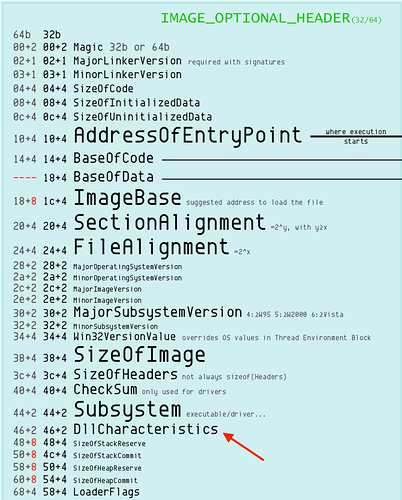
Address space layout randomization (ASLR) is a security protection the randomly arranges the address space of a process, including the base address where the PE file is loaded. This protection was first introduced to Windows OS with Vista in 2007, and though it is enabled in the OS, each PE file must opt-in to ASLR by setting the ASLR flag 0x40 in the DllCharacteristics entry in the PE IMAGE_OPTIONAL_HEADER.
All modern versions of VisualStudio will enable this setting by default by setting the /DYNAMICBASE build flag. This means that ASLR is now common in malware too!
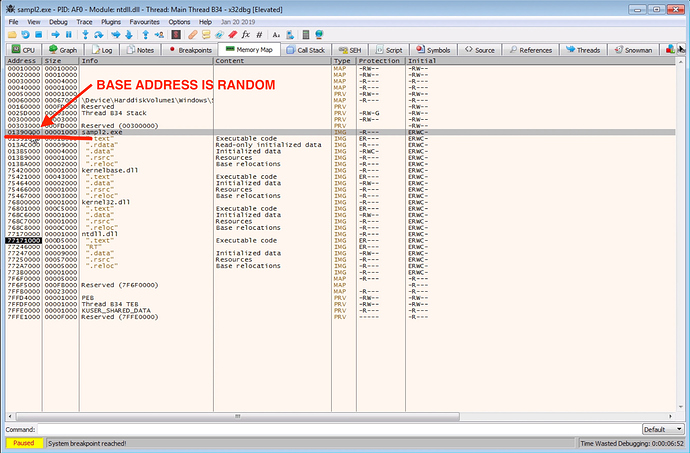
The problem with debugging ASLR enabled malware is that the base address of the PE continuously changes each time you restart the debugger. This can cause a lot of headaches if you are trying to match up addresses in IDA Pro with addresses in your debugger. IDA Pro will load the PE file using its preferred base address so this will not match with the random base address ASLR has given you in your debugger.
How To Disable ASLR
The best solution is to simply disable ASLR in your debugging VM. Simply add the registry value MoveImages to the key HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management\MoveImages and set its value to 0x00000000. After setting this registry value you will have to reboot the VM and ASLR will be disabled. After disabling ASLR the addresses in IDA should match exactly with the addresses in your debugger.
Rebase PE File in IDA Pro
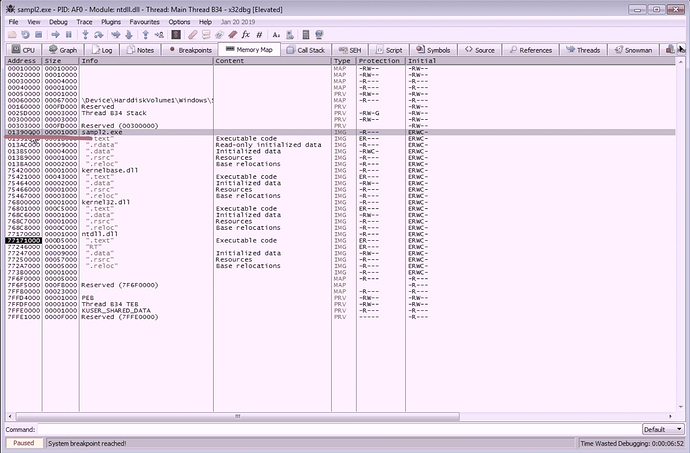
If disabling ASLR is not an option IDA has the option to rebase the loaded PE file it has disassembled. This option can be used to force the IDA addresses to match the addresses in your debugged process. First locate the base address of the PE image in the x64dbg Memory Map view.
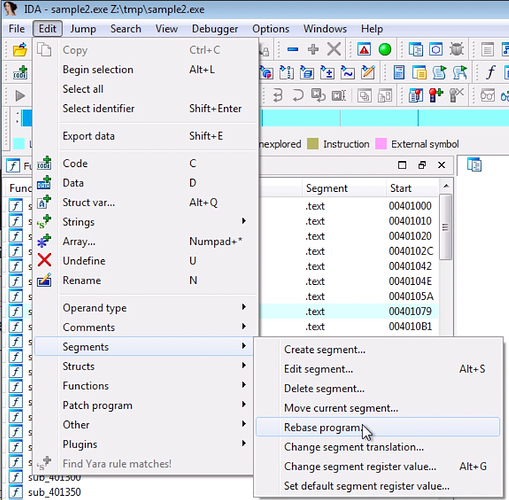
Next, in IDA select Edit->Segments->Rebase program and enter the new base address.
This will rebase the disassembled PE file so that the addresses in IDA now match up with the addresses in the debugger. The drawback to this method is that the PE must be rebased in IDA each time you restart the debugger. This is because ASLR will assign a new base address each time the process is restarted.
Article Link: https://oalabs.openanalysis.net/2019/06/12/disable-aslr-for-easier-malware-debugging/