Inspired by a post by John Lambert and others who contributed, I've put together a table of Base64 encodings for certain file signatures and script elements often encountered in malware analysis.
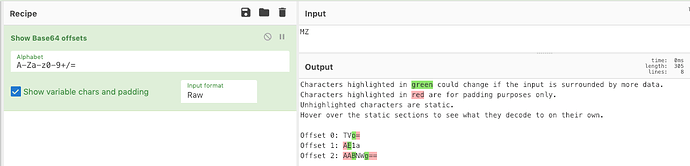
Due to the nature of Base64 encoding, there are different possibilities of the encoding result depending on the placement of the bytes in the overall structure of the blob. Using CyberChef all the possible Base64 offsets can be determined. However, in the below tables for ease I've only included the fixed bytes as if the header was at the start of the blob of Base64.
For those files that don't have a readable signature, this simple CyberChef recipe will change the hex values to display their Base64 offsets.
File Signatures
File signatures, aka 'magic bytes' or 'file headers', are static bytes that appear at the start of files.
| File Type | File Signature | Base64 Encoding |
|---|---|---|
| DOS Executable | MZ | TV |
| RAR Compressed | Rar! | UmFyI |
| JVBER | ||
| Office/Zip | PK | UE |
| Rich Text Format | {\rtf | e1xydG |
| Compound Binary File (.doc etc.) | D0 CF 11 E0 A1 B1 1A E1 | 0M8R4KGxGu |
| Gzip | 1F 8B 08 | H4sI |
Common Script Elements
These script elements are common leading commands that can be encountered during script analysis.
| Script Element | Base64 Encoding |
|---|---|
| http | aHR0c |
| $\x00 | JA |
| iex ( | aWV4IC |
| cmd.exe / | Y21kLmV4ZSAv |
| certutil | Y2VydHV0aW |
| wscript | d3Njcmlwd |
| schtasks | c2NodGFza3 |
| eval | ZXZhb |
This post was essentially to save a series of Tweets that I found useful. It is not complete and if you want to add further entries please let me know at [email protected] or @mattnotmax
References:
File headers: https://www.garykessler.net/library/file_sigs.html
Article Link: https://bitofhex.com/2019/02/19/base64-encoded-signatures/
![[base64_hex_header]](https://malware.news/uploads/default/optimized/3X/7/7/772c780ef5ac863d32f4552aba869dac486224d4_2_690x173.png)