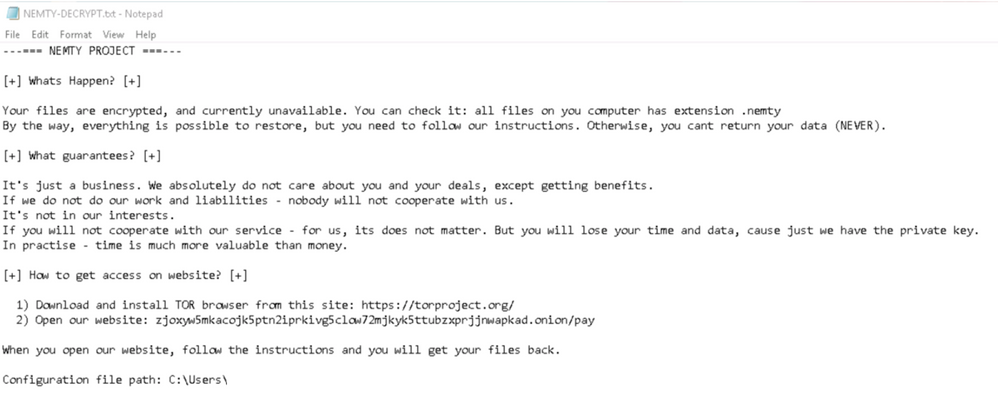
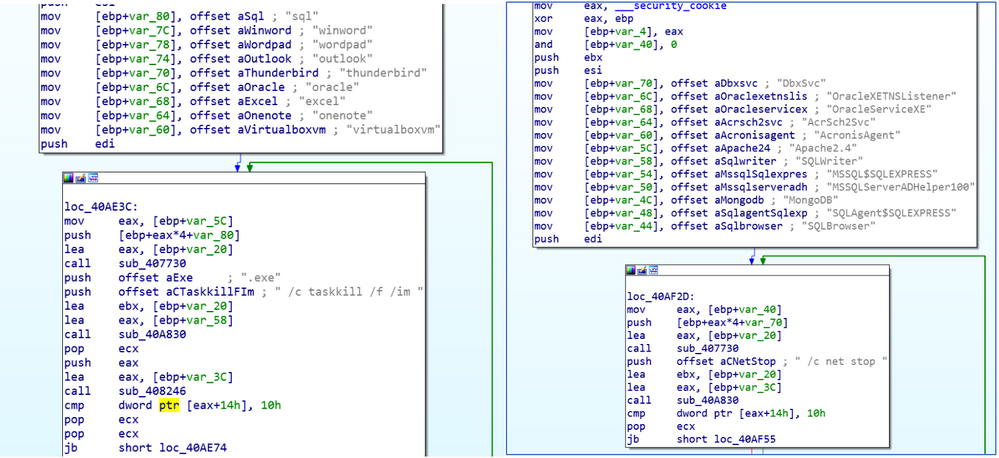
While Nemty Ransomware is distributed by various exploit kits, its behavior is similar to other variants of ransomware. It will perform “task kill” on processes to ensure the encryption of files such as databases (SQL server), perform the deletion of volume shadow copies, and disable Windows automatic startup repair to ensure all the data cannot be restored easily. After it performs file encryption, it will append “.NEMTY” as the file extension to the encrypted file and display the ransom note in Figure 1 below to the victim.
Figure 1: Screenshot of the ransom note
Figure 2: Nemty ransomware perform ‘taskkill’ and stop services of database program and other application
Nemty ransomware is blocked and detected by existing policies within Carbon Black products. To learn more about further ransomware behavior, detection and protection capabilities within the Carbon Black suite of products against Nemty ransomware, you may refer to the following blog post:
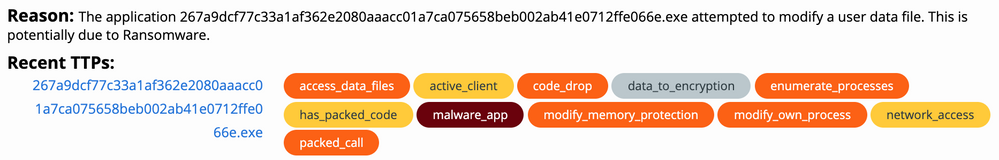
Behavioral Summary
CB Defense will display the malware’s overall triggered TTPs.
Indicators of Compromise (IOCs)
|
Indicator |
Type |
Context |
|
267a9dcf77c33a1af362e2080aaacc01a7ca075658beb002ab41e0712ffe066e 0e0b7b238a06a2a37a4de06a5ab5e615 |
SHA256 MD5 |
Nemty Ransomware |
|
505c0ca5ad0552cce9e047c27120c681ddce127d13afa8a8ad96761b2487191b 37aaba6b18c9c1b8150dae4f1d31e97d |
SHA256 MD5 |
Nemty Ransomware |
|
cb30eb1fd6d68346bcfc9bdf8b07b0724e592c7aa226ef2d860a11e6e1053b88 09f3b4e8d8246a84b55ebc7b4797f42c |
SHA256 MD5 |
Nemty Ransomware |
The post CB TAU Threat Intelligence Notification: Nemty Ransomware appeared first on Carbon Black.
Article Link: https://www.carbonblack.com/2019/10/02/cb-tau-threat-intelligence-notification-nemty-ransomware/