target for criminals.
2018 Indicators & Warnings and Forecast Scenarios
In the beginning of January, a list of five forecasted trends for 2018 was formulated by the Threat Intelligence Team at eSentire though a combination of internal and external data.
The Threat Intelligence Team has also identified a variety of threat related scenarios that may occur over 2018; the following is an example of these scenarios paired with indicators that can be used to gage the likelihood of occurrence.
“Cyber criminals adopt machine learning to increase the scale of successful exploitations” (Autonomous Exploitation).
If there is a public release or leak of an Autonomous Exploitation (AE) toolkit or proof-of-concept (POC), the likelihood of machine learning being adopted by cyber criminals will increase. If autonomous exploitation is adapted by defenders to replicate red team operations, the likelihood for the scenario to occur decreases.
See the full report for a much more in-depth look at scenarios and indicators. The report also contains a unique analysis of threat trends, methods of compromise, malware trends, phishing developments, industry specific trends and the socio-political context driving the evolution of the global threat landscape.
Article Link: eSentire | Blog