S2W TALON
Executive Summary
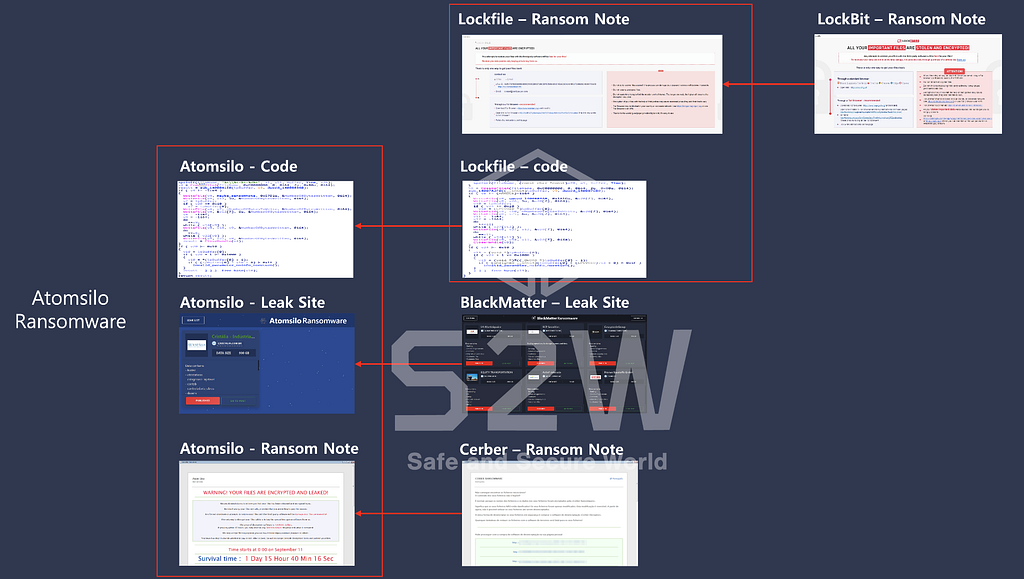
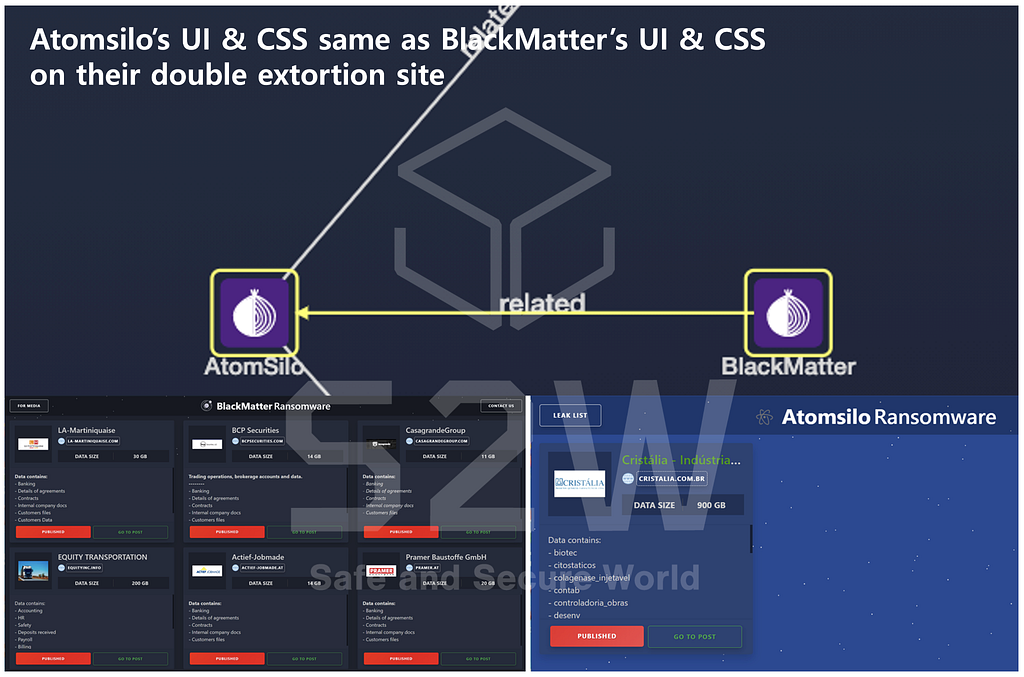
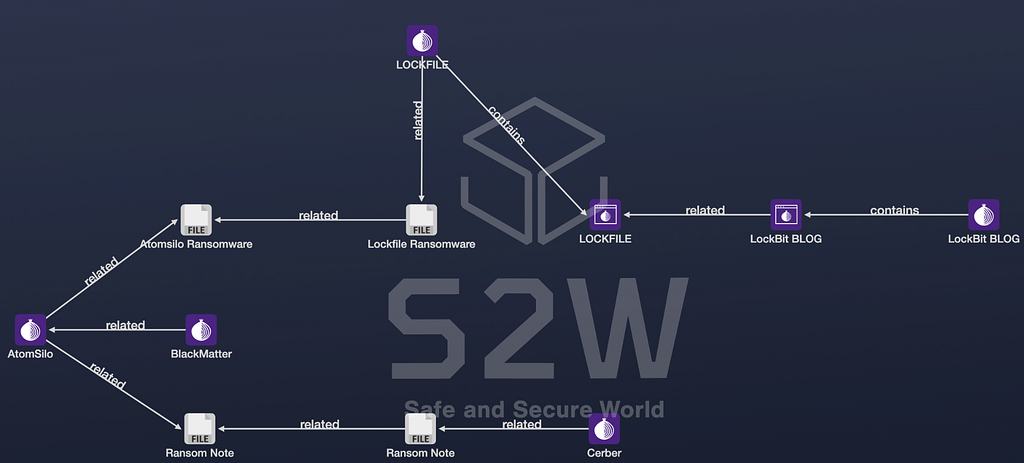
Atomsilo used the ransom note page, the double extortion site, and the malicious code of the other ransomware attack groups.
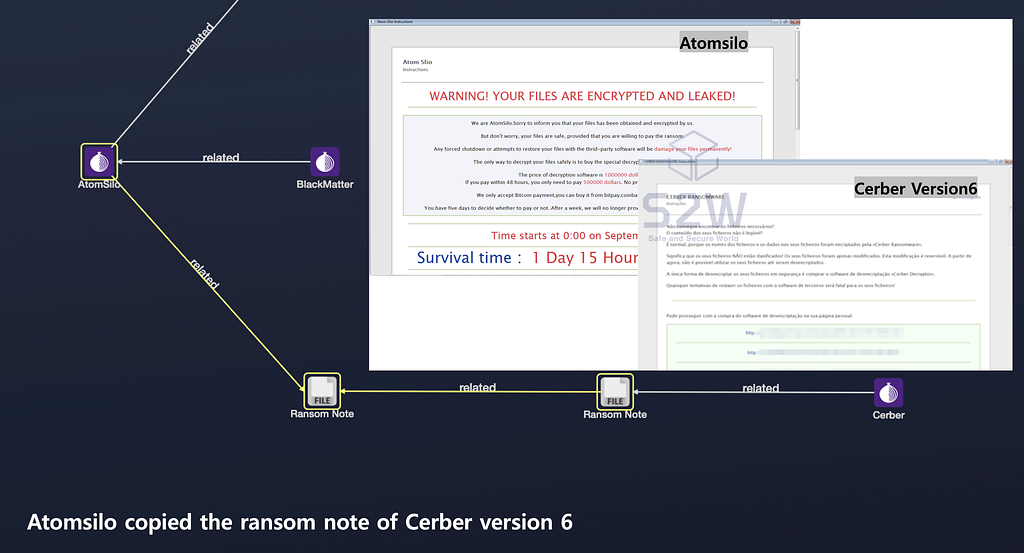
Atomsilo copied BlackMatter and Cerber version 6.
- Atomsilo copied the ransom note page of Cerber version 6.
- Atomsilo copied the double extortion site of BlackMatter.
Atomsilo used the similar malicious code to the sample of Lockfile.
- Lockfile copied the ransom note page of LockBit.
Detailed analysis
1. About Ransomware
Introduction of LockFileIntroduction of AtomsiloIntroduction of BlackMatter2. Atomsilo copied the double extortion site of BlackMatter
2.1. Compared the double extortion site
TALON Hotsauce confirmed that bootstrap.css in use is the exact same file, and site.css matches everything except the background color.
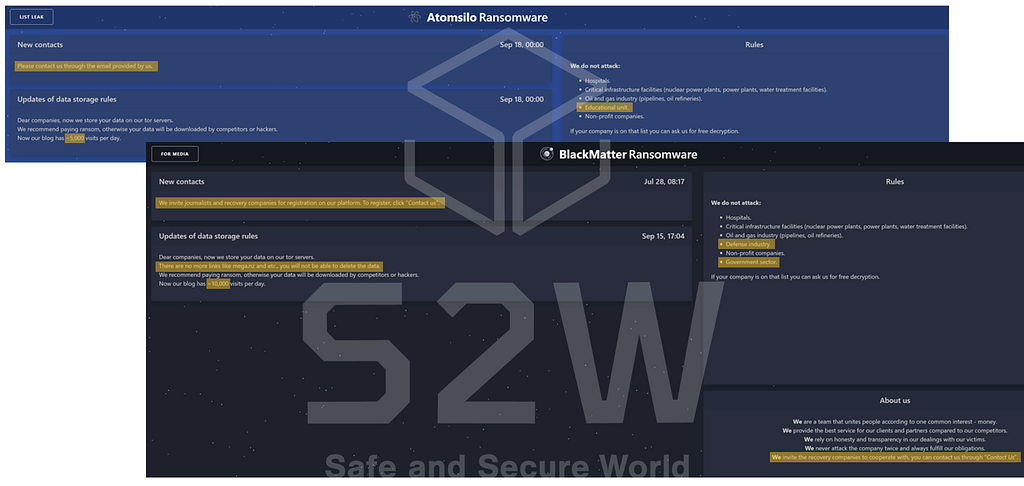
Atomsilo x BlackMatter : UI & CSSOnly a few sentences have been added or deleted, but the sentences are almost the same(Highlighted different point)
Atomsilo x BlackMatter : Atomsilo mentioned same text and contents as BlackMatter2.2. Compared the detail of CSRF
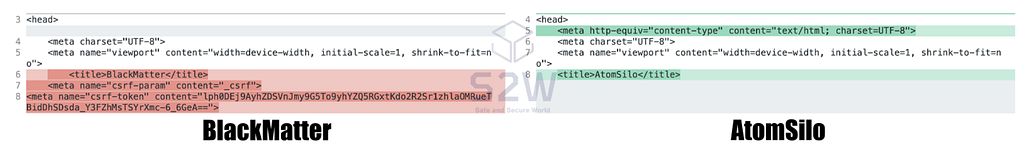
- Checked the detail of CSRF
BlackMatter generates and checks a random token to prevent CSRF, but Atomsilo analyzes that there is no CSRF token generation and verification.
If it were the same group and presumed that the server would not have opened without the CSRF token generation and verification function removed.
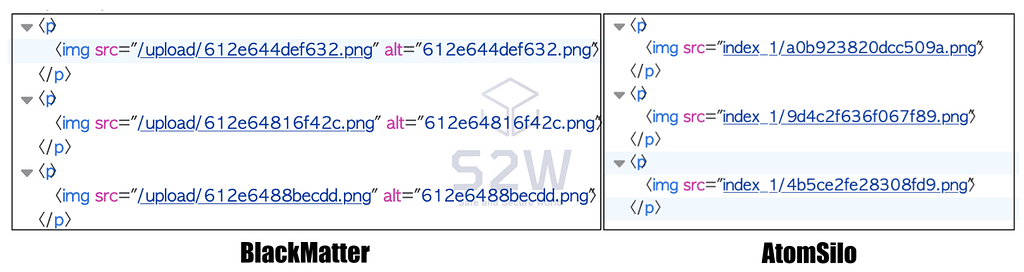
- Differences of files and archived resources structure
BlackMatter keeps all files in the upload folder, and it is presumed that the first 6 digits of the file name identify the victim company.
Atomsilo has still only one victim company, but it is estimated that files are stored by dividing folders for each victim company, and the file name is hashed to a random value and saved.
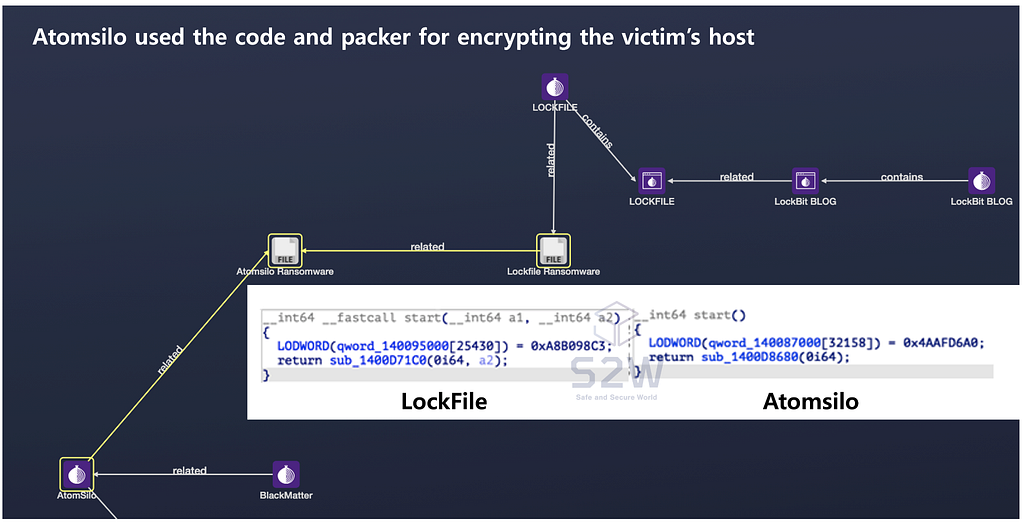
3. Atomsilo used the code and packer of LockFile
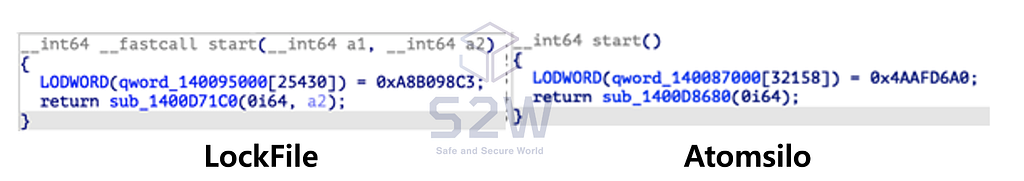
Atomsilo x LockFile : the relation of Code and packer- Lockfile and Atomsilo used the same packer.
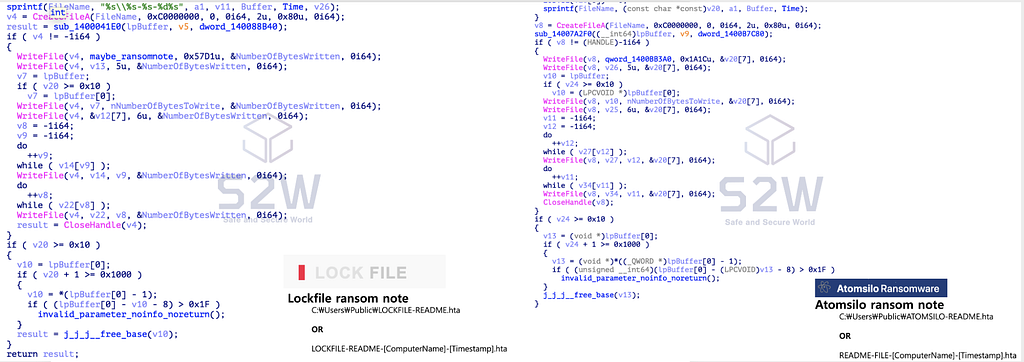
- Lockfile and Atomsilo do not create ransom notes as TXT files, but as HTA files. In this part, the code that creates the HTA file and the part that specifies the file name with the computer name are the same.
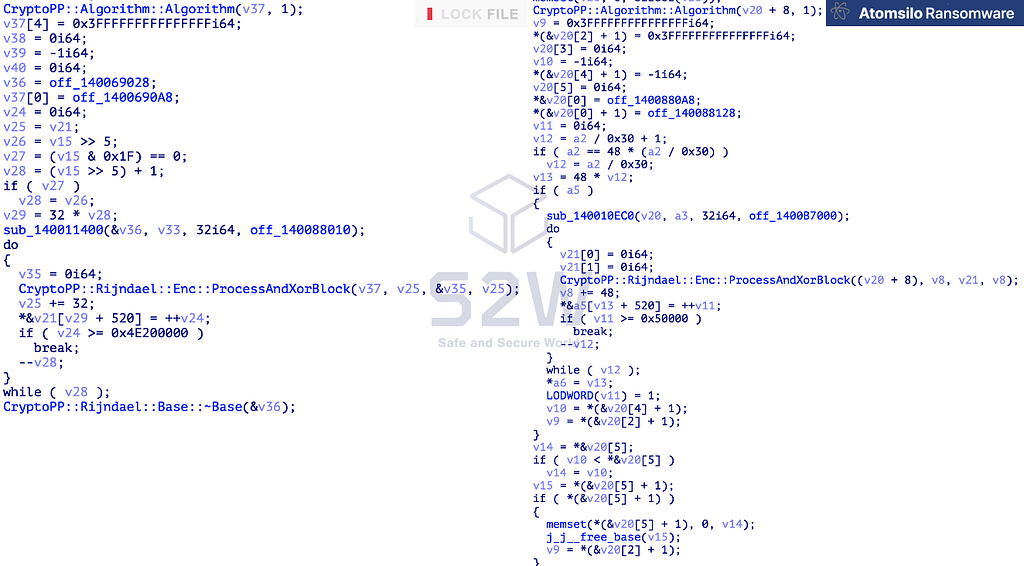
- Both Lockfile and Atomsilo encrypt files using an open source C++ encryption library called Crypto++.
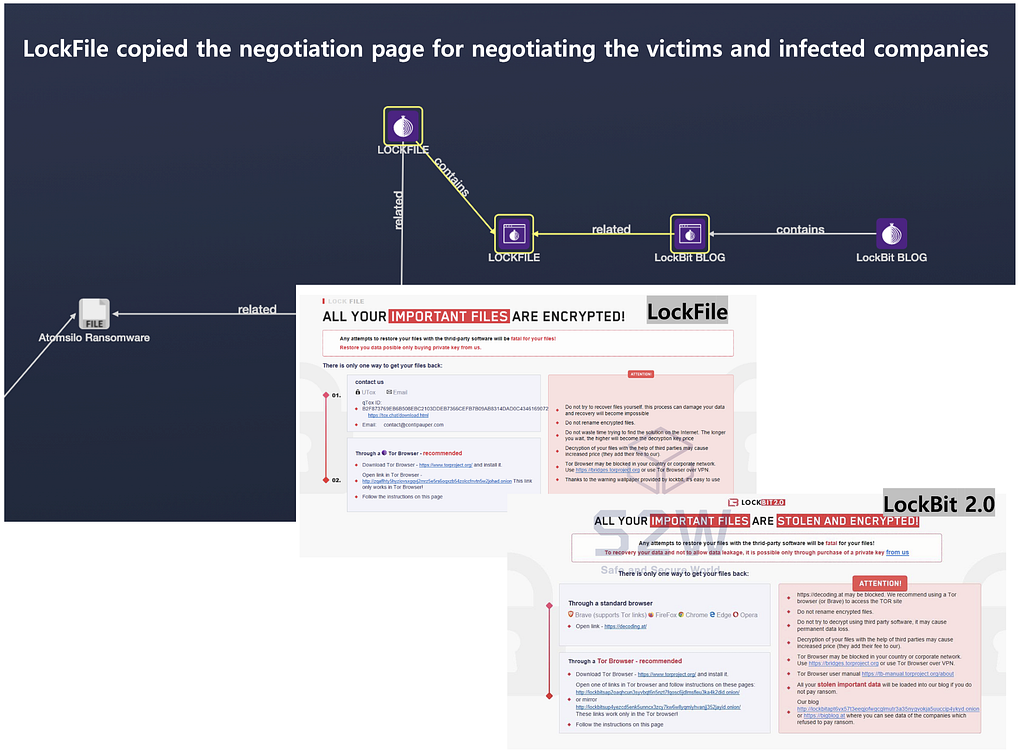
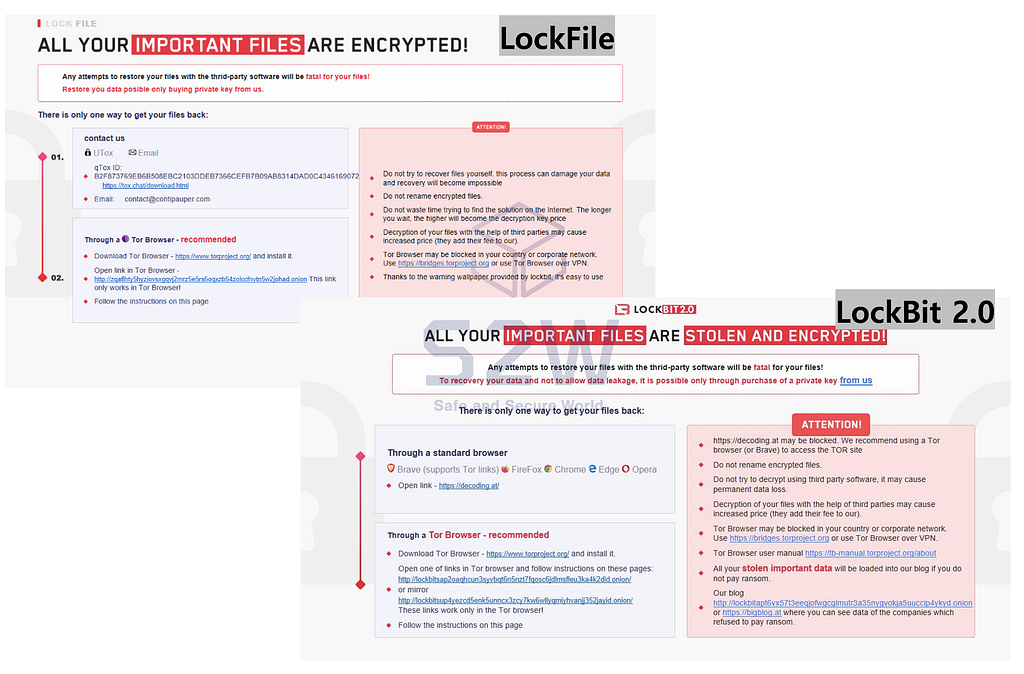
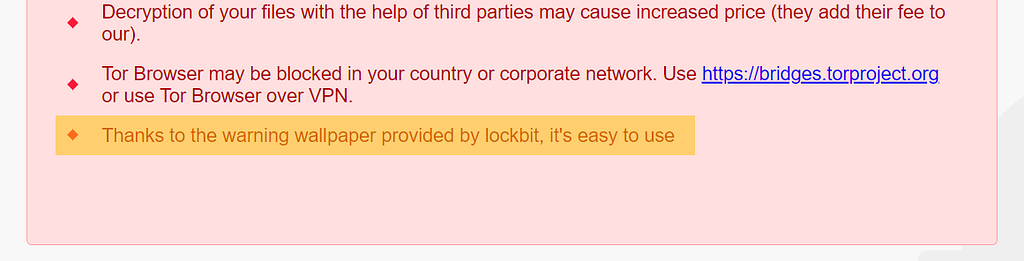
4. Lockfile copied the negotiation page of LockBit
LockFile x LockBit : the relation of negotiation pagesLockFile x LockBit : the detail of the negotiation pages- On the negotiation page of Lockfile ransomware, it was officially revealed that the UI of LockBit 2.0 was taken and used through the phrase “Thanks to the warning wallpaper provided by lockbit, it’s easy to use”.
5. Similarity of Atomsilo & Cerber Ransom note
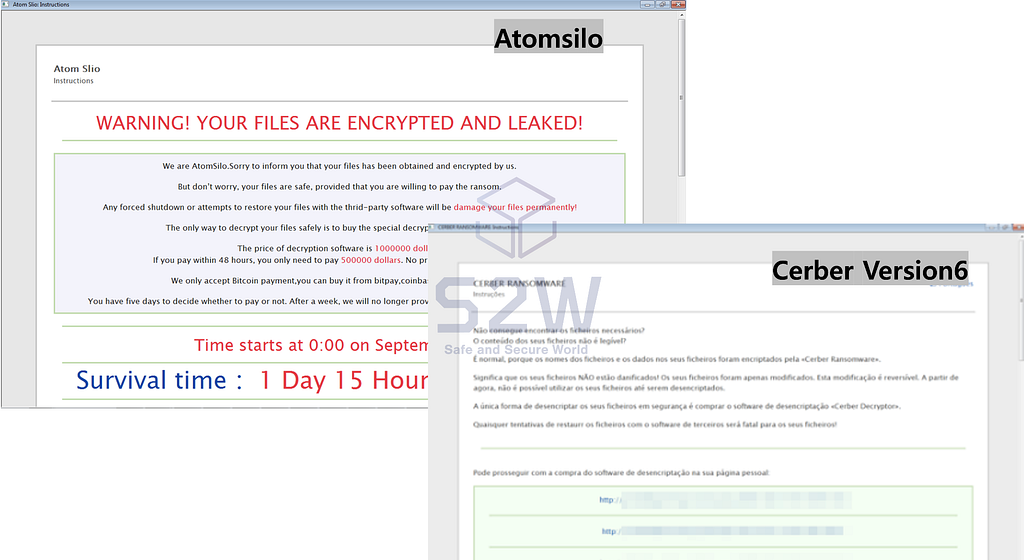
Atomsilo x Cerber version 6 : Ransom noteAtomsilo x Cerber version 6 : Atomsilo copied the same UI as Cerber Version 6Conclusion
- According to the analysis between Atomsilo and the other ransomware attack groups, Atomsilo is presumed to be a family of LockFile, and although there is a connection with BlackMatter and Cerber version6, it seems that the operation method or content is simply copied.
- Although Atomsilo is not yet an active ransomware attack group, it has copied several ransomware attack groups, so it is necessary to continuously monitor which ransomware attack group they are related to and their future activities.

- Homepage: https://www.s2w.inc
- Facebook: https://www.facebook.com/S2W
- Twitter: https://twitter.com/S2W_Official
Atomsilo x Lockfile: Atomsilo copied BlackMatter and Cerber for operating the double extortion site. was originally published in S2W BLOG on Medium, where people are continuing the conversation by highlighting and responding to this story.